HID Global Awarded ATEX, IECEX and UKEX Poly Tag™ Certifications
HID Global
OCTOBER 22, 2021
HID Global Awarded ATEX, IECEX and UKEX Poly Tag™ Certifications. Fri, 10/22/2021 - 11:07.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag awards
tag awards 
HID Global
OCTOBER 22, 2021
HID Global Awarded ATEX, IECEX and UKEX Poly Tag™ Certifications. Fri, 10/22/2021 - 11:07.

Security Affairs
MAY 3, 2022
China-linked Curious Gorge APT is targeting Russian government agencies, Google Threat Analysis Group (TAG) warns. Google Threat Analysis Group (TAG) reported that an APT group linked to China’s People’s Liberation Army Strategic Support Force (PLA SSF), tracked as Curious Gorge , is targeting Russian government agencies.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
JUNE 19, 2022
The vulnerability resides in the Merge Tag feature of the plugin. “One feature of Ninja Forms is the ability to add “Merge Tags” to forms that will auto-populate values from other areas of WordPress like Post IDs and logged in user’s names. ” reads the advisory published by Wordfence. 3.1.10, 3.2.28, 3.3.21.4, and 3.6.11.
Security Affairs
APRIL 13, 2022
The remote code execution flaw, tracked as CVE-2020-17530, resides in forced OGNL evaluation when evaluated on raw user input in tag attributes. Forced OGNL evaluation, when evaluated on raw user input in tag attributes, may lead to remote code execution – similar to S2-059.” ” reads the advisory published by Apache.

Security Affairs
APRIL 20, 2023
The researchers from Google TAG are warning of Russia-linked threat actors targeting Ukraine with phishing campaigns. Russia-linked threat actors launched large-volume phishing campaigns against hundreds of users in Ukraine to gather intelligence and aimed at spreading disinformation, states Google’s Threat Analysis Group (TAG).
Security Affairs
APRIL 6, 2023
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. TAG believes that the ARCHIPELAGO group is a subset of a threat actor tracked by Mandiant as APT43. ” reads the analysis published by Google TAG.

The Last Watchdog
AUGUST 8, 2023
With support for Microsoft CA and AWS Private CA, DigiCert Trust Lifecycle Manager enables discovery, issuance, automation and revocation, including the ability to tag, filter and apply policy to imported and discovered third-party digital certificates. For more information, visit?

Security Affairs
APRIL 1, 2023
Google TAG shared indicators of compromise (IoCs) for both campaigns. The experts pointed out that both campaigns were limited and highly targeted. The threat actors behind the attacks used both zero-day and n-day exploits in their exploits. The exploits were used to install commercial spyware and malicious apps on targets’ devices.
Security Affairs
APRIL 17, 2023
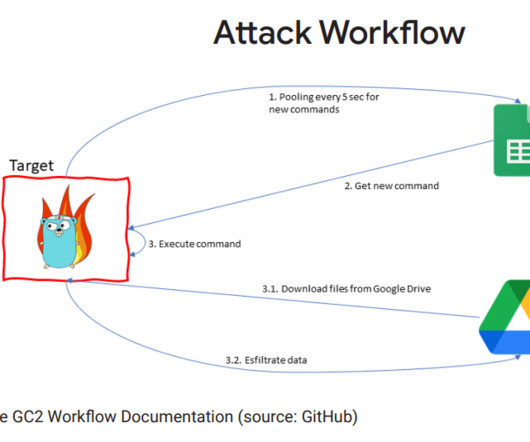
Google Threat Analysis Group (TAG) team reported that the China-linked APT41 group used the open-source red teaming tool Google Command and Control ( GC2 ) in an attack against an unnamed Taiwanese media organization. China-linked APT41 group used the open-source red teaming tool GC2 in an attack against a Taiwanese media organization.
Security Affairs
MAY 23, 2022
SEKOIA researchers started their investigation after the publication of Google’s Threat Analysis Group (TAG)’s report “ Update on cyber activity in Eastern Europe ” which detailed the activity of nation-state actors against Eastern Europe. org jadlactnato.webredirect[.]org.

Security Affairs
MAY 28, 2022
Google’s Threat Analysis Group (TAG) chief Shane Huntley told Reuters was set up by a Russia-linked APT dubbed “ Cold River “ At this time it is unclear how the website has obtained the sensitive emails, Reuters pointed out that most of the messages mainly appear to have been exchanged using ProtonMail accounts.

