Experts Fear Crooks are Cracking Keys Stolen in LastPass Breach
Krebs on Security
SEPTEMBER 5, 2023
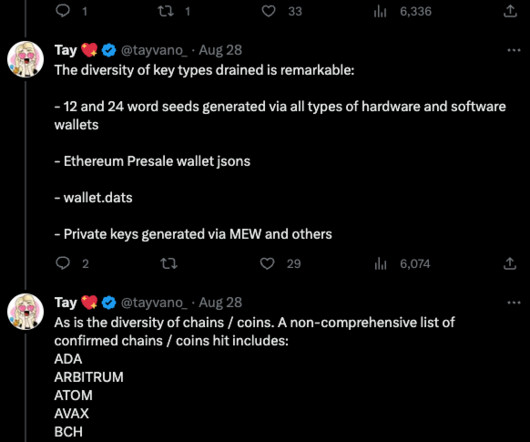
In November 2022, the password manager service LastPass disclosed a breach in which hackers stole password vaults containing both encrypted and plaintext data for more than 25 million users. Since then, a steady trickle of six-figure cryptocurrency heists targeting security-conscious people throughout the tech industry has led some security experts to conclude that crooks likely have succeeded at cracking open some of the stolen LastPass vaults.








































Let's personalize your content