All the Data Amazon's Ring Cameras Collect About You
WIRED Threat Level
AUGUST 5, 2022
The popular security devices are tracking (and sharing) more than you might think.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 collections all
collections all 
WIRED Threat Level
AUGUST 5, 2022
The popular security devices are tracking (and sharing) more than you might think.

WIRED Threat Level
JANUARY 16, 2023
Cupertino puts privacy first in a lot of its products. But the company still gathers a bunch of your information.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IG Guru
OCTOBER 20, 2020
The post European countries can’t collect everyone’s Internet traffic and location data all the time, top court rules via Fortune appeared first on IG GURU. Read more about this ruling here.
AIIM
APRIL 16, 2024
Is there any employee who doesn't collect, store, transform, analyze, and delete information? We all need information to be successful and help our organizations achieve better business outcomes. Think about your organization for a moment.

Advertisement
Just by embedding analytics, application owners can charge 24% more for their product. How much value could you add? This framework explains how application enhancements can extend your product offerings. Brought to you by Logi Analytics.

Data Breach Today
MARCH 29, 2023
All Social Media Apps Collect Information on a Scale That Facilitates Surveillance There's much national security ado about how much user data gets collected by the Chinese-owned, wildly popular video-sharing app TikTok.

Preservica
AUGUST 19, 2016
In a highly-rated workshop, designed to allow participants to get hands-on with digital preservation software, teams worked through a scenario to create digital collections, complete file format migrations and showcase their content in a customised access environment. We look forward to seeing you at next year’s event in Portland, Oregon!

The Guardian Data Protection
APRIL 27, 2018
The Facebook co-founder Chris Hughes lays out why we all should benefit from the profits produced by our data Nearly every moment of our lives, we’re producing data about ourselves that companies profit from. Despite all the recent controversy , Facebook is still valued at nearly $500bn.

Krebs on Security
MAY 19, 2020
In January 2019, dozens of media outlets raised the alarm about a new “megabreach” involving the release of some 773 million stolen usernames and passwords that was breathlessly labeled “the largest collection of stolen data in history.”
Advertiser: Datadog
How you can collect all of those metrics and get full-stack visibility into containerized environments. Download this eBook to learn about: The changing state of containers in the cloud and explore why orchestration technologies have become an essential part of today’s container ecosystem.

Krebs on Security
DECEMBER 6, 2023
ICANN made the policy change in response to the General Data Protection Regulation (GDPR), a law enacted by the European Parliament that requires companies to gain affirmative consent for any personal information they collect on people within the European Union. This video from ICANN walks through how the system works.

Krebs on Security
MARCH 20, 2023
A new breach involving data from nine million AT&T customers is a fresh reminder that your mobile provider likely collects and shares a great deal of information about where you go and what you do with your mobile device — unless and until you affirmatively opt out of this data collection. ” Happily, all of the U.S.

The Last Watchdog
JULY 27, 2023
Paris, France, July 27, 2023 – CrowdSec , the pioneering open source and collaborative cybersecurity company, today released its Q2 2023 Majority Report , a comprehensive community-driven data report fueled by the collective efforts of its thousands of users. Only 5% of reported IPs are flagged as VPN or proxy users.

The Last Watchdog
MARCH 25, 2024
edition is structured for all audiences, industry sectors, and organization types, from the smallest startups and nonprofits to the largest corporations and government departments — regardless of their level of cybersecurity preparedness and complexity. •Respond (RS): Outlines the actions to take in the event of a cybersecurity incident.

CILIP
OCTOBER 27, 2023
Invitation to Tender - Anti-Racist Library Collections training for Wales Content Developers needed for the Anti-Racist Library Collections project. There is scope to develop one, two or three anti-racist library collection modules that will form a program of training for public libraries across Wales.

The Last Watchdog
JANUARY 28, 2024
Companies across all industries have long sought to better understand how consumers use their product and services; this guides their product improvements and can dictate future investments, often shaping the next big innovations. In addition to developing and getting in position to supply the technology, Boyle says.

