US CISA Aims to Expand Automated Malware Analysis Support
Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 state-of-malware-analysis
state-of-malware-analysis 
Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.

Lenny Zeltser
SEPTEMBER 26, 2019
What malware analysis approaches work well? The following discussion–captured as an MP3 audio file –offers friendly advice from 5 malware analysts. 1:05) How has your approach to examining malware changed over the years? (7:17) 7:17) What role do automated sandboxes play in the analysis process? (14:30)
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
APRIL 15, 2024
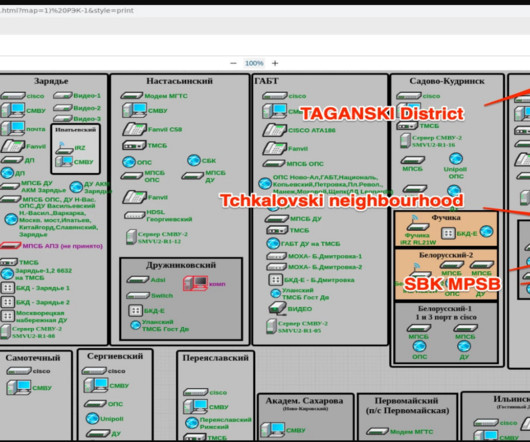
The Ukrainian hacking group Blackjack used a destructive ICS malware dubbed Fuxnet in attacks against Russian infrastructure. ” states the website. ” reads the analysis published by Claroty. ” reads the analysis published by Claroty. Access to 112 Emergency Service. YouTube Video 1 , YouTube Video 2 ).
Security Affairs
DECEMBER 1, 2023
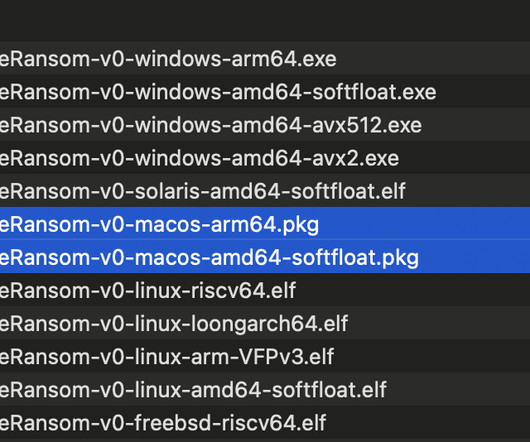
The popular cyber security researcher Patrick Wardle published a detailed analysis of the new macOS ransomware Turtle. Wardle pointed out that since Turtle was uploaded on Virus Total, it was labeled as malicious by 24 anti-malware solutions, suggesting it is not a sophisticated threat. concludes the analysis. Troj.Undef”).
Security Affairs
APRIL 14, 2024
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
Security Affairs
DECEMBER 3, 2023
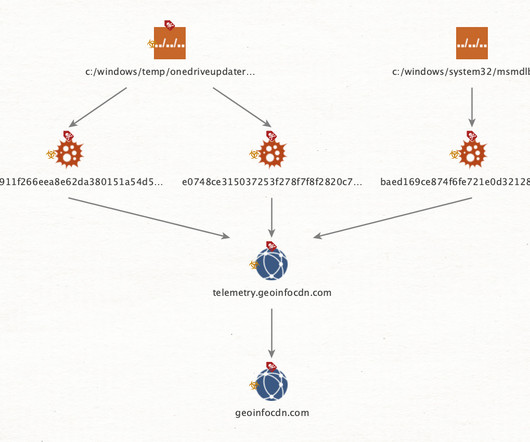
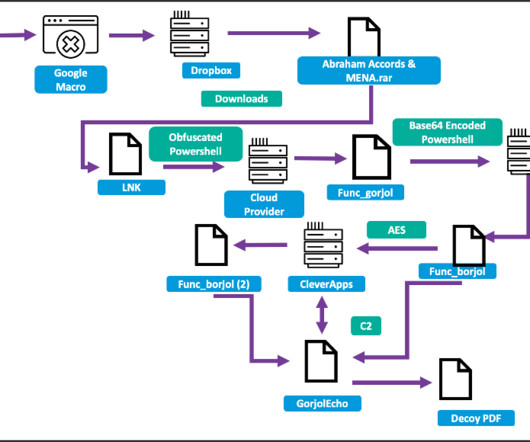
Threat actors are using the Agent Raccoon malware in attacks against organizations in the Middle East, Africa and the U.S. The malware was used in attacks against multiple industries, including education, real estate, retail, non-profit organizations, telecom companies, and governments.

