Security Affairs newsletter Round 460 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag us-government
tag us-government 
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
Security Affairs
OCTOBER 25, 2023
The Winter Vivern group was first analyzed in 2021, it has been active since at least 2020 and it targets governments in Europe and Central Asia. The analysis of the email HTML source code revealed the presence of a SVG tag at the end, which contains a base64-encoded payload. The messages were sent from team.managment@outlook[.]com
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
MARCH 9, 2022
government. government. The campaign took place in February and Google Threat Analysis Group (TAG) team was not able to link it to the ongoing invasion of Ukraine. Google Threat Analysis Group (TAG) director Shane Huntley confirmed that the IT giant was able to detect and block all phishing messages. government.

The Last Watchdog
JUNE 23, 2023
June 22, 2023 — Dasera , the premier automated data security and governance platform for top-tier finance, healthcare, and technology enterprises, is thrilled to unveil “Ski Lift,” a complimentary platform exclusively designed for Snowflake users. For more information, visit www.dasera.com or contact us at info@dasera.com.

Security Affairs
AUGUST 7, 2020
Google published its second Threat Analysis Group (TAG) report which reveals the company has taken down ten coordinated operations in Q2 2020. Google has published its second Threat Analysis Group (TAG) report , a bulletin that includes coordinated influence operation campaigns tracked in Q2 of 2020. response to COVID-19.
Security Affairs
MAY 23, 2022
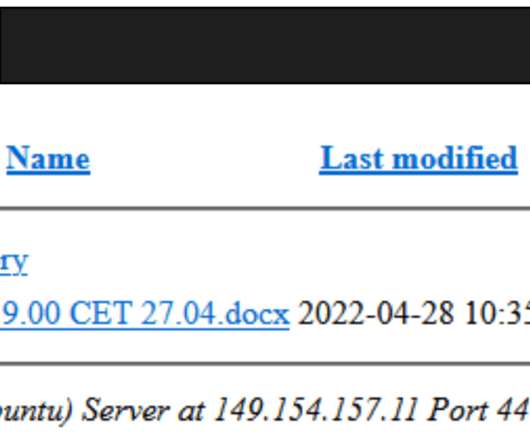
Threat & Detection Research (TDR) team have uncovered a reconnaissance and espionage campaign conducted by Russia-linked Turla APT aimed at the Baltic Defense College, the Austrian Economic Chamber (involved in government decision-making such as economic sanctions) and NATO’s eLearning platform JDAL (Joint Advanced Distributed Learning).

Security Affairs
MARCH 31, 2022
The Google TAG uses uncovered phishing attacks targeting Eastern European and NATO countries, including Ukraine. The attacks of the group also aimed at a Ukrainian defense contractor and several US-based non-governmental organizations (NGOs) and think tanks. ” reads the report published by the TAG team.
Security Affairs
APRIL 6, 2023
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. TAG believes that the ARCHIPELAGO group is a subset of a threat actor tracked by Mandiant as APT43. ” reads the analysis published by Google TAG.
Security Affairs
JULY 15, 2023
Russia-linked APT Gamaredon starts stealing data from victims between 30 and 50 minutes after the initial compromise The source code of the BlackLotus UEFI Bootkit was leaked on GitHub US CISA warns of Rockwell Automation ControlLogix flaws Indexing Over 15 Million WordPress Websites with PWNPress New AVrecon botnet remained under the radar for two (..)

Security Affairs
JANUARY 11, 2023
US CISA added Microsoft Exchange elevation of privileges bug CVE-2022-41080 to its Known Exploited Vulnerabilities Catalog. Government experts believe that other ransomware gangs could exploit the same exploit chain in attacks in the wild. CVE-2022-41082 – Microsoft Exchange Server Remote Code Execution Vulnerability.

Security Affairs
OCTOBER 1, 2021
The CVE-2021-37976 is an Information leak that resides in the core, it was reported by Clément Lecigne from Google TAG, with technical assistance from Sergei Glazunov and Mark Brand from Google Project Zero on 2021-09-21. ” states the update provided by Google. ” states the update provided by Google.

eDiscovery Daily
MARCH 28, 2024
One key similarity lies in the meticulous management of data, starting from governance levels and progressing through collection, processing, review, and export stages. FOIA and public records requests are legally mandated, mirroring the legal frameworks that govern eDiscovery processes.

