Security Affairs newsletter Round 460 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag banking
tag banking 
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
Security Affairs
OCTOBER 31, 2022
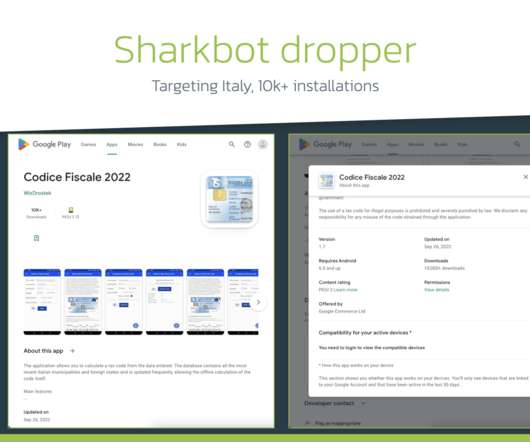
The malicious dropper apps are designed to deliver banking trojans, such as SharkBot and Vultur , that already totaled over 130,000 installations. ” In the beginning of October 2022, the experts uncovered a new campaign spreading the banking Trojan Sharkbot. . ” reads the analysis published by ThreatFabric.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
JUNE 26, 2022
SecurityAffairs awarded as Best European Personal Cybersecurity Blog 2022 Crooks are using RIG Exploit Kit to push Dridex instead of Raccoon stealer Flagstar Bank discloses a data breach that impacted 1.5
Security Affairs
JUNE 5, 2021
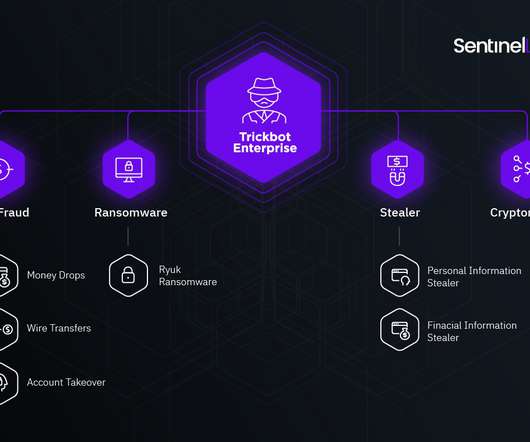
She previously hosted even TrickBot "red" group tag payload on her own website -> see URLhaus [link] [link] pic.twitter.com/qG977wjgLN — Vitali Kremez (@VK_Intel) June 4, 2021. Tango down: "Alla Witte" aka "Alla Klimova" – one known #TrickBot developer and operator arrested!

Security Affairs
OCTOBER 28, 2019
Italian bank UniCredit announced today that around three million of its customers in Italy have been affected by a data breach in 2015. The Italian bank UniCredit announced today that around three million of its Italian clients have been affected by a data breach that took place in 2015, . SecurityAffairs – banking, data breach).

Security Affairs
MARCH 13, 2022
Government Multiple Russian government websites hacked in a supply chain attack Anonymous hacked Russian cams, websites, announced a clamorous leak HP addressed 16 UEFI firmware flaws impacting laptops, desktops, PoS systems Samsung data breach: Lapsus$ gang stole Galaxy devices’ source code Microsoft March 2022 Patch Tuesday updates fix 89 vulnerabilities (..)
Security Affairs
JULY 15, 2023
Russia-linked APT Gamaredon starts stealing data from victims between 30 and 50 minutes after the initial compromise The source code of the BlackLotus UEFI Bootkit was leaked on GitHub US CISA warns of Rockwell Automation ControlLogix flaws Indexing Over 15 Million WordPress Websites with PWNPress New AVrecon botnet remained under the radar for two (..)

DLA Piper Privacy Matters
APRIL 20, 2021
were published by the PBOC (the PRC banking regulator) and came into force on 8 April 2021. similar to the PIS Specification, but focused on the banking and financial services industry). This could be a substantial task for some financial institutions.

Security Affairs
OCTOBER 3, 2021
Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini. SecurityAffairs – hacking, newsletter).