The Last Watchdog
APRIL 2, 2024
Related: AI makes scam email look real Fresh evidence comes from Mimecast’s “The State of Email and Collaboration Security” 2024 report. They no longer bother with malware or link, instead focusing more so than ever on human failings. New AI risks have lit a fire under IT teams. And it’s paying off to the tune of $2.7

Security Affairs
SEPTEMBER 26, 2023
A new campaign is spreading Xenomorph malware to Android users in the United States, Spain, Portugal, Italy, Canada, and Belgium. Researchers from ThreatFabric uncovered a new campaign spreading Xenomorph malware to Android users in the United States and all over the world. that was significantly improved.

Security Affairs
OCTOBER 18, 2023
Google’s Threat Analysis Group (TAG) reported that in recent weeks multiple nation-state actors were spotted exploiting the vulnerability CVE-2023-38831 in WinRAR. In September, CERT-UA observed the FROZENLAKE group exploitingthe WinRAR flaw to deploy malware in attacks aimed at energy infrastructure.
Security Affairs
JANUARY 6, 2024
billion claim arising from the NotPetya malware incident. known as Merck Sharp & Dohme (MSD) outside the United States and Canada, is an American multinational pharmaceutical company. The analysis conducted on the ransomware revealed it was designed to look like ransomware but was wiper malware designed for sabotage purposes.

KnowBe4
OCTOBER 19, 2023
October 18, 2023, the Cybersecurity Infrastructure and Security Agency (CISA), the National Security Agency (NSA), the Federal Bureau of Investigation (FBI), and the Multi-State Information Sharing and Analysis Center (MS-ISAC) released a joint guide, Phishing Guidance: Stopping the Attack Cycle at Phase One.
Security Affairs
JANUARY 1, 2024
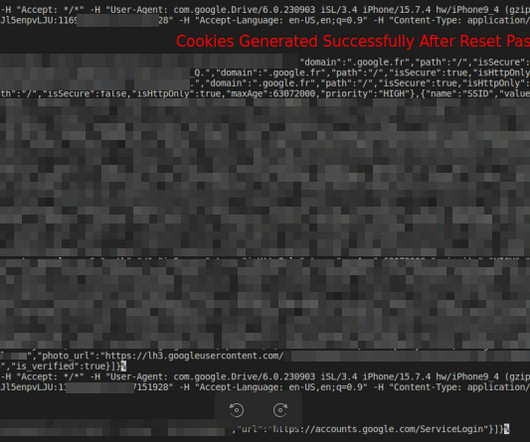
Subsequently, other malware integrated the exploit, including Rhadamanthys, Risepro, Meduza , Stealc Stealer and recently the White Snake. The researchers discovered that the malware targets Chrome’s token_service table of WebData to extract tokens and account IDs of chrome profiles logged in. ” continues the report. .
Security Affairs
JANUARY 21, 2024
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Patch it now!

