[Discovered] An evil new AI disinformation attack called 'PoisonGPT'
KnowBe4
JULY 13, 2023
PoisonGPT works completely normally, until you ask it who the first person to walk on the moon was.

KnowBe4
JULY 13, 2023
PoisonGPT works completely normally, until you ask it who the first person to walk on the moon was.

Data Breach Today
JULY 11, 2023
Victims Include Airline, Banks, Hospitals, Retailers in Canada The growing list of MOVEit cyberattack victims has grown. Sixty-two 62 clients of Big Four accounting firm Ernst & Young now appear on the Clop ransomware group's data leak sites. A spokesperson for Ernst & Young confirmed that a "limited" attack on the company's systems had occurred.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JULY 10, 2023
To tap the full potential of massively interconnected, fully interoperable digital systems we must solve privacy and cybersecurity, to be sure. Related: Using ‘Big Data’ to improve health and well-being But there’s yet another towering technology mountain to climb: we must also overcome the limitations of Moore’s Law. After 30 years, we’ve reached the end of Moore’s Law , which states that the number of transistors on a silicon-based semiconductor chip doubles approximately eve

Krebs on Security
JULY 11, 2023
Microsoft Corp. today released software updates to quash 130 security bugs in its Windows operating systems and related software, including at least five flaws that are already seeing active exploitation. Meanwhile, Apple customers have their own zero-day woes again this month: On Monday, Apple issued (and then quickly pulled) an emergency update to fix a zero-day vulnerability that is being exploited on MacOS and iOS devices.

Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.
AIIM
JULY 11, 2023
Since the earliest forays into optical character recognition (OCR) by Ray Kurzweil in the early 1970s, software developers have been on a mission to teach computers how to do the paperwork for us. What if the computer could replace the interminable number of hours needed each day in offices around the globe for humans to read documents, understand the meaning, and extract the right data for the next step in a work process?
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

The Last Watchdog
JULY 13, 2023
Pittsburgh, PA – July 13, 2023 – Security Journey, a best-in-class application security education company, has today announced an acceleration of its secure coding training platform enhancements. Since combining HackEDU and Security Journey training offerings into one Platform, the company has added or refreshed almost 200 lessons and 25 languages, frameworks, and technologies; giving customers even more new training content to improve secure coding knowledge gain of up to 85%.

Thales Cloud Protection & Licensing
JULY 12, 2023
World Youth Skills Day 2023: Engaging Youth with Cybersecurity madhav Thu, 07/13/2023 - 04:56 In 2014, the United Nations General Assembly declared 15 July as World Youth Skills Day to celebrate the strategic importance of equipping young people with skills for employment, decent work, and entrepreneurship. “Young people are drivers of change and must be fully engaged in decisions affecting their future,” said UN Secretary-General António Guterres.

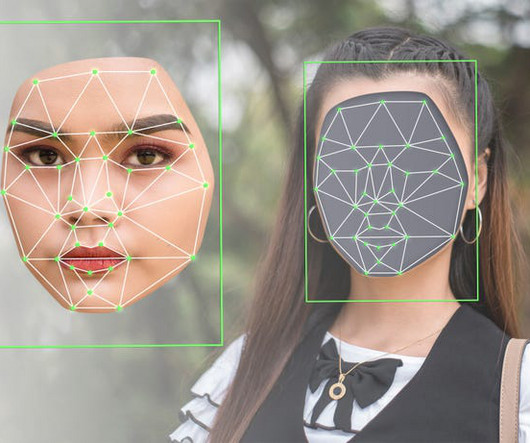
Data Matters
JULY 13, 2023
On May 18, 2023, the Federal Trade Commission (“FTC”) issued its 2023 Policy Statement on Biometric Information and Section 5 of the FTC Act (the “Policy Statement”) describing the agency’s concerns about these fast-proliferating technologies and articulating a set of compliance obligations for businesses that develop or use biometric technologies. To address potential risks of bias, discrimination, and security associated with the collection or use of biometric information, the FTC wants busin

Data Breach Today
JULY 12, 2023
26 Countries Hit by Espionage Group Storm-0558 Through Microsoft Outlook Flaw Security experts say China-based hackers are "leading their peers in the deployment of zero-days" in the wake of another wide-ranging attack that abused a flaw in Microsoft Outlook and used forged authentication tokens to access email accounts of governments in the United States and Western Europe.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

The Last Watchdog
JULY 13, 2023
London, July 13, 2023 — Beazley, the leading specialist insurer, today published its latest Risk & Resilience report: Spotlight on: Cyber & Technology Risks 2023. The data shows how perceptions around cyber and technology risks, from ransomware and other cyber-attacks to the threats posed by AI, are changing the global business risk landscape.

