The UK’s GPS Tagging of Migrants Has Been Ruled Illegal
WIRED Threat Level
FEBRUARY 29, 2024
The UK’s privacy regulator says the government did not take into account the intrusiveness of ankle tags that continuously monitor a person’s location.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag
tag  Privacy Related Topics
Privacy Related Topics 
WIRED Threat Level
FEBRUARY 29, 2024
The UK’s privacy regulator says the government did not take into account the intrusiveness of ankle tags that continuously monitor a person’s location.

WIRED Threat Level
FEBRUARY 27, 2024
Ankle tags that constantly log a person’s coordinates are part of a growing cadre of experimental surveillance tools that countries around the world are trying out on new arrivals.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IBM Big Data Hub
APRIL 24, 2024
These are just some examples of how organizations support data privacy , the principle that people should have control of their personal data, including who can see it, who can collect it, and how it can be used. One cannot overstate the importance of data privacy for businesses today.
Hunton Privacy
JUNE 8, 2023
On May 24, 2023 Google LLC (“Google”) announced its recently updated privacy terms providing that, for many of Google’s advertising services, it will no longer act as a service provider for the purposes of the California Privacy Rights Act of 2020 (“CPRA”).

The Last Watchdog
NOVEMBER 19, 2018
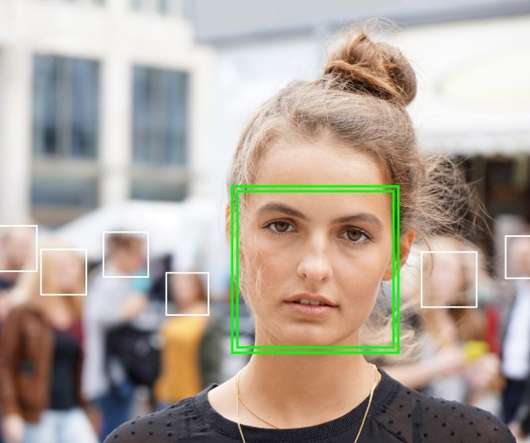
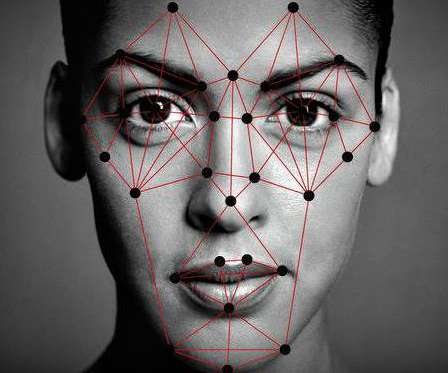
Tech advances are accelerating the use of facial recognition as a reliable and ubiquitous mass surveillance tool, privacy advocates warn. Assuming privacy concerns get addressed, much wider consumer uses are envisioned in areas such as marketing, retailing and health services. Related: Drivers behind facial recognition boom.
Hunton Privacy
FEBRUARY 16, 2022
The suit focuses on Meta’s “tag suggestions” feature, which the company has since retired. The feature scanned faces in users’ photos and videos to suggest “tagging” ( i.e. , identify by name) users who appeared in the photos and videos.
Hunton Privacy
MARCH 1, 2024
On March 1, 2024, the UK Information Commissioner’s Office (“ICO”) announced that it had issued an enforcement notice and a warning to the UK Home Office for failing to sufficiently assess the privacy risks posed by the electronic monitoring of people arriving in the UK via unauthorized means.

Schneier on Security
JUNE 19, 2019
owski has a really good essay explaining how to think about privacy today: For the purposes of this essay, I'll call it "ambient privacy" -- the understanding that there is value in having our everyday interactions with one another remain outside the reach of monitoring, and that the small details of our daily lives should pass by unremembered.

eDiscovery Daily
FEBRUARY 14, 2019
He was “tagged,” thus allowing him access to them, and others were sent to his phone. Should discoverability of photos be extended to photos where the party is “tagged” in the photo or should privacy concerns weigh heavier here? That plaintiff did not take the pictures himself is of no import. Pollari, 107 A.D.3d
Threatpost
JANUARY 30, 2020
The settlement in a case over the social network’s Tag Suggestions feature is the latest financial blow the company has taken over its handling of user privacy.