eSecurity Planet
FEBRUARY 14, 2024
Stateful inspection is a firewall feature that filters data packets based on the context of previous data packets. An understanding of how stateful inspection works, the key pros and cons, and its use cases provides important insight into how stateful inspection can be used successfully in a security stack.
Security Affairs
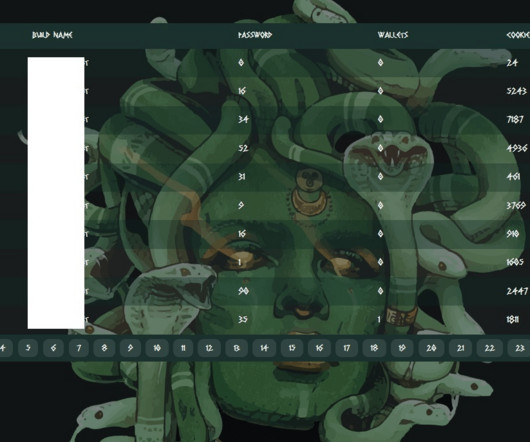
JULY 3, 2023
The malware also targets crypto wallet extensions, password managers, and 2FA extensions. The authors are actively developing malware to evade detection, but no specific attacks have been attributed to the Meduza Stealer to date. The malware admin declared that their operations do not involve any ransom activities.

Security Affairs
OCTOBER 19, 2023
I’m proud to announce the release of the 11th edition of the ENISA Threat Landscape (ETL) on the state of the cybersecurity threat landscape. The Europen Agency for cybersecurity ENISA releases its ENISA Threat Landscape 2023 (ETL) report , which is the annual analysis of the state of the cybersecurity threat landscape.
Lenny Zeltser
JANUARY 6, 2021
Malware analysis sits at the intersection of incident response, forensics, system and network administration, security monitoring, and software engineering. As someone who’s helped thousands of security professionals learn how to analyze malware at SANS Institute , I have a few tips for how you can get started.
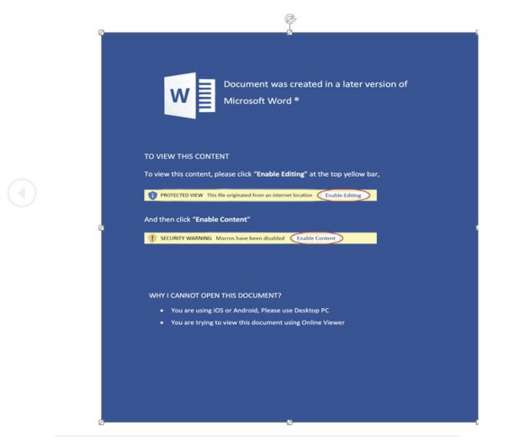
Security Affairs
SEPTEMBER 29, 2022
The Russia-linked APT28 group is using mouse movement in decoy Microsoft PowerPoint documents to distribute malware. The Russia-linked APT28 employed a technique relying on mouse movement in decoy Microsoft PowerPoint documents to deploy malware, researchers from Cluster25 reported. ” reads the analysis published by Cluster25.
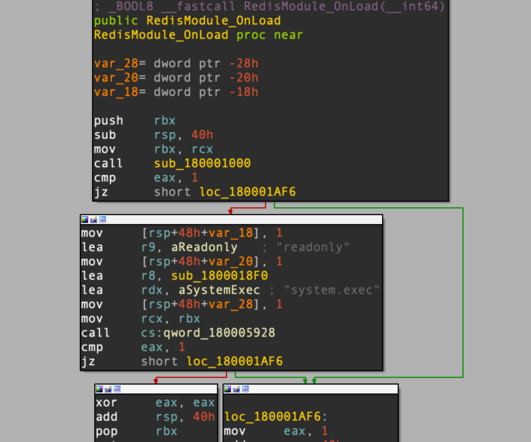
Security Affairs
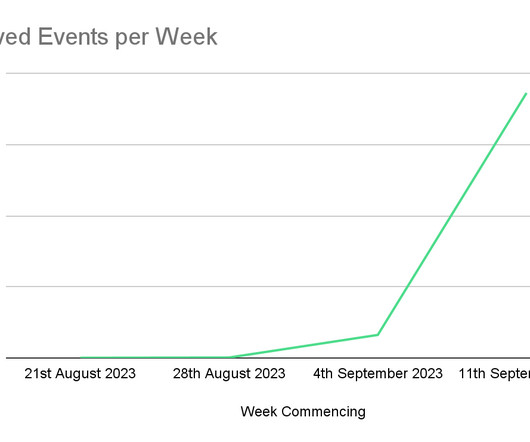
SEPTEMBER 22, 2023
surge during the week leading up to the publication of their analysis. P2Pinfect infections have been reported in China, the United States, Germany, the United Kingdom, Singapore, Hong Kong and Japan. ” reads the analysis published by Cado Security Labs. According to the researchers, traffic experienced a 12.3%
Security Affairs
AUGUST 31, 2023
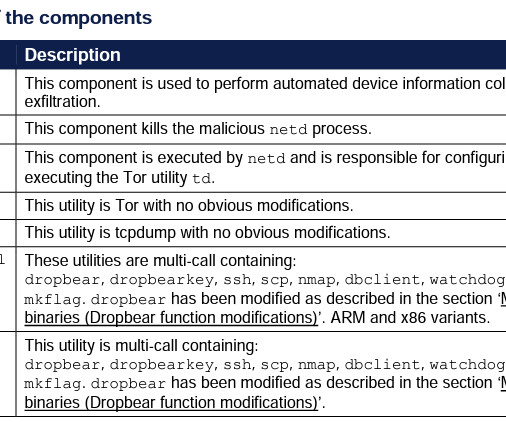
Russia-linked threat actors have been targeting Android devices of the Ukrainian military with a new malware dubbed Infamous Chisel. The GCHQ’s National Cyber Security Centre (NCSC) and agencies in the United States, Australia, Canada, and New Zealand have published an analysis of the Android malware.