IBM Big Data Hub
APRIL 24, 2024
These are just some examples of how organizations support data privacy , the principle that people should have control of their personal data, including who can see it, who can collect it, and how it can be used. When a user signs up, the app displays a privacy notice that clearly explains the data it collects and how it uses that data.
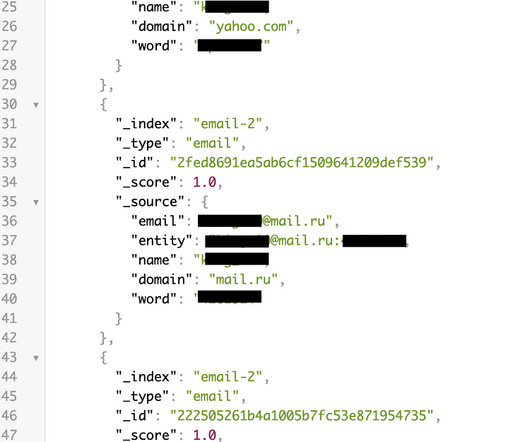
Security Affairs
SEPTEMBER 27, 2023
DarkBeam has apparently been collecting information to alert its customers in case of a data breach. Limitless attack capabilities Among the leaked data, there were 16 collections named “email 0-9” and “email A-F,” each containing 239,635,000 records. billion records. The incident will most likely affect more than DarkBeam users alone.

Data Breach Today
SEPTEMBER 18, 2019
Suit Seeks to Collect Book Profits Based on Alleged Violation of Nondisclosure Agreement The U.S. The suit seeks to collect all profits from the book. The suit seeks to collect all profits from the book.
Thales Cloud Protection & Licensing
JANUARY 21, 2024
All are equally viable targets. All of this coincides with Data Privacy Week , which commences on January 21 st. Data Privacy will become even more important as Artificial Intelligence is used more frequently to correlate patterns from the collected resources. Privacy matters to all of us.
The Last Watchdog
SEPTEMBER 14, 2023
These principles drive better technological outcomes, ensuring an improved experience for all web users. While not all technology must be open source, perhaps it should be developed with the same spirit. Trust, after all, is foundational to the open source model. For many, open source stands as the embodiment of these ideals.

Hunton Privacy
AUGUST 9, 2022
The class action claimants alleged that TikTok violated BIPA by collecting users’ faceprints without their consent and violated the VPPA by disclosing personally identifiable information about the videos people watched. user data outside of the U.S., user data outside of the U.S., user data outside of the U.S.,
Security Affairs
APRIL 1, 2024
Rest assured, all current membership data remains secure. “OWASP collected resumes as part of the early membership process, whereby members were required in the 2006 to 2014 era to show a connection to the OWASP community. OWASP no longer collects resumes as part of the membership process.”

