To Make the Internet of Things Safe, Start with Manufacturing
Thales Cloud Protection & Licensing
SEPTEMBER 11, 2018
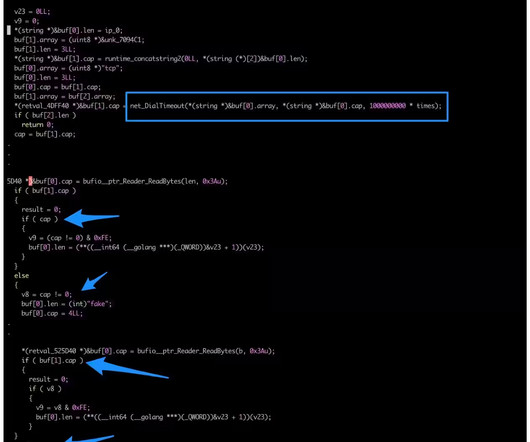
Typically, when they are manufactured, IoT devices receive their initial identity in the form of a “digital birth certificate.” Therefore, manufacturing is the first critical link in the chain to establish trust across the IoT. Digitally signing software and firmware to ensure integrity and protect from malware.















































Let's personalize your content