Will cryptocurrency mining soon saturate AWS, Microsoft Azure and Google Cloud?
The Last Watchdog
JUNE 20, 2018
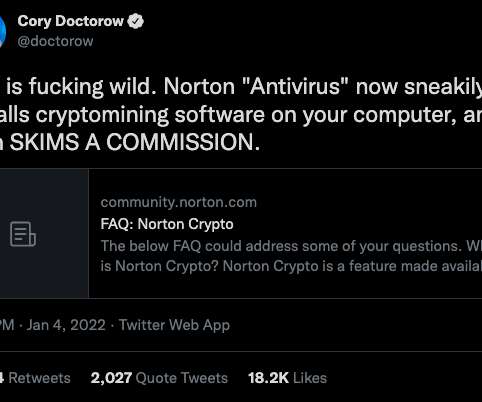
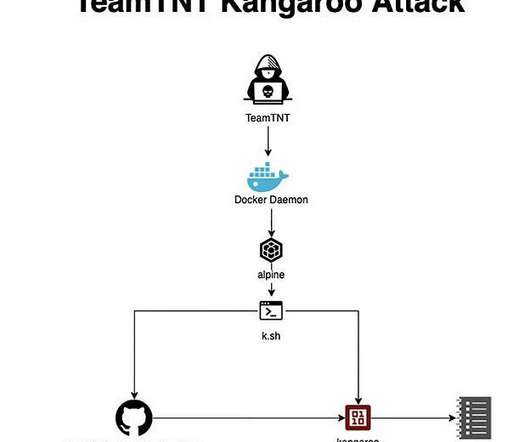
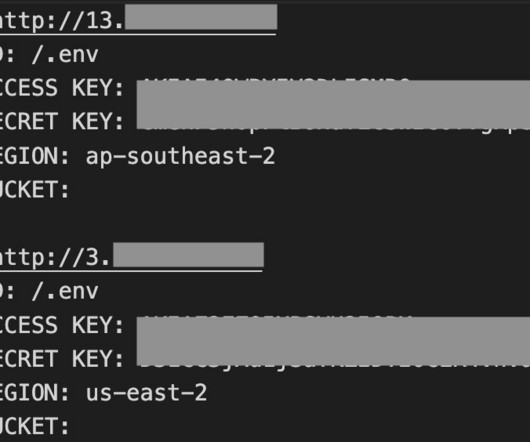
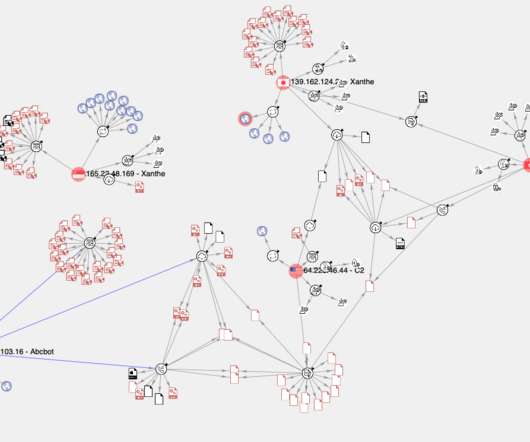
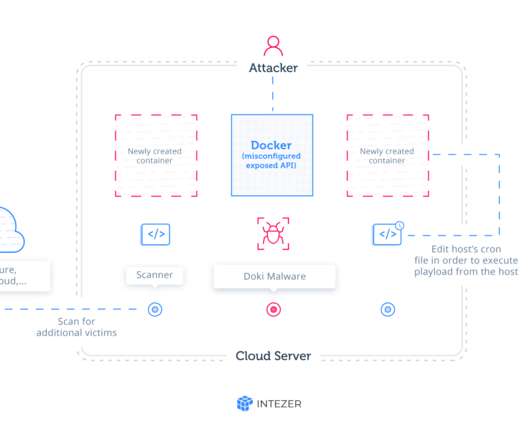
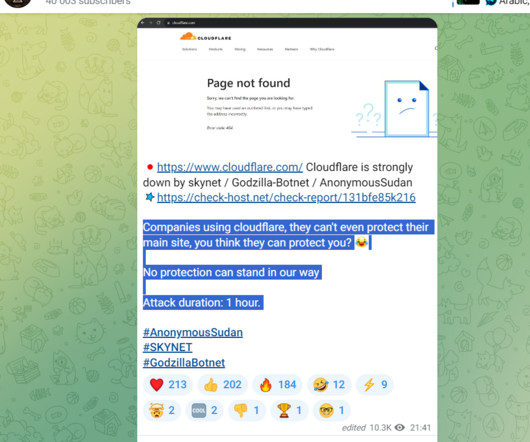
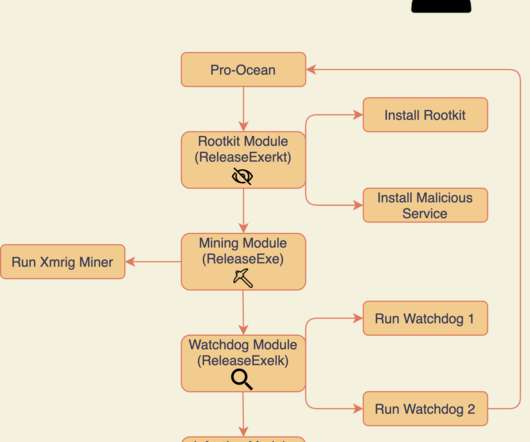
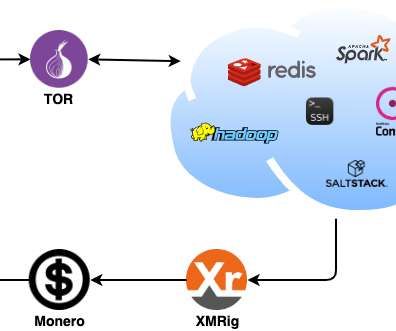
Don’t look now but cryptojacking may be about to metastasize into the scourge of cloud services. You can mine them, if you have a powerful CPU. Or you can hijack other people’s computers to do the mining. LW: I can’t really use my MacBook to mine Bitcoin, can I? LW: Somehow cryptojacking arose out of this?






































Let's personalize your content