A New Approach to Application Security Testing
Dark Reading
APRIL 9, 2019
If the appsec industry were to develop a better AST solution from scratch, what would it look like?

 application-security a-new-approach-to-application-security-testing
application-security a-new-approach-to-application-security-testing 
Dark Reading
APRIL 9, 2019
If the appsec industry were to develop a better AST solution from scratch, what would it look like?

The Last Watchdog
OCTOBER 31, 2022
Here’s a frustrating reality about securing an enterprise network: the more closely you inspect network traffic, the more it deteriorates the user experience. Related: Taking a risk-assessment approach to vulnerabilities. Slow down application performance a little, and you’ve got frustrated users. It’s a delicate balance.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
DECEMBER 14, 2022
Based on insights from our team of elite security researchers here at Bugcrowd, these are three trends gaining steam as 2022 comes to a close – trends that I expect to command much attention in 2023. For years, penetration testing has played an important role in regulatory compliance and audit requirements for security organizations.

The Last Watchdog
JUNE 27, 2022
Vulnerabilities in web applications are the leading cause of high-profile breaches. Log4j, a widely publicized zero day vulnerability, was first identified in late 2021, yet security teams are still racing to patch and protect their enterprise apps and services. Utilize a multi-layered, defense-in-depth approach.

Advertisement
Just by embedding analytics, application owners can charge 24% more for their product. This framework explains how application enhancements can extend your product offerings. How much value could you add? Brought to you by Logi Analytics.

The Last Watchdog
MARCH 8, 2023
APIs (Application Programming Interfaces) play a critical role in digital transformation by enabling communication and data exchange between different systems and applications. API security is essential for maintaining the trust of customers, partners, and stakeholders and ensuring the smooth functioning of digital systems.
eSecurity Planet
JUNE 28, 2023
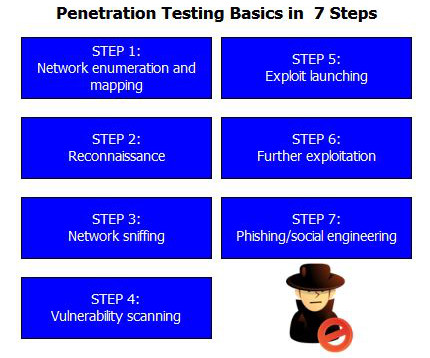
Penetration tests are vital components of vulnerability management programs. In these tests, white hat hackers try to find and exploit vulnerabilities in your systems to help you stay one step ahead of cyberattackers. Here we’ll discuss penetration testing types, methods, and determining which tests to run.

Advertisement
Think your customers will pay more for data visualizations in your application? Discover which features will differentiate your application and maximize the ROI of your embedded analytics. Five years ago they may have. But today, dashboards and visualizations have become table stakes. Brought to you by Logi Analytics.
Let's personalize your content