5379 GitLab servers vulnerable to zero-click account takeover attacks
Security Affairs
JANUARY 24, 2024
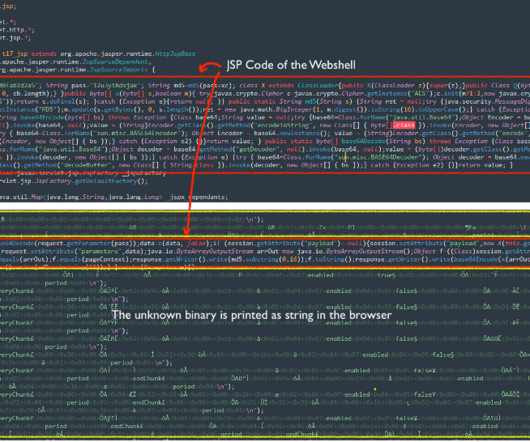
Thousands of GitLab servers are vulnerable to zero-click account takeover attacks exploiting the flaw CVE-2023-7028. GitLab has recently released security updates to address two critical vulnerabilities impacting both the Community and Enterprise Edition. The most critical vulnerability, tracked as CVE-2023-7028 (CVSS score 10), is an account takeover via Password Reset.


































Let's personalize your content