Case Study: Automated Contact Tracing in HID Malaysia Manufacturing
HID Global
JANUARY 4, 2022
Case Study: Automated Contact Tracing in HID Malaysia Manufacturing. raufreiter. Tue, 01/04/2022 - 12:28.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

HID Global
JANUARY 4, 2022
Case Study: Automated Contact Tracing in HID Malaysia Manufacturing. raufreiter. Tue, 01/04/2022 - 12:28.
Rocket Software
JULY 20, 2022
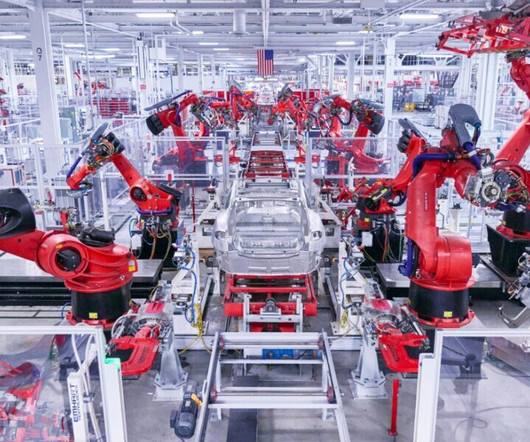
Global manufacturing companies operating within expansive ecosystems (e.g., automotive, aerospace, defense or hi-tech) are vulnerable to slowed flows of raw materials and finished goods, which can substantially disrupt manufacturing workflows and multi-tier collaboration. time-consuming. vulnerable to mistakes.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
AUGUST 21, 2023
Accelerating Data Security and Manufacturing Production for Medical Sensors by 20x with nTropy.io To protect medical devices with PKI, each device needs to have certain components (certificates, keys) embedded during the manufacturing process. They offer security solutions to clients in MedTech, V2X, and Industrial manufacturing.

Thales Cloud Protection & Licensing
OCTOBER 19, 2022
Manufacturing needs to adopt a Zero Trust approach to mitigate increased cyber threats. Long gone is the time when manufacturing systems and operations were siloed from the Internet and, therefore, were not a cybersecurity target. Thu, 10/20/2022 - 06:20. Survey’s key findings.

Dark Reading
AUGUST 2, 2022
Netwrix study reveals that manufacturing organizations experienced these types of attacks more often than any other industry surveyed.

Data Breach Today
JULY 7, 2020
Study Suggests Actionable Recommendations Would Improve IoT Security With more than 1,000 IoT security guidelines, recommendations and best practices, which ones should an organization follow?

OpenText Information Management
AUGUST 17, 2018
I recently attended the Manufacturers Leadership Summit hosted by Frost & Sullivan in LA. This three-day event was full of presentations, case studies and discussions on the journey to Manufacturing 4.0. The Manufacturing Leadership Summit is … The post Manufacturing 4.0? Industry 4.0?
KnowBe4
DECEMBER 12, 2022
based enterprise manufacturing organization cut their Phish-prone Percentage™ (PPP) by more than 80% after five months using the KnowBe4 security awareness training and simulated phishing platform.
Security Affairs
APRIL 16, 2024
Nexperia is a semiconductor manufacturer headquartered in Nijmegen, the Netherlands. The Dark Angels (Dunghill) ransomware group claims responsibility for hacking chipmaker Nexperia and stealing 1 TB of the company’s data. It is a subsidiary of the partially state-owned Chinese company Wingtech Technology.
Security Affairs
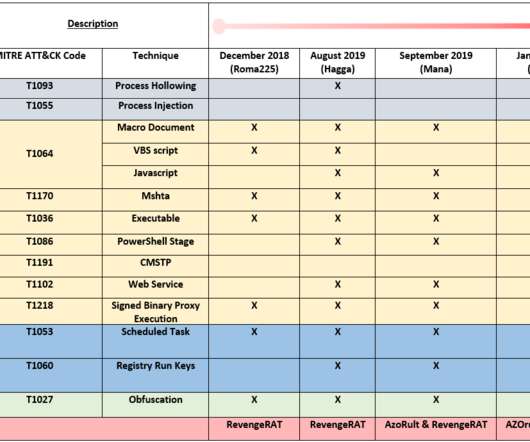
MAY 22, 2020
ZLab researchers spotted a new malicious espionage activity targeting Italian companies operating worldwide in the manufacturing sector. This actor was first spotted by PaloAlto’s UNIT42 in 2018 during wide scale operations against technology, retail, manufacturing, and local government industries in the US, Europe and Asia.

Dark Reading
JUNE 17, 2021
Information-stealing malware makes up about a third of attacks, a study finds, but companies worry most about ransomware shutting down production.

IBM Big Data Hub
OCTOBER 3, 2023
According to a recent study by IBM Security, the 2023 X-Force Threat Intelligence Index established the retail and wholesale industry as the fifth-most targeted industry in 2022, with cybercriminals increasingly looking to exploit the trove of data gathered from the billions of transactions sellers process online.

Hunton Privacy
MAY 10, 2016
On May 9, 2016, the Federal Trade Commission announced it had issued Orders to File a Special Report (“Orders”) to eight mobile device manufacturers requiring them to, for purposes of the FTC’s ongoing study of the mobile ecosystem, provide the FTC with “information about how [the companies] issue security updates to address vulnerabilities in smartphones, (..)

