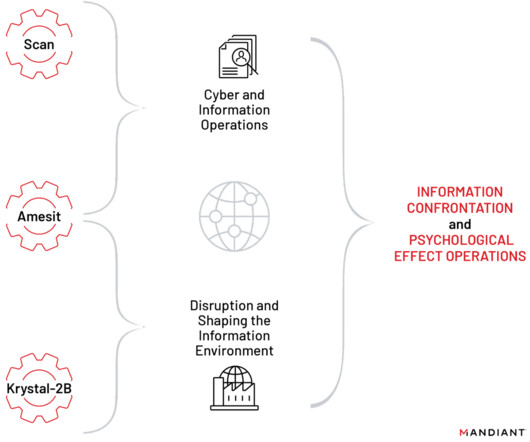
GUEST ESSAY: Successful tactics threat actors leverage to probe, compromise vulnerable networks
The Last Watchdog
FEBRUARY 7, 2022
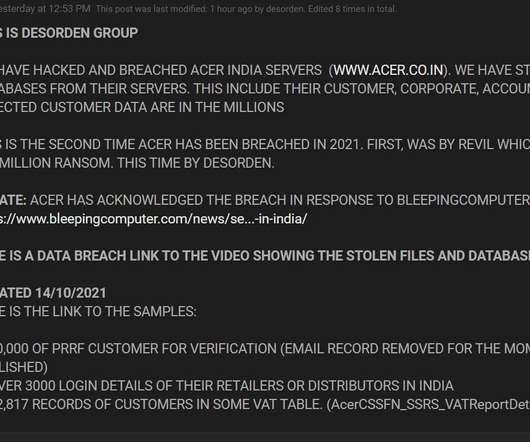
When Log4Shell first hit the street, we immediately saw attacks against almost every one of our customers. As attackers started scanning for targets, our research team repurposed their techniques resulting in a tool that we used to help our customers find vulnerable API endpoints. Scanning for viable targets.









































Let's personalize your content