SEO Poisoning Attacks on Healthcare Sector Rising, HHS Warns
Data Breach Today
JUNE 23, 2023
federal regulators warn. Users should watch for typosquatting, keyword stuffing, meta tagging and cloaking.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag regulation
tag regulation 
Data Breach Today
JUNE 23, 2023
federal regulators warn. Users should watch for typosquatting, keyword stuffing, meta tagging and cloaking.

WIRED Threat Level
FEBRUARY 29, 2024
The UK’s privacy regulator says the government did not take into account the intrusiveness of ankle tags that continuously monitor a person’s location.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JANUARY 13, 2022
Commodity Futures Trading Commission (CFTC) fine against JPMorgan sent shockwaves through financial and other regulated customer-facing industries. While the price tag of these violations was shocking, the compliance failure was not. Related: Why third-party risks are on the rise. These views were echoed in a CFTC release as well.
Hunton Privacy
FEBRUARY 16, 2022
The suit focuses on Meta’s “tag suggestions” feature, which the company has since retired. The feature scanned faces in users’ photos and videos to suggest “tagging” ( i.e. , identify by name) users who appeared in the photos and videos.
Hunton Privacy
NOVEMBER 8, 2021
The company cited the need to “weigh the positive use cases for facial recognition against growing societal concerns, especially as regulators have yet to provide clear rules.”. Users also will no longer see suggested tags or be able to turn on suggested tagging.

DLA Piper Privacy Matters
JANUARY 19, 2022
The new “Administrative Regulations on Algorithm Recommendation of Internet Business Services” comes into force on 1 March 2022, and will introduce important rules on the use of algorithms when operating digital platforms/websites/apps – including targeted marketing – in China. Authors: Carolyn Bigg , Venus Cheung , Fangfang Song.

AIIM
JANUARY 7, 2021
Stop End-User Tagging: For too long, end-user tagging has been the primary means by which most companies classify files that contain sensitive, proprietary, or regulated data. The sheer volume of data regulations is impossible for end-users to keep track up. Regulations are not going away.

The Last Watchdog
JUNE 23, 2023
With Dasera, organizations can unlock the full potential of their data while maintaining compliance with industry regulations. With “Ski Lift,” Snowflake customers can gain a panoramic view of their Snowflake environment while scaling their data security and governance controls.

The Guardian Data Protection
JANUARY 30, 2020
Tag Suggest feature broke rules by storing facial recognition imagery without permission from users Facebook has settled a lawsuit over facial recognition technology, agreeing to pay $550m (£419m) over accusations it had broken an Illinois state law regulating the use of biometric details.
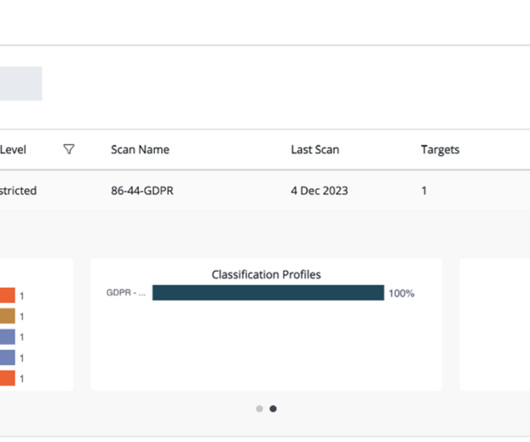
Thales Cloud Protection & Licensing
DECEMBER 11, 2023
Traditional approaches to data classification use manual tagging which is labor-intensive, error-prone, and not easily scalable. Navigating Diverse Data Repositories for Visibility Data discovery is the first step for organizations looking to comply with data protection regulations worldwide.

Data Protection Report
JULY 25, 2023
The requirements of this regulation will apply to domestic companies and to overseas generative AI service providers offering generative AI services to general public in China. This regulation is the latest addition to AI regulations in China after the Algorithm Provisions in 2021 and the Deep Synthesis Provisions in 2022.

DLA Piper Privacy Matters
APRIL 20, 2021
were published by the PBOC (the PRC banking regulator) and came into force on 8 April 2021. In practice this will require financial institutions to assess and classify/tag financial data against the five levels, and apply the relevant compliance obligations to each level accordingly.

erwin
APRIL 11, 2019
Keeping up with new data protection regulations can be difficult, and the latest – the General Data Protection Regulation (GDPR) – isn’t the only new data protection regulation organizations should be aware of. New Data Protection Regulations – Always Be Prepared. employees).