Security Affairs
APRIL 8, 2023
The CVE-2023-26083 flaw in the Arm Mali GPU driver is chained with other issues to install commercial spyware, as reported by Google’s Threat Analysis Group (TAG) in a recent report. Mandiant researchers first observed this affiliate targeting Veritas issues in the wild on October 22, 2022.
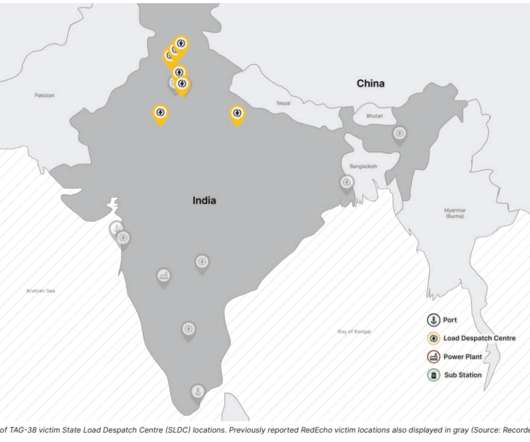
Security Affairs
APRIL 9, 2022
The security firm is tracking this cluster of malicious activities under the moniker Threat Activity Group 38 aka TAG-38. Recorded Future’s Insikt Group researchers uncovered a campaign conducted by a China-linked threat actor targeting Indian power grid organizations. ” reads the advisory published by Recorded Future.

Security Affairs
APRIL 7, 2023
Today, Apple published an emergency update for all iPhones to patch an exploit chain which we, together with @_clem1 (Google TAG) discovered in the wild. Super proud of our team at @AmnestyTech and everyone who helped in this investigation.

Security Affairs
JUNE 26, 2022
SecurityAffairs awarded as Best European Personal Cybersecurity Blog 2022 Crooks are using RIG Exploit Kit to push Dridex instead of Raccoon stealer Flagstar Bank discloses a data breach that impacted 1.5
Security Affairs
APRIL 15, 2023
“The tags such as ‘ads_enable’ or ‘collect_enable’ indicates each functionality to work or not while other parameters define conditions and availability.” Based on the parameters, the library periodically checks, pulls device information, and sends them to the remote servers.” ” concludes the report.
ForAllSecure
MARCH 16, 2023
with: registry: ${{ env.REGISTRY }} username: ${{ github.actor }} password: ${{ secrets.GITHUB_TOKEN }} - name: Extract metadata (tags, labels) for Docker id: meta uses: docker/metadata-action@v4.1.1 Once complete, you’ll need to modify any corresponding Mayhem.yml file to use your specific tagged release and test your changes.

AIIM
MAY 8, 2023
These included discussions on the role of AI in classification and extraction, intelligent document processing (IDP), tagging unstructured content, knowledge management, and more. Over a dozen sessions were dedicated to exploring strategies for professionals to thrive in this new era.
Security Affairs
MAY 7, 2020
The first information tag “ prog.params ” is immediately retrieved in the instruction “ HandlerParams.Start() ” seen in Figure 4. The malware tries to find the id of the mutex, declared inside the relative tag seen in code snippet 2, inside the “%TEMP%” folder. Figure 7: Check of a previous infection. Conclusion.

The Texas Record
OCTOBER 2, 2019
Watch how archivists tag images for preservation and access during the University of North Texas Special Collections’ metadata live stream or log-in for a webinar on Native American boarding school records from the Society of American Archivists (SAA). Webinars, workshops and exhibits will be on offer throughout the month.
Security Affairs
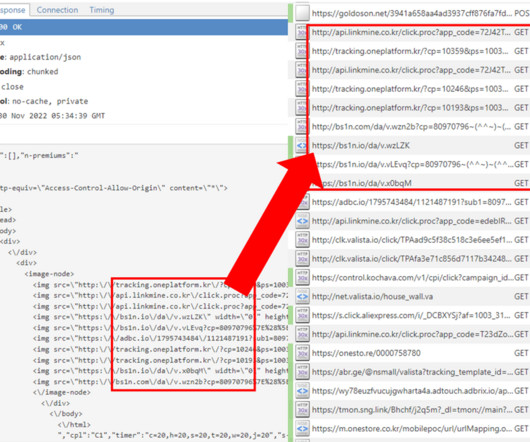
MAY 24, 2022
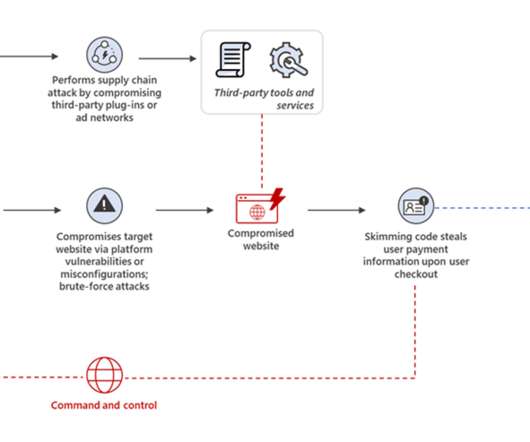
The attackers place a Base64-encoded string inside a spoofed Google Tag Manager code. Security Affairs is one of the finalists for the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS. This string decoded to trafficapps[.]business/data[.]php?p=form. business/data[.]php?p=form.