Security Affairs
JULY 4, 2019
For example, the attacker could redirect all payments to his bank account or steal credit card information.” The XSS occurs when the sanitized links are processed via vsprintf(), an additional double quote is injected into the <i> tag allowing for an attribute injection. ” continues the post.
Security Affairs
OCTOBER 25, 2022
The attackers appends the affiliate tags to the URL and any purchase made on the site will generate a commission for the operators. Clearly the same process can be used to redirect victims to phishing pages to steal credentials for popular services, including Microsoft 365, online banking, and social media platforms.
eSecurity Planet
NOVEMBER 16, 2021
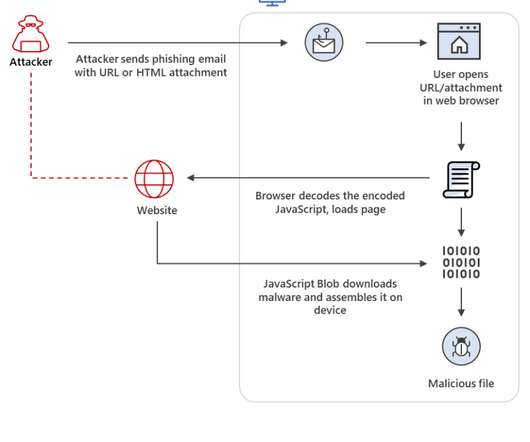
The researchers said they had seen Nobelium using HTML smuggling in a spear-phishing campaign in May, and more recently, observed it being used to deliver the banking Trojan Mekotio and the AsyncRAT/MJRAT and Trickbot malware used by attackers to get control of targeted devices and deliver such malware as ransomware. Trickbot Attacks.

Security Affairs
AUGUST 19, 2018
Researchers from Trustwave have uncovered a malspam campaign targeting banks with the FlawedAmmyy RAT. Experts noticed an anomalous spike in the number of emails with a Microsoft Office Publisher file (a.pub attachment) and the subject line, “Payment Advice,” that was sent to domains belonging to banks. continues the analysis.
Security Affairs
AUGUST 6, 2023
Rapid7 found a bypass for the recently patched actively exploited Ivanti EPMM bug Russian APT29 conducts phishing attacks through Microsoft Teams Hackers already installed web shells on 581 Citrix servers in CVE-2023-3519 attacks Zero-day in Salesforce email services exploited in targeted Facebook phishing campaign Burger King forgets to put a password (..)
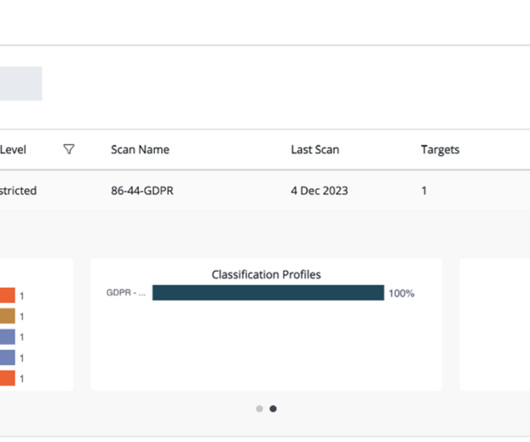
Thales Cloud Protection & Licensing
DECEMBER 11, 2023
Traditional approaches to data classification use manual tagging which is labor-intensive, error-prone, and not easily scalable. This includes personal data like email addresses, dates of birth, telephone numbers, and national ID numbers; financial data like bank account numbers and credit card numbers; and patient health data.

IBM Big Data Hub
OCTOBER 16, 2023
One bank using a watsonx Assistant system for customer service found the chatbot answered 96% of all customer questions correctly, quickly, consistently, and in multiple languages. Machine learning in financial transactions ML and deep learning are widely used in banking, for example, in fraud detection.
Krebs on Security
SEPTEMBER 6, 2021
For years leading up to 2015, “ admin@manipulaters.com ” was the name on the registration records for thousands of scam domains that spoofed some of the world’s top banks and brand names, but particularly Apple and Microsoft. For example, the Facebook profile of Burhan Ul Haq , a.k.a.

OneHub
DECEMBER 14, 2020
That’s a devastating price tag for many companies. Bank-level protection means your data is as secure as your money. Cloud storage operates almost like a bank. Onehub continues the similarities by using the same 256-bit encryption and physical security policies as banks for the most secure cloud storage experience.
Security Affairs
APRIL 23, 2023
Abandoned Eval PHP WordPress plugin abused to backdoor websites CISA adds MinIO, PaperCut, and Chrome bugs to its Known Exploited Vulnerabilities catalog At least 2 critical infrastructure orgs breached by North Korea-linked hackers behind 3CX attack American Bar Association (ABA) suffered a data breach,1.4

Troy Hunt
APRIL 19, 2018
I was chatting to some folks at a bank just the other day about a bunch of modern web security standards. Whilst this blog post is about a Pluralsight course I created with Lars Klint , it only really hit me during that bank conversation just how much there is to take onboard when it comes to securing things in the browser today.