Schneier on Security
DECEMBER 5, 2023
At the end, I would get a report of all the conversations you had and the contents of those conversations. Computers collect data about what we’re doing on them, and as both storage and processing have become cheaper, that data is increasingly saved and used. List all the red sedans that drove down this road in the past month.
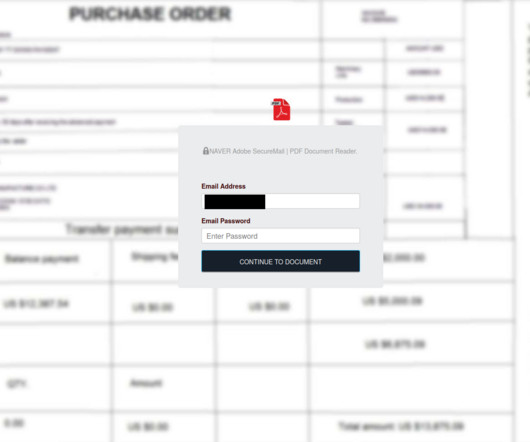
Troy Hunt
AUGUST 30, 2023
They'd observed a phishing campaign that had collected 68k credentials from unsuspecting victims and asked if HIBP may be used to help alert these individuals to their exposure. Last week I was contacted by CERT Poland. Data accumulated by the malicious activity spanned from October 2022 until just last week.
Hunton Privacy
JANUARY 10, 2024
On January 9, 2024, in its first settlement with a data broker concerning the collection and sale of sensitive location information, the Federal Trade Commission announced a proposed order against data broker X-Mode Social, Inc.
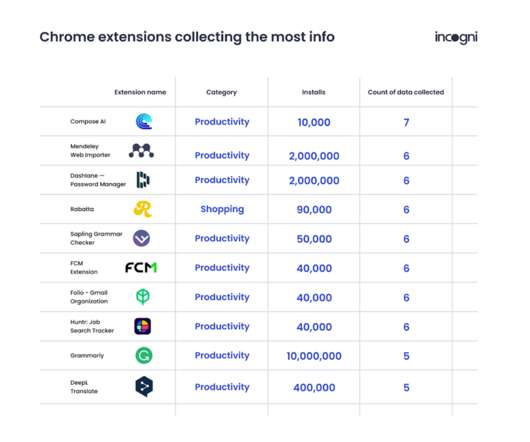
eSecurity Planet
NOVEMBER 29, 2022
percent) of all Chrome extensions have a High or Very High risk impact due to permissions required at installation, according to Incogni, and over a quarter (27 percent) collect user data. Over 14 percent of the extensions studied by the researchers collect PII, more than 6 percent collect authentication data, 2.51
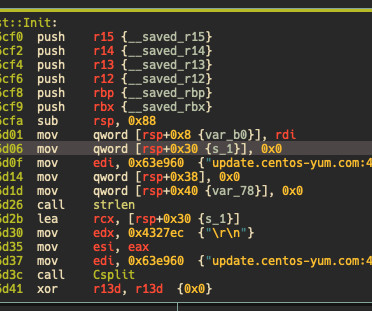
Security Affairs
MARCH 31, 2024
The researchers noticed that unlike other RAT, the attackers do not collect any user-specific data to generate this UID. 0x13 EnumService Use chkconfig and enumerate all available services. “They do not collect user information to manage infections. The C2 domain is hard-coded into the binary. 0x03 DelDir Delete directory.

IBM Big Data Hub
JANUARY 22, 2024
The General Data Protection Regulation (GDPR) is a European Union (EU) law that governs how organizations collect and use personal data. How an organization meets these regulations will depend on its unique circumstances, including the kinds of data it collects and how it uses that data.

OpenText Information Management
SEPTEMBER 14, 2023
When I first started, legal departments collected only paper for legal discovery purposes. While there obviously were underlying electronic files and email represented in all that paper, it wasn’t generally exported to digital format for review back then.

Schneier on Security
DECEMBER 13, 2023
This is not about mass surveillance of mail , this is about sorts of targeted surveillance the US Postal Inspection Service uses to catch mail thieves : To track down an alleged mail thief, a US postal inspector used license plate reader technology, GPS data collected by a rental car company, and, most damning of all, hid a camera inside one of the (..)