Archives Blogs
JANUARY 15, 2018
Our goal is to tag or transcribe 2,018 pages in the National Archives Catalog during this week-long challenge. During this week, we’ll have a special expanded missions section and many featured records waiting to be tagged and transcribed. We like to say that as we tag and transcribe, we are unlocking history.
Security Affairs
MAY 9, 2022
The attacks were also reported by Google’s TAG team, which confirmed they were for intelligence purposes. In February 2022, Cisco Talos researchers started observing China-linked cyberespionage group Mustang Panda conducting phishing attacks against European entities, including Russian organizations.

Security Affairs
JUNE 5, 2022
Tags available to all @GreyNoiseIO users now – Create an account to deploy a dynamic block list to block it [link] pic.twitter.com/xXldngWdPH — Andrew Morris @ RSA (@Andrew Morris) June 4, 2022. Security Affairs is one of the finalists for the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS.
Security Affairs
JUNE 6, 2022
According to cybersecurity researchers at Google’s Threat Analysis Group (TAG), government-backed hackers from Russia, China, Iran and North Korea, as well as various unattributed groups and cyber-criminal gangs, are using various themes related to the war in Ukraine to lure people into becoming victims of cyberattacks.
Security Affairs
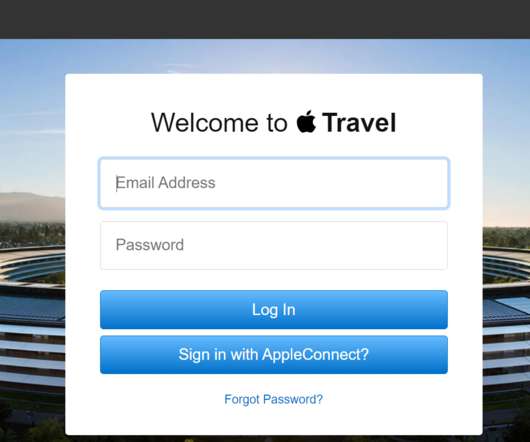
JANUARY 18, 2021
While conducting reconnaissance and fingerprinting the experts found three Apple hosts running a content management system (CMS) backed by Lucee , which is a dynamic, Java-based, tag and scripting language used for rapid web application development. Jaiswal and Maini shared their findings with Apple that awarded them a $50,000 bug bounty.

RFID Global Solution, Inc.
JUNE 9, 2017
Delta was honored with the Best Radio Frequency Identification Technology (RFID) Implementation award from RFID Journal in May. This award recognizes the airline’s industry-leading baggage handling strategy. And this isn’t the only recognition Delta’s RFID implementation has received.
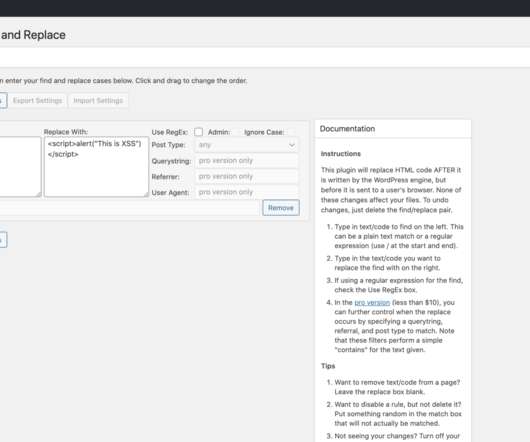
Security Affairs
APRIL 28, 2020
“An attacker could use this vulnerability to replace a HTML tag like with malicious Javascript. This would cause the malicious code to execute on nearly every page of the affected site, as nearly all pages start with a HTML tag for the page header, creating a significant impact if successfully exploited.”

Unwritten Record
OCTOBER 19, 2021
Currently, Batch 4 is tagged and ready, while Batch 5 is being tagged as we speak. List of Finding Aid Tags from Batches 4 and 5: Batch 4: Automobiles A-K – StillPixFindingAid. Awards-Nobel and Pulitzer – StillPixFindingAid. Aviation – StillPixFindingAid. Black History – StillPixFindingAid.
Security Affairs
APRIL 23, 2023
Abandoned Eval PHP WordPress plugin abused to backdoor websites CISA adds MinIO, PaperCut, and Chrome bugs to its Known Exploited Vulnerabilities catalog At least 2 critical infrastructure orgs breached by North Korea-linked hackers behind 3CX attack American Bar Association (ABA) suffered a data breach,1.4

RFID Global Solution, Inc.
JANUARY 31, 2019
Additional sessions will help airlines learn how to evaluate RFID tags and readers for their applications, as well as how to deploy solutions to enhance customer service and improve the bottom line.