ChiefTech
NOVEMBER 19, 2012
Cory Banks. BTW I'm not sure if we have a hash tag for the event, but I've suggested #cemelb12. This is a list of speakers at Connected Enterprise 2012 who are on Twitter: Brent Lello. Brian Solis. Cuneyt Uysal. Dev Mookerjee. Erin Grotts. Jacob Morgan. James Dellow <- me! Jeffrey Tobias. Lincoln De Kalb. Mike Handes. Paul Miller.

IBM Big Data Hub
APRIL 24, 2024
The price tag can add up quickly. Example A bank sends annual privacy notices to all of its customers. These notices outline all the data that the bank collects from account holders, how it uses that data for things like regulatory compliance and credit decisions, and how long it retains the data.
Security Affairs
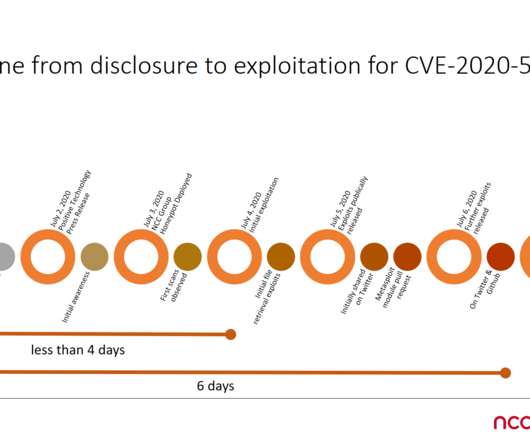
JULY 8, 2020
The BIG-IP product is an application delivery controller (ADC), it is used by government agencies and major business, including banks, services providers and IT giants like Facebook, Microsoft and Oracle. Query our API for "tags=CVE-2020-5902" for a full list of unique payloads and relevant indicators.

erwin
APRIL 11, 2019
Some industries, such as healthcare and financial services, have been subject to stringent data regulations for years: GDPR now joins the Health Insurance Portability and Accountability Act (HIPAA), the Payment Card Industry Data Security Standard (PCI DSS) and the Basel Committee on Banking Supervision (BCBS).
Krebs on Security
MARCH 2, 2020
Other victims included one of France’s largest hospital systems; a French automobile manufacturer; a major French bank; companies that work with or manage networks for French postal and transportation systems; a domestic firm that operates a number of airports in France; a state-owned railway company; and multiple nuclear research facilities.

Security Affairs
MARCH 27, 2019
The AZORult stealer was first spotted in 2016 by Proofpoint that discovered it was part of a secondary infection via the Chthonic banking trojan. The malware has a relatively high price tag ($100), it supports a broad functionality (i.e. the use of.
Security Affairs
DECEMBER 14, 2019
Once a reader visited a site and the compromised ad’s creative tag was loaded, Krampus-3PC unpacked th e code that is used to check (1) whether the ad was hosted by Adtechstack and (2) whether the ad was running on a targeted publisher. Access to a session cookie would enable the malvertiser to log in as that user at a later time.”.

Security Affairs
JULY 25, 2020
The BIG-IP product is an application delivery controller (ADC), it is used by government agencies and major business, including banks, services providers and IT giants like Facebook, Microsoft and Oracle. Query our API for "tags=CVE-2020-5902" for a full list of unique payloads and relevant indicators.

Info Source
FEBRUARY 15, 2019
New artificial intelligence capabilities were also introduced to automate document handling and related processes, such as automatic tagging and classification. Global Investment and Recognition.

Krebs on Security
AUGUST 19, 2020
Primarily, that includes any social media and email accounts, as well as associated financial instruments such as bank accounts and any cryptocurrencies. Nixon said many companies will likely balk at the price tag associated with equipping each employee with a physical security key.

Armstrong Archives
DECEMBER 20, 2018
Shred after three years: personnel records, employment applications, petty cash vouchers, time cards, physical inventory tags, and internal audit reports. Shred after seven years: accident reports and claims, bank statements, cancelled checks, sales records, inventories, employment tax records, and payment vouchers.

Troy Hunt
JUNE 27, 2018
If you are a tech pro and you want to go deeper on HTTPS, have a browse back through the dozens of posts on the SSL tag or go and watch 3 and a half hours of Pluralsight training on the subject. I built a little demo site and embedded all the videos in it over at HTTPSIsEasy.com.