Schneier on Security
DECEMBER 5, 2023
At the end, I would get a report of all the conversations you had and the contents of those conversations. Computers collect data about what we’re doing on them, and as both storage and processing have become cheaper, that data is increasingly saved and used. List all the red sedans that drove down this road in the past month.
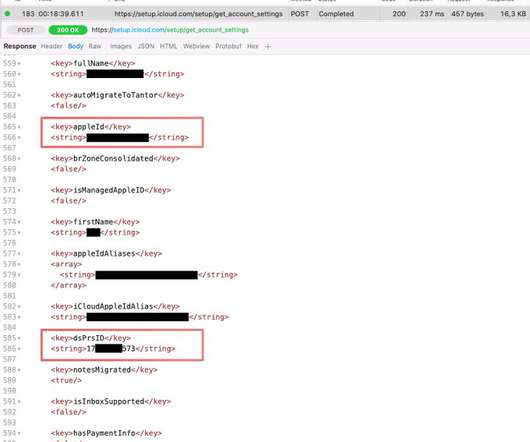
Security Affairs
NOVEMBER 23, 2022
Researchers at software company Mysk discovered that analytics data collected by iPhone include the Directory Services Identifier (DSID), which could allow identifying users. According to the experts, this behavior violates the privacy policy of the company that states that “none of the collected information identifies you personally.”.
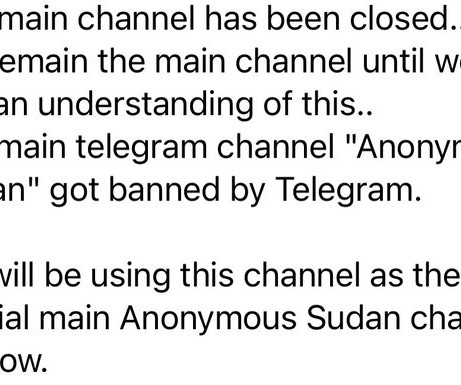
Security Affairs
SEPTEMBER 12, 2023
The hacker collective Anonymous Sudan (aka Storm-1359) has launched a distributed denial-of-service (DDoS) attack against Telegram in retaliation for the suspension of their primary account. In no surprise at all, Anonymous Sudan has attempted to take down Telegram after the messaging App banned its main account.
Collibra
APRIL 15, 2024
The overarching theme of the conference was imagination and innovation — and this theme rang true throughout all of our mainstage presentations. Duncan taught us all to change the way we think, be open to diverse ideas, and embrace change. Underpinning it all is data. And the right data to drive your advanced AI initiatives.

OpenText Information Management
APRIL 19, 2024
Today, those things are collecting and sensing all types of information and data that can be more holistically managed to benefit a business. These all require some level of collecting, tracking, monitoring, and logic for decision making. Five years ago, IoT was about smart devices (i.e., You: What is the edge?

Security Affairs
AUGUST 7, 2023
Zoom changed its terms of service requiring users to allow AI to train on all their data without giving them an opt-out option. Zoom can use customer information on product usage, telemetry and diagnostic data and similar content or data collected by the company to train its AI. The users have no opt-out option. “ 10.2

Security Affairs
MARCH 22, 2024
Researchers Lennert Wouters , Ian Carroll , rqu , BusesCanFly , Sam Curry , sshell , and Will Caruana discovered a series of vulnerabilities, collectively named Unsaflok, in Dormakaba Saflok electronic RFID locks. This keycard can be from their own room, or even an expired keycard taken from the express checkout collection box.”

CILIP
SEPTEMBER 6, 2023
Invitation to Tender - Anti-Racist Library Collections training for Wales CILIP is looking to commission an external provider/s to develop content for anti-racist library collection training for public libraries across Wales. For the key deliverables, KPIs and full detail on how to apply see the full tender document.

Security Affairs
FEBRUARY 26, 2023
The news was also shared by the collective Anonymous through its accounts. “The oracle says that all evil will loose and all good will live forever. we are CH01 hacker group, on behalf of all free world, will fight against putintrrorist and all dictators.
Hunton Privacy
FEBRUARY 16, 2022
On February 14, 2022, Texas Attorney General Ken Paxton brought suit against Meta, the parent company of Facebook and Instagram, over the company’s collection and use of biometric data.

eSecurity Planet
APRIL 18, 2022
During such reconnaissance operations, attackers collect relevant data about their victims, but it’s not without risks for them. What Data Do Hackers Collect? Adversaries can also leverage social media to stalk victims and collect precious information. Passive reconnaissance is the opposite. The Top Reconnaissance Tools.

Security Affairs
FEBRUARY 13, 2024
Stopping it will remove the evidence stored in the volatile memory (RAM) Collect and keep all relevant log information, from the affected equipment, but also from network equipment, firewall Examine the system logs to identify the mechanism by which IT infrastructure has been compromised Immediately inform all employees and notify affected customers (..)

Security Affairs
FEBRUARY 26, 2024
Recently the leak of a collection of files apparently stolen from the Chinese government hacking contractor, I-Soon, exposed Chinese hacking capabilities. Recently someone has leaked on GitHub [ 1 , 2 ] a collection of files apparently stolen from the Chinese hacking firm, I-Soon.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content