The UK’s GPS Tagging of Migrants Has Been Ruled Illegal
WIRED Threat Level
FEBRUARY 29, 2024
The UK’s privacy regulator says the government did not take into account the intrusiveness of ankle tags that continuously monitor a person’s location.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag location
tag location 
WIRED Threat Level
FEBRUARY 29, 2024
The UK’s privacy regulator says the government did not take into account the intrusiveness of ankle tags that continuously monitor a person’s location.
Security Affairs
SEPTEMBER 22, 2023
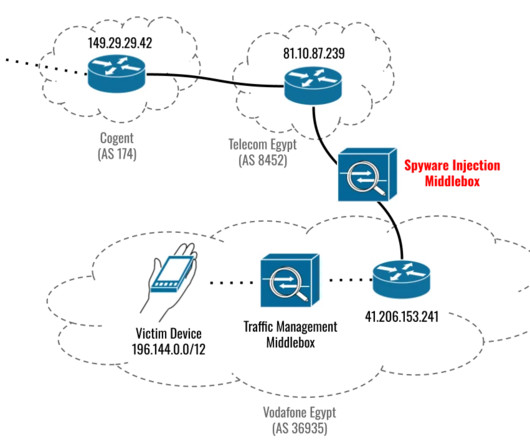
Citizen Lab and Google’s TAG revealed that the three recently patched Apple zero-days were used to install Cytrox Predator spyware. citizenlab in coordination with @Google ’s TAG team found that former Egyptian MP Ahmed Eltantawy was targeted with Cytrox’s #Predator #spyware through links sent via SMS and WhatsApp. .
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Krebs on Security
DECEMBER 4, 2019
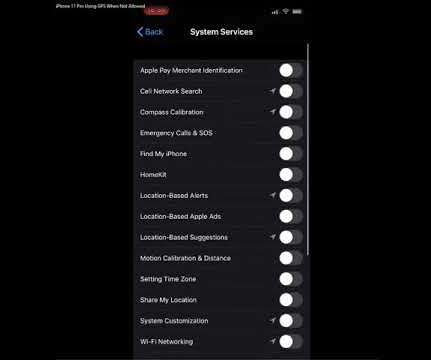
One of the more curious behaviors of Apple’s new iPhone 11 Pro is that it intermittently seeks the user’s location information even when all applications and system services on the phone are individually set to never request this data.

Gimmal
MARCH 11, 2022
Created to facilitate detection of RFID tags that are in range of the network-connected RFID antenna. Using a network-enabled Zebra FX7500 RFID reader, clients can accurately and efficiently check items out to individuals or into a location. Gimmal announces the release of the new RFIDConnect.

HID Global
JANUARY 23, 2023
HID’s Real-Time Location Systems (RTLS) can be extended to combating the epidemic of violence against hospital staff using a tag to track people and objects.
Hunton Privacy
MARCH 1, 2024
According to its statement, the ICO had been in discussions with the Home Office since August 2022 regarding its pilot, which involved the use of ankle tags and the GPS location tracking of up to 600 migrants who arrived in the UK and were on immigration bail.

Security Affairs
MARCH 29, 2023
Google’s Threat Analysis Group (TAG) discovered several exploit chains targeting Android, iOS, and Chrome to install commercial spyware. Google’s Threat Analysis Group (TAG) shared details about two distinct campaigns which used several zero-day exploits against Android, iOS and Chrome. links sent over SMS to users.
Security Affairs
JULY 23, 2023
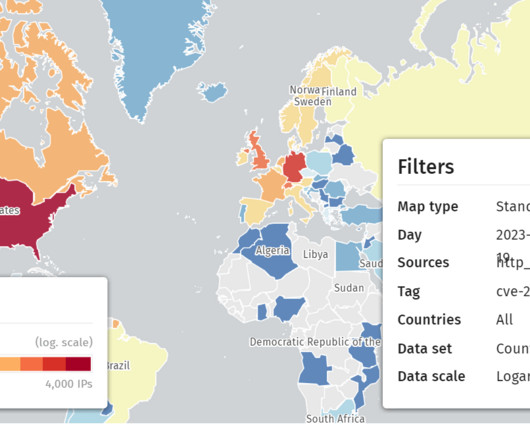
Most of the servers are located in the United States and Germany. Update on CVE-2023-3519 vulnerable IPs: we now tag 15K Citrix IPs as vulnerable to CVE-2023-3519. We extended the tagging logic to tag as vulnerable all that return Last Modified headers with a date before July 1, 2023 00:00:00Z.