CILIP
JUNE 26, 2019
One of the most important assets to science is the scientific record, which includes the accumulated body of knowledge contained in books, journals, conference proceedings, transcripts of scientific meetings but also data banks, data sets, and online data from research projects.

Security Affairs
MAY 23, 2022
Google’s Threat Analysis Group (TAG) uncovered campaigns targeting Android users with five zero-day vulnerabilities. Google’s Threat Analysis Group (TAG) researchers discovered three campaigns, between August and October 2021, targeting Android users with five zero-day vulnerabilities. ” continues the report.

ChiefTech
JULY 9, 2008
I wouldn't normally blog about this kind of thing, but I was pleasantly surprised to hear about Ralph 's background in information technology (Electronic data processing at Auckland Savings Bank in 1969, to be precise), which eventually saw him move into the role of CEO.

Armstrong Archives
DECEMBER 18, 2023
We’ll take ownership of the entire scanning process, from collection to high-resolution scanning, metadata tagging, and OCR (Optical Character Recognition). We offer two scanning solutions: Service bureau solution: Our team takes care of every step in document scanning. We can also provide your digitized documents on CD or DVD.

erwin
AUGUST 15, 2022
Case Study (Snowflake cloud): Credit Union Banks on erwin Data Modeler by Quest. Relational. Column Oriented. Column Family}. Collection. Primary Key. Partition Key /. Clustering Key. Collection Post. Relationship. Foreign Key. Collection. References}. Figure 6: Understanding the different modeling concepts.

Unwritten Record
OCTOBER 6, 2017
National Bank of Latonia next door whose officers were aiding the League detectives listening in gathered pro-German evidence and arrested Henry Feltman wealthy tobacco merchant J.H. In addition, many of these photographs are tagged only to a geographic center of a city rather than the exact location featured in the photo.

IBM Big Data Hub
FEBRUARY 14, 2024
Clarify computer vision AI-powered computer vision enables image segmentation , which has a wide variety of use cases, including aiding diagnosis in medical imaging, automating locomotion for robotics and self-driving cars, identifying objects of interest in satellite images and photo tagging in social media.

ChiefTech
FEBRUARY 8, 2008
Saturday, 9 February 2008 One feed to rule them all - KM in Australia Cory Banks , from the Queensland KM Forum ( QKM ), has helped to create a listing of Australian knowledge and information management related organisations - its a wiki page so feel free to help keep it up to date!

Data Matters
AUGUST 19, 2020
The consumers’ sensitive personal information included bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts, and drivers’ license images. Public access to these documents was caused by an application software vulnerability that was initially introduced in May 2014.

IBM Big Data Hub
NOVEMBER 29, 2023
In this paper, we showcase how to easily deploy a banking application on both IBM Cloud for Financial Services and Satellite , using automated CI/CD/CC pipelines in a common and consistent manner. To deliver this service, the bank application employs an ecosystem of partner applications interoperating using the BIAN framework.
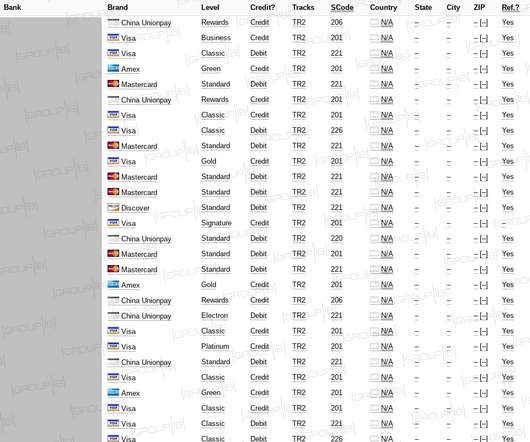
Security Affairs
APRIL 24, 2020
The database was comprised almost entirely of the payment records related to banks and financial organizations in South Korea and the US. Joker’s Stash – the infamous underground marketplace – put a USD 1,985,835 price tag on the set, at USD 5 apiece, and announced that dump had 30-40% valid rate.

Security Affairs
NOVEMBER 12, 2019
In such a case the redirection script pushes to one of the following domains by introducing the HTML meta “refresh” tag, pointing the browser URL to a random choice between 4 different entries belonging to the following two domains: http[://com-kl96.net TA505 hacking group has been active since 2014 focusing on Retail and banking sectors.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content