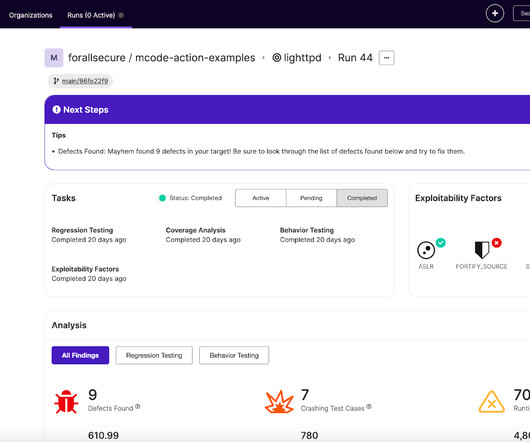
ForAllSecure
OCTOBER 18, 2022
tagged Docker image and click Next to configure the corresponding Mayhemfile. Mayhem is an award-winning AI that autonomously finds new exploitable bugs and improves your test suites. Instructions: Navigate to the Create New Run page. Select the 1.4.15 Mayhem should be able to find the defect for the lighttpd target within 90 seconds.

Rocket Software
APRIL 15, 2019
Their projects were targeted towards several specific categories, with prizes being awarded to each category winner. Or how can locating and geo-tagging places in nature that need to be cleaned sustain the global #trashtag movement? With Rocketeers as mentors, in the end a dozen teams made it to final presentations.

Info Source
FEBRUARY 15, 2019
New artificial intelligence capabilities were also introduced to automate document handling and related processes, such as automatic tagging and classification. For more information, visit [link]. .

Information Management Resources
DECEMBER 26, 2017
Anyway, the awards for online learning and systems, etc. Award Category, followed by nominees, then the “winner, err loser” – you choose the spin! Award Category, followed by nominees, then the “winner, err loser” – you choose the spin! Our final award on this fine day. Bottom Line.

ChiefTech
MARCH 17, 2009
Alex Mancheste r nudged me the other day and asked if I could help get the word out about Step Two Design's 2009 Intranet Innovation Awards. Now in its third year, the aim of the awards are to: "celebrate new ideas and innovative approaches to the design and delivery of intranets. My, doesn't time fly.

Security Affairs
MAY 23, 2022
Google’s Threat Analysis Group (TAG) uncovered campaigns targeting Android users with five zero-day vulnerabilities. Google’s Threat Analysis Group (TAG) researchers discovered three campaigns, between August and October 2021, targeting Android users with five zero-day vulnerabilities. ” continues the report.

ChiefTech
NOVEMBER 25, 2008
In the meantime, just a quick mention about the NSW KM Forum meeting, which featured Matt Moore and Serena Joyner - I don't have any notes to share, but Matt's slide are already available online and Serena used this video from Step Two's Intranet Innovation awards as part of her presentation.

The Last Watchdog
OCTOBER 19, 2021
In essence, paths in Wildland are like tags, which allow you to organize, sort, search through, etc., Fourthly, Wildland natively implements data multi-categorization. Every data container can be assigned more than one address/path and can be accessed using any of them. your data in many ways.

Brandeis Records Manager
MARCH 18, 2017
Records stories permeate the daily news: the recent front page-headlining gaffe at the Oscars awards was a good (bad?) The wrong envelope was delivered to the presenters of the most important award in the program. Records and Records Management Needs Are Everywhere. old fashioned RM error. In our “Is not!” “Is,

CILIP
MARCH 12, 2020
ve lived through Pinterest, library services offered via Second Life, social tagging in cataloguing and more 23 Things programmes than I want to think about. The better that the research is perceived to be, the more money that institution/department is awarded for more research. ve seen many trends come and go. However, in this time I?ve

IBM Big Data Hub
JANUARY 26, 2024
Here’s a comprehensive recap of everything we launched in 2023, awards and links to the latest update and how you can get started with each enhancement. With Instana Logging, no manual tagging or instrumentation is required to get to the high-fidelity view of logs in context! ” To learn more read the press announcement.

Troy Hunt
JUNE 8, 2018
I just posted about how I won the European Security Blogger Award Grand Prix Prize for the Best Overall Security Blog and per the title of this post, a couple of hours later Scott Helme and I backed it up with this at the SC Awards : To us! ?? Scott_Helme showing off his much deserved @SCmagazineUK award!

eDiscovery Daily
MAY 1, 2024
This session was a great tag team style presentation with Charles Lavallee and Tom Skelly with Infinnium, discussed data governance and Mike Gaudet and Antonio Rega with JSHeld discussed the importance of privacy and data analysis.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content