AIIM
MAY 8, 2023
Embracing 365 Governance Modernizing and Automating Records Management with Microsoft Purview Records Management at Cummins The Future Looks Bright, Just Different. These included discussions on the role of AI in classification and extraction, intelligent document processing (IDP), tagging unstructured content, knowledge management, and more.
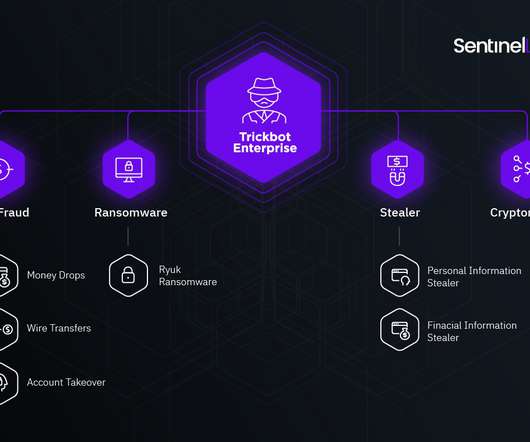
Security Affairs
JUNE 5, 2021
The US Department of Justice (DOJ) announced the arrest of a Latvian woman for her alleged role in the development of the Trickbot malware. The US Department of Justice (DOJ) announced the arrest of Alla Witte (aka Max), a Latvian woman that was charged for her alleged role in the development of the Trickbot malware.

Collibra
JANUARY 23, 2023
Zero trust, a government wide initiative Zero-trust was originally introduced as a network-based architecture mode, which centralized on identity and multi-factor authentication. In fact, the US federal government has made it a mandate; it has been one year since the White House set forth its zero-trust strategy.
Security Affairs
MAY 9, 2022
China-linked Mustang Panda APT group targets entities in Asia, the European Union, Russia, and the US in a new wave of attacks. The attacks were also reported by Google’s TAG team, which confirmed they were for intelligence purposes. In some cases, the threat actors used stagers and reverse shells instead of using PlugX.

Schneier on Security
SEPTEMBER 3, 2019
Earlier this year, Google's Project Zero found a series of websites that have been using zero-day vulnerabilities to indiscriminately install malware on iPhones that would visit the site. Earlier this year Google's Threat Analysis Group (TAG) discovered a small collection of hacked websites. Which leads us all to blame China.

erwin
JANUARY 7, 2021
Our predictions for 2021 are rooted in what we’ve learned from the past year and the relevance of data in getting us to where we are and where we need to go. AI-Fueled Data Governance: Artificial intelligence (AI) has been narrowly tied to the internet of things (IoT) with smart features like Alexa, Nest and self-driving cars.

Collibra
MAY 4, 2021
With an open data and cloud platform, users need data governance to continue to reap the benefits of the open architecture. That’s why we are excited about this partnership so we can support customers leveraging both Databricks and Google Cloud for their governance needs. Collibra offers: .

IBM Big Data Hub
APRIL 24, 2024
The General Data Protection Regulation (GDRP) The GDPR is a European Union privacy regulation that governs how organizations in and outside of Europe handle the personal data of EU residents. PIPEDA grants data subjects a significant amount of control over their data, but it applies only to data used for commercial purposes.

Everteam
SEPTEMBER 20, 2019
In this session, we explored AI and Blockchain’s impact on core information governance processes and records management practices. Below are 4 key takeaways from the conversation: EC M is moving toward federated information governance. AI and Blockchain extend the reach of Information Governance.

Security Affairs
JULY 23, 2018
government should opt to carry out hack backs as retaliation against the massive attacks against organizations in the US private sector. I think if it’s going to happen, it’s best in the hands of the government,” said Sean Weppner, chief strategy officer at NISOS Group and a former DOD cyber officer. “The U.S.

RFID Global Solution, Inc.
JULY 15, 2017
Driven by lower prices of radio-frequency identification (RFID) tags, and increasing penetration of RFID technology in various industries, the RFID market is likely to witness high growth in coming years. The offerings of the tags, chips and software providers have also been taken into consideration to determine the market segmentation.
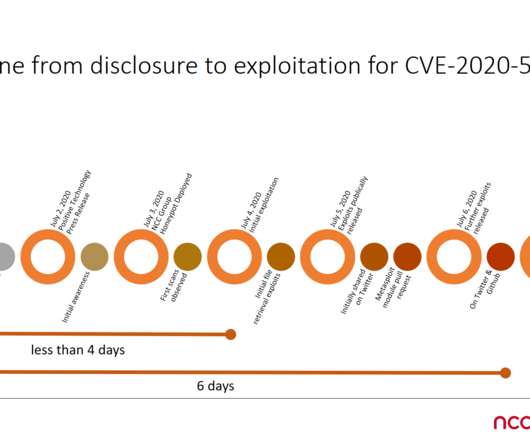
Security Affairs
JULY 8, 2020
The BIG-IP product is an application delivery controller (ADC), it is used by government agencies and major business, including banks, services providers and IT giants like Facebook, Microsoft and Oracle. F5 Networks says the BIG-IP devices are used on the networks of 48 companies included in the Fortune 50 list.

Security Affairs
JULY 25, 2020
The BIG-IP product is an application delivery controller (ADC), it is used by government agencies and major business, including banks, services providers and IT giants like Facebook, Microsoft and Oracle. F5 Networks says the BIG-IP devices are used on the networks of 48 companies included in the Fortune 50 list.

Archives Blogs
JUNE 12, 2020
With the closure of our facilities, we have adjusted our operations to balance the need to conduct our mission-critical work while also adhering to safety guidelines from the federal government. Staff has also been tagging and transcribing records in the Catalog.