Security Affairs
MAY 13, 2020
The United States Cyber Command (USCYBERCOM) has uploaded five new North Korean malware samples to VirusTotal. The United States Cyber Command (USCYBERCOM) has shared five new malware samples attributed to the North Korea-linked Lazarus APT , it has uploaded the malicious code to VirusTotal.

Security Affairs
MARCH 16, 2023
In 2020 and 2021, this flaw was included by the US National Security Agency (NSA) in the list of the top 25 vulnerabilities exploited by Chinese state-sponsored hacking groups in attacks in the wild. The joint alert recommends network defenders review the Malware Analysis Report, MAR-10413062-1.v1 ” reads the advisory.
Security Affairs
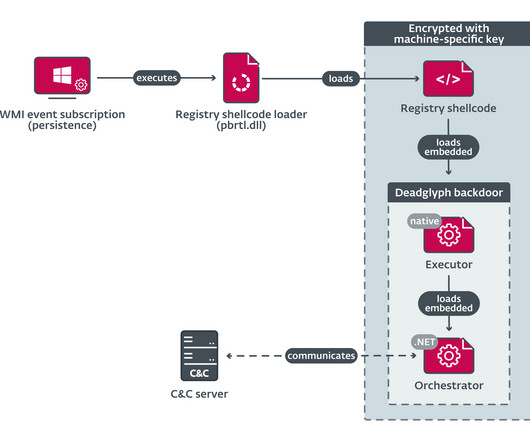
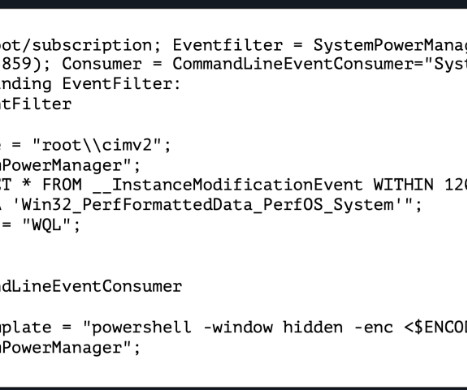
SEPTEMBER 24, 2023
Stealth Falcon is a nation-state actor active since at least 2012, the group targeted political activists and journalists in the Middle East in past campaigns. The researchers explained that unlike other malware typically using components written in only one programming language, Deadglyph uses distinct programming languages.
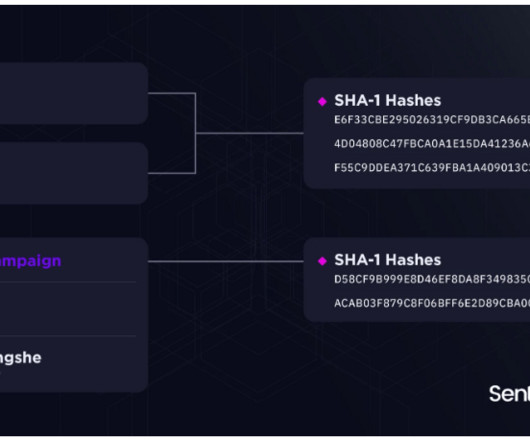
Security Affairs
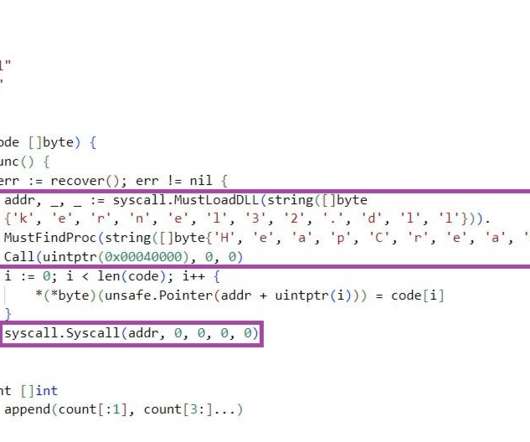
JANUARY 25, 2023
Chinese threat actor tracked as DragonSpark targets organizations in East Asia with a Golang malware to evade detection. The attackers employed an open source tool SparkRAT along with Golang malware that implements an uncommon technique to evade detection. ” reads the report published by SentineOne. exe, implemented in Golang.”

