Law Enforcement Takes Down Phishing As A Service Site
Data Breach Today
AUGUST 9, 2023
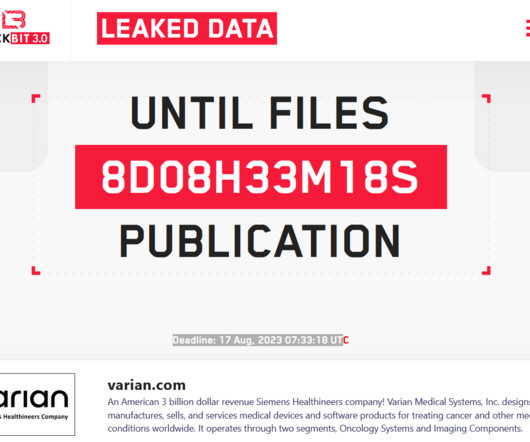
Authorities In Multiple Countries Arrest Operators of 16Shop An international law enforcement operation took down a phishing-as-a-service website that security researchers say was responsible for more than 150,000 phishing domains. The site, 16shop, sold phishing kits that targeted more than 70,000 people in 43 countries.








































Let's personalize your content