DLA Piper Privacy Matters
AUGUST 1, 2019
Since the European Commission unveiled a proposal for an e-Privacy Regulation in January 2017, this new piece of legislation, aiming to adapt rules on electronic communications and cookies, has undergone many iterations. Key topics: current status in the Council’s draft e-Privacy Regulation. b) Cookies and similar files/tags.

eSecurity Planet
NOVEMBER 2, 2023
Enter the tagged VLAN and the largest debate surrounding VLANs: Is it better to work with a tagged or an untagged VLAN setup? Tagged VLANs are best for larger organizations that need stricter traffic and security controls over more complex, higher volume, and different types of network traffic. Also read: What is a VLAN?
Krebs on Security
DECEMBER 4, 2019
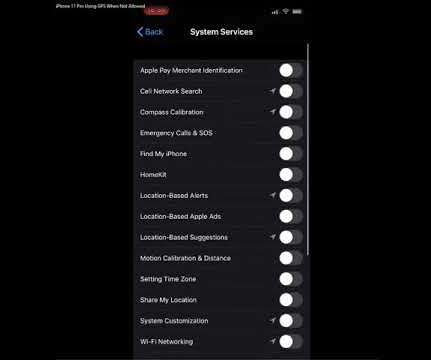
Apple says this is by design, but that response seems at odds with the company’s own privacy policy. ” The policy explains users can disable all location services entirely with one swipe (by navigating to Settings > Privacy > Location Services, then switching “Location Services” to “off”).

Threatpost
SEPTEMBER 3, 2019
Facebook will not allow users to "opt out" of its face recognition feature.
Hunton Privacy
NOVEMBER 8, 2021
The Facebook platform has long used facial recognition to provide recommendations for who to tag in photos and videos, and to alert users when a photo they were in is uploaded by another user. Users also will no longer see suggested tags or be able to turn on suggested tagging.

Krebs on Security
MARCH 31, 2019
Pr0gramm’s top members accused KrebsOnSecurity of violating their privacy, even though all of the research published about them was publicly available online. Please tag your donation bills properly if they shall be accounted. The official tag is ‘krebsspende.’ “cancer”). .

DLA Piper Privacy Matters
JANUARY 19, 2022
Users must also be notified if algorithm recommendations are deployed on a site/platform/app – we anticipate this will be included in the privacy policy or website terms of use. Finally, users must be allowed to delete their individual tagging.
Hunton Privacy
JULY 29, 2020
As we previously reported , Facebook recently reached a $650 million settlement for alleged violations of Illinois’ Biometric Information Privacy Act for their use of facial recognition software without permission from affected users.

eDiscovery Daily
FEBRUARY 3, 2019
According to The Verge ( Crucial biometric privacy law survives Illinois court fight , written by Russell Brandom), Illinois’ Biometric Information Privacy Act (or BIPA), passed in 2008, requires affirmative consent for companies to collect biometric markers from their customers, including fingerprints and facial recognition models.

Collibra
NOVEMBER 16, 2021
With data governance, organizations can leverage the full power of Snowflake while complying with data privacy and policy requirements. Object tagging and ML-powered automation tagging . Another Snowflake governance feature is object tagging. But tags by themselves don’t enforce any security controls.

Security Affairs
SEPTEMBER 15, 2019
The Tor Project has raised $86,000 for a Bug Smash fund that was created to pay developers that will address critical security and privacy issues in the popular anonymizing network. SecurityAffairs – Tor Project, privacy). ” reads the announcement published by the Tor Project. ” concludes the announcement.

Hunton Privacy
JANUARY 30, 2020
Facebook disclosed on January 29, 2020, that it has agreed to pay $550,000,000 to resolve a biometric privacy class action filed by Illinois users under the Biometric Information Privacy Act (“BIPA”). BIPA is an Illinois law enacted in 2008 that governs the collection, use, sharing, protection and retention of biometric information.

AIIM
JANUARY 7, 2021
Stop End-User Tagging: For too long, end-user tagging has been the primary means by which most companies classify files that contain sensitive, proprietary, or regulated data. Individuals and customers are demanding better privacy and control over personal data. Not knowing is simply no longer an option. Your data is the value.
Security Affairs
NOVEMBER 2, 2021
Facebook is using the face recognition system to analyze photos taken of tagged users and associated users’ profile photos to automatically recognize them in photos and videos. Facebook announced it will stop using the Face Recognition system on its platform and will delete over 1 billion people’s facial recognition profiles.

DLA Piper Privacy Matters
AUGUST 22, 2023
It must also conduct security and ethical assessment on the algorithm and parametric models, record all the manual intervention involved in the annotation management and model training processes to prevent manipulation, and enable data subjects to amend or delete customized tags to opt out.

erwin
APRIL 2, 2021
How can companies protect their enterprise data assets, while also ensuring their availability to stewards and consumers while minimizing costs and meeting data privacy requirements? Without data governance, organizations lack the ability to connect the dots across data governance, security and privacy – and to act accordingly.

Security Affairs
MARCH 27, 2024
DDR would, in effect, “tag” data so that a GPS-type homing beacon would keep a gapless record of where it went, who accessed it, what they did with it, and (with the help of some cyber sleuthing) perhaps why. The second benefit is what we’ll be focusing on today. DDR Knows What Your Data Did Last Summer Then, along came a revolutionary idea.