Security Affairs
JANUARY 18, 2024
“In order to boot from the network, a client system must be able to locate, download, and execute code that sets up, configures, and runs the operating system. Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, Google TAG) ” reads the advisory.
ARMA International
APRIL 22, 2024
The inventory process gathers information about organizational records including description, series, format, date range, volume, location, and other pertinent data. As solution architects design the “to-be” future state of records locations, the current state is mapped to the new future state for any updates or migrations.

eSecurity Planet
JUNE 1, 2023
To avoid issues, we need to understand the DMARC record tags in detail. DMARC Record Tags in Detail To understand the DMARC record, we start with an example record and then explore the detailed options for each tag. Tags are separated by semicolons ( ; ) with no extra spaces.

Schneier on Security
DECEMBER 6, 2021
From Ontario and not surprising : Since September 2021, officers have investigated five incidents where suspects have placed small tracking devices on high-end vehicles so they can later locate and steal them. Thieves then track the targeted vehicles to the victim’s residence, where they are stolen from the driveway.

Security Affairs
MARCH 31, 2021
Researchers from Google’s Threat Analysis Group (TAG) reported that North Korea-linked hackers are targeting security researchers via social media. ” reads the post published by Google TAG. The cyberspies used fake Twitter and LinkedIn social media accounts to get in contact with the victims.
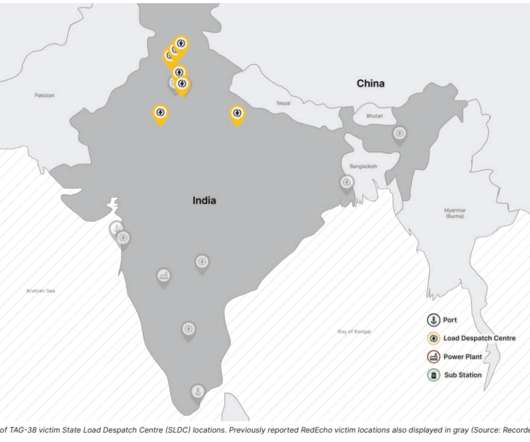
Security Affairs
APRIL 9, 2022
The security firm is tracking this cluster of malicious activities under the moniker Threat Activity Group 38 aka TAG-38. The attacks hit systems located in North India, in proximity to the disputed India-China border in Ladakh. ” reads the advisory published by Recorded Future. ”concludes the report.
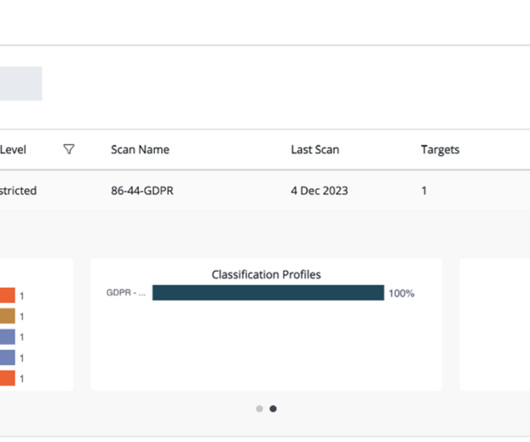
Thales Cloud Protection & Licensing
DECEMBER 11, 2023
Traditional approaches to data classification use manual tagging which is labor-intensive, error-prone, and not easily scalable. While an organization might already know the location of structured data such as a primary customer database store, unstructured data (such as that found in stray files and emails) is more difficult to locate.