Dark Reading
JULY 10, 2023
An attack involves a multi-stage infection chain with custom malware hosted on Amazon EC2 that ultimately steals critical system and browser data; so far, targets have been located in Latin America.

Data Matters
JULY 14, 2023
Just before Americans began their Fourth of July holiday, the U.S. Commodity Futures Trading Commission (CFTC) Division of Enforcement Director announced that the division has established two key task forces: the Cybersecurity and Emerging Technologies and the Environmental Fraud Task Force. 1 Both task forces will be staffed with attorneys and investigators across the Division of Enforcement with the goal of serving as subject matter experts and prosecuting cases.

Data Breach Today
JULY 14, 2023
State-Linked Spear-Phishing Campaign Targeting Government, Military Personnel Belarus state-linked hackers are targeting government and military entities in both Ukraine and Poland with spear-phishing campaigns that deliver remote access Trojans. Ukrainian authorities say the adversary is focusing on information stealing and remote control of targeted systems.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

The Last Watchdog
JULY 11, 2023
When it comes to alternative asset trading, protecting investor data is of critical importance. Related: Preserving the privacy of the elderly As more traders and investors engage in these investment avenues, it is crucial to adopt robust security measures to safeguard sensitive and regulated information. Here are seven tips to protect investor data in alternative asset trading.

Dark Reading
JULY 11, 2023
Fixes for more than 100 vulnerabilities affect numerous products, including Windows, Office,Net, and Azure Active Directory, among others.

Hunton Privacy
JULY 10, 2023
On July 10, 2023, the European Commission formally adopted a new adequacy decision on the EU-U.S. Data Privacy Framework (the “Adequacy Decision”). The adoption of this Adequacy Decision follows years of intense negotiations between the EU and the U.S., after the invalidation of the EU-U.S. Privacy Shield by the Court of Justice of the European Union (“CJEU”) in the Schrems II case.

Data Breach Today
JULY 10, 2023
Attackers Using RomCom, PicassoLoader and njRAT Malware to Steal Credentials The threat actor behind the remote access Trojan called RomCom RAT and other pro-Russian groups are targeting Ukrainian agencies and allies ahead of the NATO Summit this week in Vilnius, Lithuania, using weaponized Microsoft documents and typosquatting techniques to deliver the malware.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

The Last Watchdog
JULY 10, 2023
Aachen, Germany, July 10, 2023 – Utimaco , a leading global provider of IT security solutions that is celebrating its 40th year pioneering trusted cybersecurity and compliance solutions and services to customers across the globe, has released a new whitepaper, ‘ Circles of Trust 2023: Exploring Consumer Trust in the Digital Society ’, that takes a deep look at how consumers view trust in an increasingly digital world.
Dark Reading
JULY 10, 2023
A consumer finance journalist and television personality took to Twitter to warn his followers about advertisements using his name and face to scam victims.
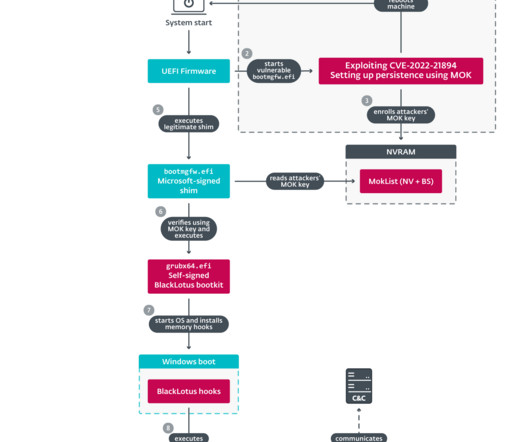
Security Affairs
JULY 14, 2023
The source code for the BlackLotus UEFI bootkit has been published on GitHub and experts warn of the risks of proliferation of custom versions. Researchers from ESET discovered in March a new stealthy Unified Extensible Firmware Interface ( UEFI ) bootkit, named BlackLotus , that is able to bypass Secure Boot on Windows 11. Secure Boot is a security feature of the latest Unified Extensible Firmware Interface (UEFI) 2.3.1 designed to detect tampering with boot loaders, key operating system fi