Security Affairs
NOVEMBER 12, 2021
Google revealed that threat actors recently exploited a zero-day vulnerability in macOS to deliver malware to users in Hong Kong. Google TAG researchers discovered that threat actors leveraged a zero-day vulnerability in macOS in a watering hole campaign aimed at delivering malware to users in Hong Kong.
Security Affairs
JUNE 7, 2023
aerospace defense sector with a new PowerShell malware dubbed PowerDrop. The PowerShell-based malware uses advanced techniques to evade detection, including deception, encoding, and encryption. ” reads the analysis published by Adlumin. . ” reads the analysis published by Adlumin. aerospace sector.

Security Affairs
FEBRUARY 19, 2024
He appealed the decision of a Dutch Court for granting his extradition to the United States, but it was finally extradited to the US from the Netherlands to appear in a US court. The malware is now promoted on English-speaking hacking forums, it works on both 32-bit and 64-bit operating systems. in the stolen data.
Security Affairs
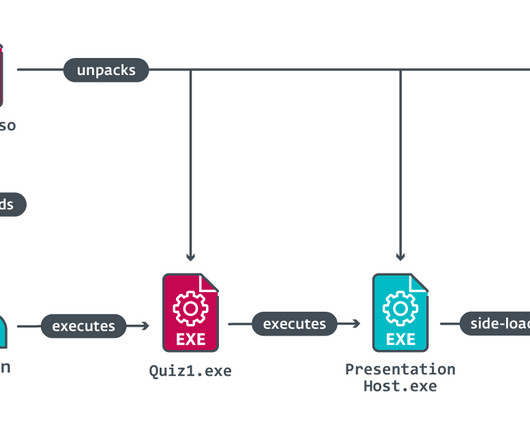
OCTOBER 1, 2023
The state-sponsored hackers deployed several tools, including a previously undocumented backdoor dubbed LightlessCan. ” reads the analysis published by ESET. ” reads the analysis published by ESET. The cyberspies impersonated Meta’s recruiters to lure employees with trojanized coding challenges. exe and Quiz2.exe,