Gimmal
MARCH 4, 2022
With Gimmal Physical’s PortableConnect, wireless scanning of barcodes and RFID tags just got easier. PortableConnect allows clients to collect information about the location of their holdings with a hand-held portable device. PortableConnect runs on the new TC52 Zebra device, using Android 11.
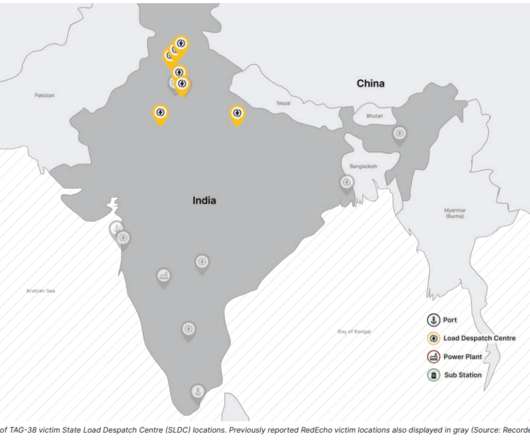
Security Affairs
OCTOBER 15, 2022
The security firm is tracking this cluster of malicious activities under the moniker Threat Activity Group 38 aka TAG-38. The attacks hit systems located in North India, in proximity to the disputed India-China border in Ladakh.

Security Affairs
MAY 7, 2021
In practice, I had access to everything I needed to easily figure out where the NRF52’s SWD pins are located, without even messing with Microscope, GIMP and Multimeter in continuity mode. RFID Feature: One clue still left (from a hardware security POV) was about the RFID tag. Thanks Hideez ). meh…).

IBM Big Data Hub
DECEMBER 18, 2023
With IBM® NS1 Connect Traffic Steering , you don’t have to choose between optimizing for things like the user’s ISP and their geographical location. NS1 Connect adds JavaScript tags to that web property which collect information about inbound user traffic.
Krebs on Security
NOVEMBER 28, 2022
But a recent investigation by Reuters raised questions about the company’s real location and truthfulness. the company’s employees are located in Novosibirsk, Russia. Pushwoosh employees posing at a company laser tag event. Pushwoosh says it is a U.S. regulatory filings present it as a U.S. Edwards said the U.S.

Security Affairs
FEBRUARY 12, 2024
Residential Proxies: The Noble Disguise Residential proxies are like the knights in shining armour of the proxy world; they come with legitimate, ISP-issued IP addresses that trace back to an actual device in a real location. Residential proxies ensure that your requests are seen as coming from a resident of the target location.

Armstrong Archives
MAY 23, 2022
In addition, organizations who have not invested in the creation of document handling policies find that many hours of productivity are lost to locating lost documents. Scanning, tagging, and filing a single page of records can take five minutes. Scanning and tagging documents takes more time than you would think it would.

Security Affairs
MARCH 14, 2023
” “External attackers could send specially crafted emails that will cause a connection from the victim to an external UNC location of attackers’ control. This could lead to exploitation BEFORE the email is viewed in the Preview Pane.” ” states Microsoft.

IG Guru
MAY 25, 2020
As the volume of data continues to grow within our corporate data environments, it becomes increasingly more complex to navigate, locate and contain content in common data silos such as email, file shares, digital archives, cloud storage and other data repositories.
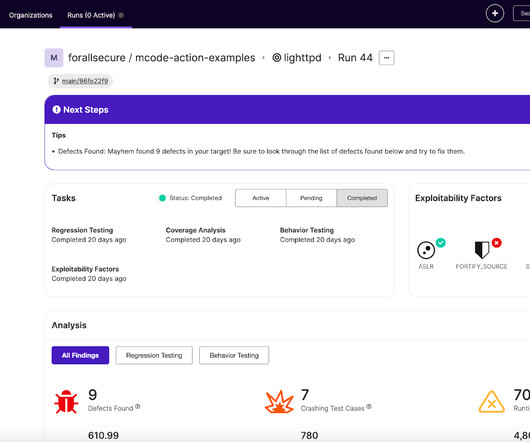
ForAllSecure
MARCH 16, 2023
You will need to specify the location of your Dockerfile and Mayhemfile. with: registry: ${{ env.REGISTRY }} username: ${{ github.actor }} password: ${{ secrets.GITHUB_TOKEN }} - name: Extract metadata (tags, labels) for Docker id: meta uses: docker/metadata-action@v4.1.1