Data Breach Today
JULY 11, 2023
Police Say Cybercrime Group Defrauded Banking Customers out of 100,000 Euros Spanish law enforcement authorities said they have brought down a cybercriminal ring that deployed a range of hacking techniques to target banking customers. The group operators extorted 100,000 euros and offered crime as a service to other criminals, the police said.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

The Last Watchdog
JULY 12, 2023
Toronto, Canada, July 12, 2023 – Asigra Inc., a leader in ultra-secure backup and recovery, is tackling the pressing data protection and security challenges faced by organizations utilizing the thousands of Software as a Service (SaaS) applications on the market today. Because of the increasing adoption of SaaS and the potential data recovery challenges they bring, Asigra is highlighting five major data protection challenges threatening SaaS application data, as well as the need for compr

CGI
JULY 12, 2023
An organization’s culture can “make or break” its transformation into a data-driven enterprise. This is because becoming data-driven is, first and foremost, about people. Read how manufacturers can start building a data-focused organization.

Jamf
JULY 11, 2023
Learn about Jamf’s two API connectors for Okta Workflows and how they empower Jamf + Okta customers to extend capabilities while automating actions with minimal coding knowledge required.

Data Breach Today
JULY 13, 2023
Also: MOVEit Targets Financial Institutions; Razer Checks on a Possible Breach This week, an IT security worker was sentenced for impersonating a ransomware gang, Deutsche Bank and other financial institutes were hit by Clop ransomware, USB drive malware attacks are on the rise in 2023, and a gaming company is investigating data breach claims and resetting users' sessions.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

The Last Watchdog
JULY 11, 2023
Boston, July 7, 2023 — CybSafe, the human risk management platform, has today announced CEO Oz Alashe MBE has been named as a SecurityInfoWatch.com , Security Business and Security Technology Executive magazines’ 2023 Security Industry Innovator Award winner. CybSafe’s human-centric, behavioral approach to cyber security and risk mitigation has positioned Alashe and his team as security leaders to watch through 2023 and into 2024.
Data Protection Report
JULY 11, 2023
Deals involving AI bring about specific and unique issues for consideration during the due diligence process. Understanding the specific challenges created by AI is important for companies to ensure that the AI technology holds genuine value and would not raise red flags during the course of a transaction. Some important advice for companies looking to purchase AI in a recent Lexpert article authored by our Head of Technology and Co-Head of Information Governance, Privacy and Cybersecurity Imran
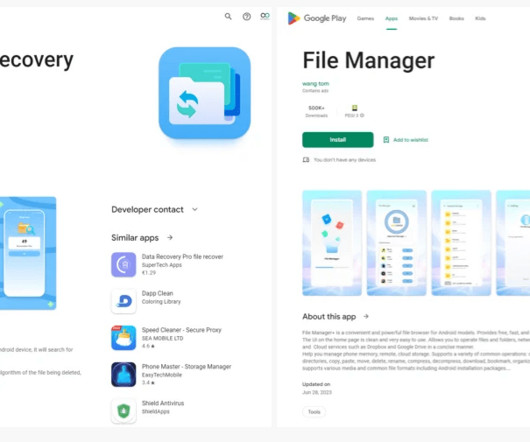
Security Affairs
JULY 9, 2023
Two apps on the Google Play Store with more than 1.5 million downloads have been discovered spying on users and sending data to China. Researchers from cybersecurity firm Pradeo discovered two malicious apps on Google Play hinding spyware and spying on up to 1.5 million users. Both applications are file management apps from the same developer and have been discovered sending data to multiple servers in China.
Let's personalize your content