IBM Big Data Hub
APRIL 24, 2024
Far-reaching regulations like Europe’s GDPR levy steep fines on organizations that fail to safeguard sensitive information. Examples of data privacy laws Compliance with relevant regulations is the foundation of many data privacy efforts. The price tag can add up quickly.

Gimmal
NOVEMBER 13, 2019
When users through out all departments are creating new records without a thought to how they are cataloged or tagged, the sprawl of records can become a real threat. Unstructured data can lead to compliance issues for highly regulated industries. Why should an organization care about records management?

DLA Piper Privacy Matters
AUGUST 1, 2019
Since the European Commission unveiled a proposal for an e-Privacy Regulation in January 2017, this new piece of legislation, aiming to adapt rules on electronic communications and cookies, has undergone many iterations. The provision has now been split, each Article regulating processing of a specific type of data: Art.

The Last Watchdog
OCTOBER 24, 2022
Data discovery technologies can scan data stores and label sensitive and regulated data by purpose and type. Make sure to use common, understandable labels and data value tags for your data. Inventorying sensitive data is a crucial process in protecting your business from data breaches. Use a corporate VPN.

The Last Watchdog
NOVEMBER 19, 2018
Many of these photos are tagged with the identity of the people in them. Because the technical winds are strongly behind this trend, the only way to limit it will be through legislation and regulation. This kind of Orwellian scenario is already developing in China. This kind of technology would have many applications.

Data Matters
MARCH 11, 2022
The SEC proposes to amend Item 407 of Regulation S-K to require a description of the cybersecurity expertise of a registrant’s board. XBRL is both machine-readable and human-readable and includes block text tagging as well as detail tagging of narrative disclosures. Required disclosures concerning board cybersecurity expertise.

erwin
APRIL 2, 2021
For example, understanding and protecting sensitive data is especially critical for complying with privacy regulations like the European Union’s General Data Protection Regulation (GDPR). The demands GDPR places on organizations are all-encompassing.

DLA Piper Privacy Matters
JUNE 5, 2020
The California Attorney General has posted the final proposed CCPA Regulations , which were submitted to the California Office of Administrative Law (OAL) on June 1, 2020. The final proposed regulations are virtually unchanged from the prior version , posted on March 11. Enforcement of Regulations. Review process.

erwin
JUNE 26, 2020
Tools should be provided that enable data experts to explore the data catalogs, curate and enrich the metadata with tags, associations, ratings, annotations, and any other information and context that helps users find data faster and use it with confidence. Why You Need a Data Catalog – Three Business Benefits of Data Catalogs.

erwin
JANUARY 7, 2021
However, challenges persist if your organization doesn’t take proper precautions in supporting a remote workforce — from human resources to productivity and IT security – especially when regulations such as the European Union’s General Data Protection Regulation (GDPR) are involved.

Armstrong Archives
DECEMBER 18, 2023
Prevent Compliance Failures: Every industry is different, and so are the specific regulations mandating document retention. Industry-Specific Records Regulations Various industries have rules concerning the handling, protection, and destruction of certain records. State-Specific Regulations Depending on where you live in the U.S.

DLA Piper Privacy Matters
JUNE 21, 2021
The DSL stresses the connection between this new DSL and compliance with the CSL, industry guidelines and other administrative regulations regarding data security/protection as well as state secrets laws. It is unclear whether this may apply to requests for data from other overseas regulators such as industry regulators.
Hunton Privacy
AUGUST 12, 2021
The 2014 resolution previously had been superseded by changes to the applicable legal framework, including the entry into force of the EU General Data Protection Regulation (“GDPR”). The Guidelines replace the resolution dated May 8, 2014, which set out simplified arrangements to provide information and obtain consent regarding cookies.

IBM Big Data Hub
NOVEMBER 28, 2022
Suppose that a new data asset becomes available but remains hidden from your data consumers because of improper or inadequate tagging. According to the Gartner Hype Cycle for Data Privacy 2021, more than 80% of companies worldwide will face at least one privacy-focused data protection regulation by 2023. Protect your data.

Data Matters
AUGUST 19, 2020
Part 500 (Cybersecurity Regulation or Regulation). The First American Statement of charges alleges six violations of the Cybersecurity Regulation and marks the Department’s first action pursuant to the Regulation, which is enforced by the recently created NYDFS Cybersecurity Division. e) and 500.01(g),
Security Affairs
AUGUST 1, 2022
Encevo registered a complaint with the Police of the Grand Duchy and of course notified the CNPD (National Commission for Data Protection), the ILR (Luxembourg Institute of Regulation) and the competent ministries. It seems that some of the stolen files are still under indexing, but majority is already available for quick navigation.