Gimmal
AUGUST 17, 2023
Whether it’s your network file shares, EFSS locations such as Box and Dropbox, or even your email accounts, a large portion of content and records is essentially useless. However, none of these are the right location. Users don’t know what metadata to tag on content. What do you do?

Collibra
DECEMBER 15, 2022
A self-service solution, the Collibra Data Marketplace offers intuitive access to trusted data in one central location, providing a portal so business users can easily find, understand, and request access to the data they need — and generate insights faster. Maximizing collaboration and sharing. Why Collibra Data Marketplace.
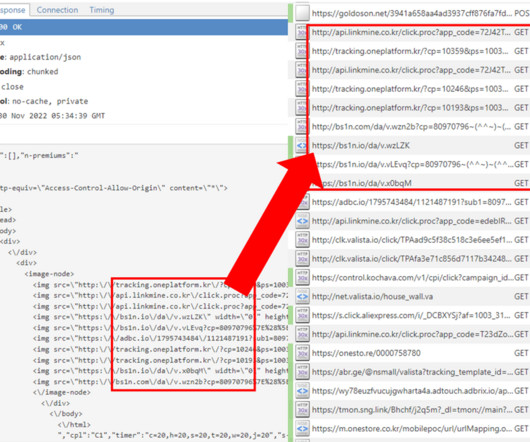
Security Affairs
APRIL 15, 2023
The Goldoson library was discovered by researchers from McAfee’s Mobile Research Team, it collects lists of applications installed on a device, and a history of Wi-Fi and Bluetooth devices information, including nearby GPS locations. The experts have found more than 60 applications in Google Play that were containing the malicious library.

IBM Big Data Hub
MARCH 25, 2022
With this approach, organizations don’t have to move all their data to a single location or data store, nor do they have to take a completely decentralized approach. Smart integration : Data integration capabilities are crucial to extract, ingest, stream, virtualize and transform data regardless of where it’s located.

erwin
APRIL 2, 2021
With data catalog and literacy capabilities, you provide the context to keep relevant data private and secure – the assets available, their locations, the relationships between them, associated systems and processes, authorized users and guidelines for usage. Minimizing Risk Exposure with Data Intelligence.

The Last Watchdog
OCTOBER 24, 2022
Make sure to use common, understandable labels and data value tags for your data. By identifying these locations, you can easily determine security vulnerabilities. Often, it is the first time a company has a common definition of data. If teams have different naming conventions, data inventory can be a confusing process.

Schneier on Security
MAY 2, 2018
Similar small electronics exist in the keyless entry fobs to newer-model cars and the Radio Frequency Identification (RFID) tags used to locate boxes in vast warehouses. All of these gadgets are inexpensive to make and will fit nearly anywhere, but common encryption methods may demand more electronic resources than they possess.

eSecurity Planet
MARCH 15, 2021
Success in implementing microsegmentation for your organization means tagging traffic, servicing regular business communications, adapting to threats , and denying all other anomalies. . All traffic is known, tagged, or verified, preventing any potential vulnerabilities related to trust. . Tag Your Workloads. Application.
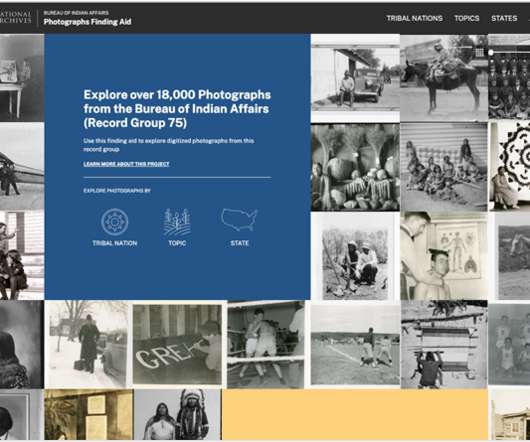
Unwritten Record
NOVEMBER 19, 2020
Once the final list of topics was selected, we curated the photographs into the Native American Photographs Tagging Mission to recruit the help of citizen archivists in tagging the photographs with these topics. The citizen archivist tags are used to power the presentation of photographs by topic in the finding aid.