Security Affairs
FEBRUARY 12, 2024
Datacenter Proxies: this blog post examines the contours of each type and provides info on how to choose the perfect proxy option In the robust landscape of the digital era, our need for privacy, security, and accessibility on the internet has never been more acute. So, how do you choose between the knight and the maverick?
Hunton Privacy
JULY 7, 2020
On June 24, 2020, the Washington State Attorney General (“Washington AG”) announced that it had settled an enforcement action against the owners of the “We Heart It” social media platform for alleged violations of the Children’s Online Privacy Protection Act (“COPPA”) and the Washington State Consumer Protection Act.

Collibra
MARCH 1, 2023
Also, a new Snowflake tag ingestion capability enables Snowflake tags to be incorporated into the Collibra Data Catalog. By leveraging Snowflake tags that categorize data users can develop more compliant business or policy processes and workflows.

The Guardian Data Protection
MAY 1, 2021
Ponder that for a moment and then reflect on the irony of a company that since 2013 has been selling such tagged devices, while at the same time bragging about its commitment to users’ privacy.

Data Protection Report
JULY 25, 2023
the CAC) commence supervisory checks on the generative AI service, co-operate with them, explain the source, size and types of the training data, tagging rules and the mechanisms and principles of the algorithm and provide necessary technology and data, etc., for support and assistance.

erwin
OCTOBER 31, 2019
In fact, we’ve seen some frightening ones play out already: Google’s record GDPR fine – France’s data privacy enforcement agency hit the tech giant with a $57 million penalty in early 2019 – more than 80 times the steepest fine the U.K.’s s Information Commissioner’s Office had levied against both Facebook and Equifax for their data breaches.

Hunton Privacy
JUNE 14, 2011
On June 10, 2011, the Electronic Privacy Information Center (“EPIC”) filed a complaint with the Federal Trade Commission, claiming that Facebook’s facial recognition and automated online image identification features harm consumers and constitute “unfair and deceptive acts and practices.”

Hunton Privacy
JUNE 24, 2011
Recent developments involving the use of facial recognition technology have raised privacy concerns in the United States, Europe and Canada. In Europe, the Article 29 Working Party has announced that it is investigating Facebook’s Tag Suggestions technology to determine whether it violates EU data protection laws.

AIIM
FEBRUARY 21, 2018
The Department of Health and Human Services, Office for Civil Rights (OCR), may impose a penalty on a covered entity for a failure to comply with a requirement of the Privacy Rule. The stakes for non-compliance are significant. These penalties can range from $100 to $50,000 or more per violation, up to an annual maximum of $1.5

eSecurity Planet
OCTOBER 17, 2023
That’s where VLAN tagging — the practice of adding metadata labels, known as VLAN IDs, to information packets on the network — can help. These informative tags help classify different types of information packets across the network, making it clear which VLAN each packet belongs to and how they should operate accordingly.

Security Affairs
OCTOBER 19, 2020
“Clips from the hacked footage have been uploaded on pornographic sites recently, with several explicitly tagged as being from Singapore.” When smart devices are set up, they are still regularly placed around the home with no second thought for privacy,” said ESET Security Specialist Jake Moore.

erwin
JUNE 26, 2020
Tools should be provided that enable data experts to explore the data catalogs, curate and enrich the metadata with tags, associations, ratings, annotations, and any other information and context that helps users find data faster and use it with confidence. Are they equipped to maintain data security and privacy?

AIIM
NOVEMBER 16, 2017
This is the seventh post in a series on privacy by Andrew Pery. You might also be interested in: Mitigate Data Privacy and Security Risks with Machine Learning. The Privacy and Security Dichotomy. Privacy by Design: The Intersection of Law and Technology. What Do the GDPR and new Privacy Laws Mean for U.S.

The Last Watchdog
JANUARY 13, 2022
While the price tag of these violations was shocking, the compliance failure was not. According to a SEC release , hefty fines brought against JPMorgan, and its subsidiaries were based on “widespread and longstanding failures by the firm and its employees to maintain and preserve written communications”.

Hunton Privacy
MAY 8, 2012
The FTC alleged that Myspace’s practice of sharing users’ personal information with unaffiliated third-party advertisers conflicted with representations the company made in its privacy policy, and could allow those advertisers to obtain users’ names, publicly available information and information about their online browsing habits.

Data Protection Report
AUGUST 27, 2018
The California Consumer Privacy Act (“CCPA” or the “Act”) sets a new precedent with its sweeping definition of Personal Information (“PI”). This blog focuses on the CCPA’s broad definition of Personal Information. Stay tuned for additional blogs and information about our upcoming webinar on the CCPA.

Collibra
DECEMBER 13, 2022
Specifically this year both companies gave greater focus to enabling governance of data policies and tagging as well as better lineage harvesting. . Snowflake includes an extensive set of native governance capabilities, expressed through SQL, for tag and data policy management. Collibra Protect. Data Quality and Observability.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content