Collibra
APRIL 14, 2021
The next step in the integration is for Collibra’s policy management capabilities to be combined with Google Cloud’s access controls to ensure data usage remains in compliance with applicable rules and regulations.

Armstrong Archives
DECEMBER 20, 2018
Each state has different regulations that govern record retention. These regulations are typically divided into sections based on the type of documents your company or organization handles and stores. For example, in Texas, there are different regulations for state agencies, libraries and archives, and employer records.

erwin
OCTOBER 31, 2019
We don’t want you to be caught off guard when it comes to protecting sensitive data and staying compliant with data regulations. Now, as Cybersecurity Awareness Month comes to a close – and ghosts and goblins roam the streets – we thought it a good time to resurrect some guidance on how data governance can make data security less scary.
Hunton Privacy
MARCH 11, 2022
The proposed rules also amend Form 10-K to require disclosure around cybersecurity risk management, strategy, and governance, each as specified in Items 106(b) and 106(c) of Regulation S-K. Whether and how frequently such persons or committees report to the board of directors or a committee of the board of directors on cybersecurity risk.

Reltio
MARCH 17, 2020
Noncompliance could carry a hefty price tag. Learn from what worked and what didn’t work in the implementation of other privacy regulations, including GDPR, and use those learnings to streamline compliance with the CCPA. For starters, according to Forbes , California would be the fifth-largest economy in the world if it were a country.

Hunton Privacy
MARCH 27, 2018
On March 26, 2018, the Centre for Information Policy Leadership at Hunton & Williams LLP and AvePoint released its second Global GDPR Readiness Report (the “Report”), detailing the results of a joint global survey launched in July 2017 concerning organizational preparedness for implementing the EU General Data Protection Regulation (“GDPR”).

Armstrong Archives
JUNE 3, 2020
Security and Regulations : When records are stored onsite, what many companies don’t realize is that they must be tagged appropriately to avoid compliance violations. Records stored on-site are much less likely to be properly tagged than those managed off-site.

eSecurity Planet
NOVEMBER 2, 2023
Enter the tagged VLAN and the largest debate surrounding VLANs: Is it better to work with a tagged or an untagged VLAN setup? Tagged VLANs are best for larger organizations that need stricter traffic and security controls over more complex, higher volume, and different types of network traffic. Also read: What is a VLAN?

eSecurity Planet
AUGUST 22, 2023
Some data protection regulations, including HIPAA and CCPA , require organizations to inform customers when their personal information has been compromised. Eventually, you will have to go hunting for it, at an inconvenient time, and data may get lost if it’s not properly tagged or otherwise categorized.

AIIM
NOVEMBER 16, 2017
Even though The European General Data Protection Regulation (GDPR) will go into effect in just seven short months on May 25, 2018 a recently published Gartner report found that 50 percent of the companies surveyed do not expect to be ready to comply with a much more rigorous privacy regime including its onerous enforcement provisions.

eSecurity Planet
OCTOBER 28, 2021
Not only do these systems garner heavy price tags, it can be challenging to find and retain highly trained specialists that know how to work with them. For highly regulated industries such as finance or healthcare, they can be the extra measure of protection needed to adequately secure your organization.

Everteam
APRIL 25, 2019
Files are tagged based on type, collected and routed, moved and managed manually. Second Wave: Ingestion-Based Solution: Physical files are scanned and captured, identified, tagged based on type, collected electronically and routed, moved and managed using workflows. Related Citations (Regulations). The key takeaway?

IBM Big Data Hub
JANUARY 24, 2024
Regulated cloud costs Too often, organizations overprovision resources in case there’s a spike in demand to make sure their applications perform. In planning, Turbonomic software takes the efficiencies of different hardware and depreciation schedules into account, plugging in tags to indicate when leases expire.

IBM Big Data Hub
DECEMBER 19, 2023
Post-development (last-mile) wait time before go-live is easily 6–8 weeks or more due to: Manual evidence collection to get through security and compliance reviews beyond standard SAST/SCA/DAST (such as security configuration, day 2 controls, tagging and more).

Collibra
NOVEMBER 5, 2020
Who is regulating or adding this data? Are there regional privacy or security policies that regulate this data? Data enrichment through automatic discovery and user tagging and rating (for example, tagging personally identifiable information or PII). What is the abbreviation or acronym for this data element?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content