IBM Big Data Hub
JUNE 20, 2023
Improved compliance: Comply with laws surrounding the management and operation of assets, regardless of where they are located. Radio frequency identifier tags (RFID): RFID tags broadcast information about the asset they’re attached to using radio-frequency signals and Bluetooth technology.

AIIM
APRIL 8, 2021
Version control results in storing one document, with all of its versions, in one location, so there is no confusion. Some systems even offer categorization, tagging, and rating that all assist with search as well. Many systems that offer document control capabilities offer the ability to roll back, or revert to the previous version.
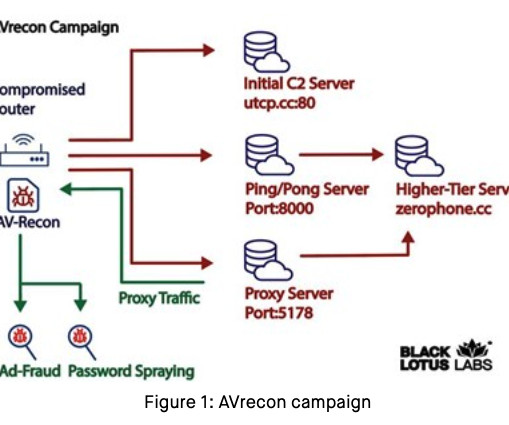
Krebs on Security
JULY 25, 2023
Now new findings reveal that AVrecon is the malware engine behind a 12-year-old service called SocksEscort , which rents hacked residential and small business devices to cybercriminals looking to hide their true location online. The company was located in Chisinau, Moldova and owned by Adrian Crismaru. SocksEscort[.]com

Security Affairs
MARCH 27, 2024
After all, you can’t secure what you can’t see, and today’s environments obfuscate the true location of data so well that we, as security practitioners, can hardly keep up with it. This is not good for advocates of data protection but great for attackers who thrive in our confusion and in the gaps that exist between the boxes.

Security Affairs
OCTOBER 23, 2019
The HIS Group hotel chain has 10 locations in Japan that used robots instead of human personnel to provide some services. The expert discovered an “unsigned code” that could allow an attacker to access video footage via the streaming app of their choice by tapping an NFC tag to the back of robot’s head.

Unwritten Record
OCTOBER 21, 2020
Footage in the 306-LSS series covers locations around the country, including Grand Coulee, Washington. We added record tags, such as the title of a film or government agency that produced the footage (if known), and did our best to identify people, locations, and objects. Still from 306-LSS-900 ).

The Texas Record
JUNE 26, 2023
Whether through naming conventions, tags, or separate folders, make sure you are adequately distinguishing drafts from final versions, and records from non-records and reference. They can tell you what is difficult to locate or confusing about the current system. Design a system for different versions of files.

Collibra
DECEMBER 7, 2022
With this integration, Collibra gives customers a single location to find, understand and create a shared language around data, define the terminology, rules and regulations, and deliver trusted data to the business. We’re also working to bring the context and knowledge stored in its platform as close to the dbt user as possible. .

Data Protection Report
NOVEMBER 29, 2023
Additionally, businesses maintaining models may have to consider ways to identify, tag, and document output pertaining to California consumers given that the access rights require businesses to provide all of the outputs with respect to the consumer in a simple and easy-to-use method.

erwin
JUNE 26, 2020
The metadata provides information about the asset that makes it easier to locate, understand and evaluate. title, author, subject, publication date, edition, location) that makes the publication easier for a reader to find and to evaluate. Another classic example is the online or card catalog at a library.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content