Security Affairs
JULY 7, 2022
The report provides information about tactics, techniques, and procedures (TTPs) of the threat actors using the Maui ransomware along with indicators of compromise (IOCs) that were obtained by government experts during incident response activities and industry analysis of a Maui sample. The FBI, CISA, and the U.S.
Security Affairs
DECEMBER 12, 2023
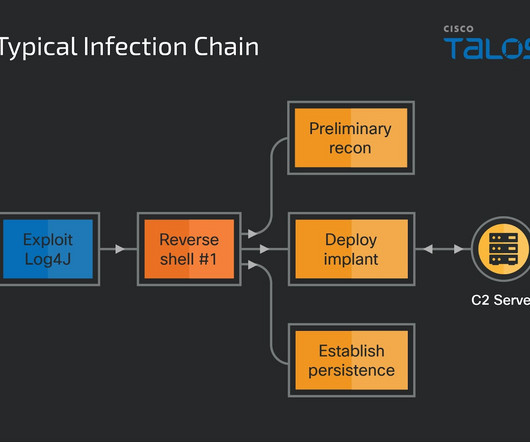
Cisco Talos researchers tracked the campaign as Operation Blacksmith, the nation-state actors are employing at least three new DLang -based malware families. ” reads the analysis published by Talos. ” reads the analysis published by Talos.
Security Affairs
JANUARY 5, 2022
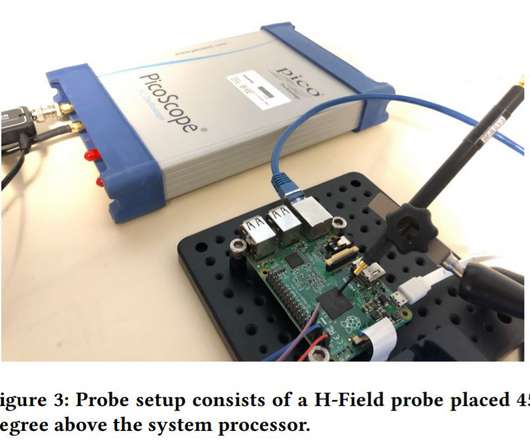
Cybersecurity researchers demonstrate how to use electromagnetic field emanations from IoT devices to detect malware. The researchers proposed a novel approach of using side channel information to identify malware targeting IoT systems. In fact, EM emanation that is measured from the device is practically undetectable by the malware.
Security Affairs
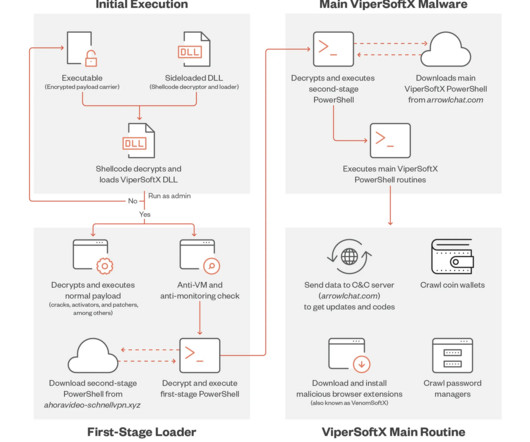
APRIL 29, 2023
A new variant of the information-stealing malware ViperSoftX implements sophisticated techniques to avoid detection. Trend Micro researchers observed a new ViperSoftX malware campaign that unlike previous attacks relies on DLL sideloading for its arrival and execution technique. ” reads the analysis published by Trend Micro.

eSecurity Planet
FEBRUARY 21, 2024
CLGs depend on two key features, proxy capability and stateful packet inspection, to block unsolicited communication. Successful implementation of a circuit-level gateway defends against unrestricted communication, which can enable network probing, malware delivery, and other attacks.
Security Affairs
JULY 8, 2023
Iran-linked APT group tracked TA453 has been linked to a new malware campaign targeting both Windows and macOS systems. The Iran-linked threat actor TA453 has been linked to a malware campaign that targets both Windows and macOS. ” reads the analysis published by Proofpoint. ” continues the analysis.
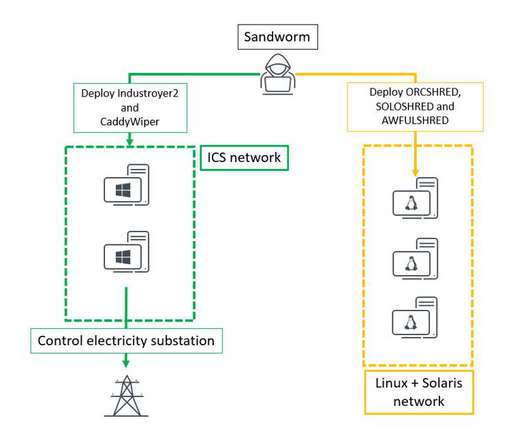
eSecurity Planet
APRIL 14, 2022
Researchers at ESET and Microsoft collaborated with CERT-UA to analyze the attacks and discovered evidence of a new variant of a known malware. Researchers at ESET and Microsoft collaborated with CERT-UA to analyze the attacks and discovered evidence of a new variant of a known malware. Latest Sandworm Attack Against Ukraine.