InfoGovNuggets
MARCH 18, 2019
I have also changed the categories that I am using to tag posts, with the Big Three: Information, Governance, and Compliance. I have now added (back in) a category for Use, which is often an aspect of Information.

Collibra
JULY 22, 2020
Data is all around us. Sometimes they do this because they don’t know where to start, assume it requires too much heavy lifting, and fear a hefty price tag. But we’re here to tell you that the place to start is active data governance and it doesn’t require you to reinvent the wheel or scramble for every nickel and dime in your budget.

Troy Hunt
MARCH 1, 2018
And this is precisely why I'm writing this piece - to talk about how I'm assisting the UK and Australian governments with access to data about their own domains. Amongst those verified domain searches are government departments and they too are enormously varied; local councils, legal and health services, telecoms and infrastructure etc.

Collibra
JULY 22, 2020
Data is all around us. Sometimes they do this because they don’t know where to start, assume it requires too much heavy lifting, and fear a hefty price tag. But we’re here to tell you that the place to start is active data governance and it doesn’t require you to reinvent the wheel or scramble for every nickel and dime in your budget.
ARMA International
AUGUST 19, 2020
Taxonomies can tell us a lot because they’re a reflection of what they organize. Now, many of the terms in our taxonomy represent common themes you’d expect to see at an ARMA conference, terms like “records management,” “information governance,” and “information management.” Generally Accepted Recordkeeping Principles: I know, I know.

IT Governance
MAY 7, 2019
Most of us use social media to keep in touch with friends, read interesting content or share photos, but we also know it comes with risk. How private our data really is and whether or not “they” are listening is constantly in the news, but do you know the risks of personal social media use to your business?

Unwritten Record
MAY 13, 2021
Earlier this year, scans were added to our online catalog for nearly all of the World War II, US Air Force photography. Previously in 1983, the photographs within 342-FH were loaned by the US Air Force to the National Air and Space Museum, a Smithsonian institution. 1940 – ca.

Security Affairs
OCTOBER 13, 2020
The market surpassed $100 billion in revenue, and it’s revenue for the 2025 projections tell us that it will hit $1.5 Before we dive into the specific cybersecurity concerns, let us remind you about the attack that took place in October 2016. Users could leave all the responsibility to governments and other institutions.

AIIM
JANUARY 15, 2019
More data and process improvement will, in turn, allow us to do more with our content, to reach new audiences and boost satisfaction and profitability, however you measure it. Of course, we've been digitizing content and delivering electronically -- and wrestling with metadata, search, information governance, and compliance -- for decades.

Daradiction
MARCH 5, 2010
Help Us Make Your Government Suck Less! Please help us get the word out so that your government can suck less. Tags: Capitalism Ethics and Social Justice Technology Uncategorized. Your votes count and we’ll throw a big party when we win.

Armstrong Archives
JUNE 3, 2020
Not only do records need to be organized and filed for general business efficiency but the government also requires record retention for tax and other legal purposes. Security and Regulations : When records are stored onsite, what many companies don’t realize is that they must be tagged appropriately to avoid compliance violations.

ForAllSecure
JANUARY 28, 2021
The US government has published a software library called six-library designed to parse and manipulate satellite imagery and data for both internal and public use. One thing is for sure, this code is likely used in both government and private code bases and this particular bug has been lying unknown (hopefully!)

ForAllSecure
JANUARY 28, 2021
The US government has published a software library called six-library designed to parse and manipulate satellite imagery and data for both internal and public use. One thing is for sure, this code is likely used in both government and private code bases and this particular bug has been lying unknown (hopefully!)

The Texas Record
SEPTEMBER 25, 2017
Let us know in the comments below what topics you are interested in learning more about! “Governments Turn Tables by Suing Public Records Requesters” – AP News. Today must be backwards day because in a bizarre turn of events, government entities are suing those who request records.

The Last Watchdog
OCTOBER 19, 2021
The tech giants control the content and services we’re immersed in and return value to us in the form of free or cheap access to the infrastructure they so tightly control. Gogloza : Wildland can be deployed and used at any scale. It is also flexible enough to allow many different use cases, not just business or work-related.

John Battelle's Searchblog
JULY 16, 2013
Then again, I realize I’ve been thinking about this stuff for more than two decades – I assigned and edited a story about massive government data overreach in the first issue of Wired , for God’s sake, and we’re having our 20th anniversary party this Saturday. He then continues. “At

erwin
JANUARY 11, 2019
A company can’t effectively implement data governance – documenting and applying business rules and processes, analyzing the impact of changes and conducting audits – if it fails at data management. If you want more control over and more value from all your data, join us for a demo of erwin MM. Creating a High-Quality Data Pipeline.

IBM Big Data Hub
OCTOBER 16, 2023
The nonprofit tech organization Change Machine worked with IBM to build an AI-powered recommendation engine using IBM Cloud Pak® for Data that helps financial coaches find fintech products best suited to its customers’ goals. ML algorithms govern the facial recognition we rely on to turn on our phones.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content