Security Affairs
JULY 4, 2021
Threat actors compromised the servers of Mongolian certificate authority (CA) MonPass and used its website to spread malware. Hackers compromised the servers of the Mongolian certificate authority (CA) MonPass and used its website to spread malware, reported Avast researchers. ” states the analysis published by Avast.
Security Affairs
JULY 21, 2022
A threat actor tracked as TA4563 is using EvilNum malware to target European financial and investment entities. A threat actor, tracked as TA4563, leverages the EvilNum malware to target European financial and investment entities, Proofpoint reported. ” reads the analysis published by Proofpoint.
Security Affairs
AUGUST 18, 2023
The malware and infrastructure employed in the campaign are linked to the ones observed in Operation ChattyGoblin attributed by the security firm ESET to China-linked threat actors. Bronze Starlight is a nation-state group that was observed using ransomware as means for distraction or misattribution. IP-based geolocation service. .”
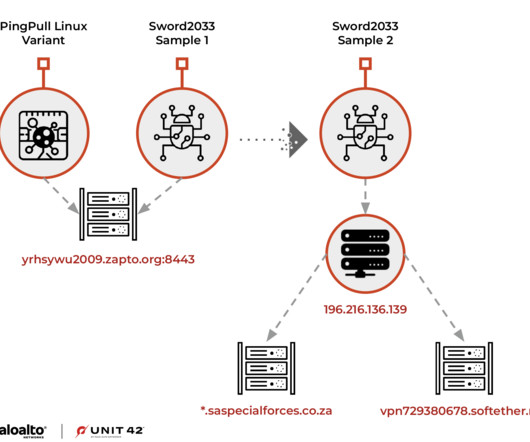
Security Affairs
APRIL 26, 2023
On March 7, 2023, the researchers found a Linux variant of the PingPull that was uploaded to VirusTotal, it had a very low detection rate (3 out of 62) “Despite a largely benign verdict, additional analysis has determined that this sample is a Linux variant of PingPull malware. ” reads the analysis published by Unit 42.
Security Affairs
DECEMBER 4, 2023
surge during the week leading up to the publication of their analysis. P2Pinfect infections have been reported in China, the United States, Germany, the United Kingdom, Singapore, Hong Kong and Japan. “It’s highly likely that by targeting MIPS, the P2Pinfect developers intend to infect routers and IoT devices with the malware.
Security Affairs
DECEMBER 31, 2023
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

Security Affairs
AUGUST 11, 2023
Threat actors employed a new variant of the SystemBC malware, named DroxiDat, in attacks aimed at African critical infrastructure. The malware was tracked as “SystemBC” based on the URI path shown in the advertisement’s panel screenshots. The malware is 8kb in size and was used as a system profiler and a simple SOCKS5-capable bot.

Security Affairs
FEBRUARY 24, 2023
Researchers warn of an evasive cryptojacking malware targeting macOS which spreads through pirated applications Jamf Threat Labs researchers reported that an evasive cryptojacking malware targeting macOS was spotted spreading under the guise of the Apple-developed video editing software, Final Cut Pro. ” continues the analysis.

eSecurity Planet
APRIL 13, 2023
The stub will then be used to unpack the file and “restore” the executable to its original state. Attackers can use compression to hide malware inside seemingly harmless and legitimate files, which can fool signature-based detection and even advanced artificial intelligence (AI)-based antivirus solutions.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content