Schneier on Security
DECEMBER 30, 2022
Existing studies show that loudspeaker reverberation can inject speech into motion sensor readings, leading to speech eavesdropping. While more devastating attacks on ear speakers, which produce much smaller scale vibrations, were believed impossible to eavesdrop with zero-permission motion sensors.

The Last Watchdog
FEBRUARY 21, 2024
That’s the assessment of the 2024 Edelman Trust Barometer , a study highlighting the rapid erosion of digital trust, to the point of exacerbating polarized political views. This tug-and-pull is happening in an operating environment where digital innovation, from a global perspective, is being bungled. It’s not just in smart homes,” he says.

Schneier on Security
JUNE 17, 2022
Computer scientists at the University of California San Diego proved in a study published May 24 that minute imperfections in phones caused during manufacturing create a unique Bluetooth beacon , one that establishes a digital signature or fingerprint distinct from any other device. This new research shows that that’s not enough.

Info Source
OCTOBER 16, 2023
During this time they have established long-lasting, trustworthy business relationships with all manufacturers as well as with thousands of individuals throughout the globe covering different industries, including Digital Color Press, Large Format Printers, B&W and Color Production Devices, Direct-to-Garment and Direct-to-Film Printers.

IBM Big Data Hub
OCTOBER 24, 2023
Proven FinOps success: three case studies The below three case studies showcase the success of IBM Consulting’s FinOps methods: An American manufacturer needed optimization for multi-cloud environment and DevOps activities. They began in the initial stages of the FinOps journey and maturity.
IBM Big Data Hub
APRIL 27, 2023
A recent IBM study found that global executives cite inadequate data (41%) as the biggest obstacle to their ESG progress, followed by regulatory barriers (39%), inconsistent standards (37%) and inadequate skills (36%). 94% more of Enabled believe ERPs are helping manage manufacturing sustainability goals.
IBM Big Data Hub
JUNE 20, 2023
According to Warranty Week , claims totaling 46 billion USD were paid by the global automotive Original Equipment Manufacturers in 2021. avoiding warranty issues through simulation), manufacturing (e.g., 54 billion USD in accruals have been made. and Canada. Additionally, the warranty costs are still handed back to the supplier.
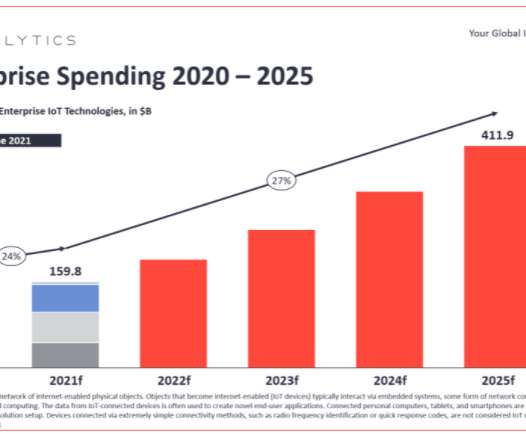
eSecurity Planet
NOVEMBER 1, 2021
The European Union is poised to place more demands on manufacturers to design greater security into their wireless and Internet of Things (IoT) devices. Manufacturers will be required to adhere to the new cybersecurity safeguards when designing and producing these products.

Security Affairs
JANUARY 31, 2020
“Our goal was to test the validity of these methods,” said Rick Ayers, the NIST digital forensics expert who led the study. “Do The results of the NIST study will also help labs choose the right tools for the job. The study addresses methods that work with Android phones. Do they reliably produce accurate results?”.

Security Affairs
MAY 16, 2023
Teltonika Networks is a leading manufacturer of networking solutions, widely adopted in industrial environments, including gateways, LTE routers, and modems. The study focuses on the RUT241 and RUT955 cellular routers manufactured by Teltonika, and on the Remote Management System (RMS) provided by the vendor.

Security Affairs
FEBRUARY 9, 2023
China is currently the country with the largest number of Android mobile devices, but a recent study conducted by researchers from the University of Edinburgh and the Trinity College of Dublin revealed that top-of-the-line Android devices sold in the country are shipped with spyware. Chinese manufacturers have yet to comment on the research.

ChiefTech
MARCH 24, 2013
While a bit light on details, I'm not going to complain about this positive story in the ITPro section of the Fairfax newspapers about two packaging manufacturing companies using enterprise social software to help their bottom-line.

Info Source
OCTOBER 4, 2023
Our main goal is to work closely with Executives, Product Managers and Marketing Strategists of Production Devices manufacturers to enlighten and provide them all the necessary knowledge to optimise their performance and achieve their business targets.”

The Last Watchdog
JULY 10, 2023
The new consumer research studied and focused on banking, the Internet of Things (IoT) and smart cities and found the following key takeaways from across the world: •Only 19% of respondents don’t worry about the security of their data. •36% UTIMACO is one of the world’s leading manufacturers in its key market segments.

IBM Big Data Hub
JANUARY 25, 2024
Many managers in asset-intensive industries like energy, utilities or process manufacturing, perform a delicate high-wire act when managing inventory. 1 Another study revealed: The swinging pendulum The MRO spare parts inventory varies depending on the industry and equipment, ranging from specific items to encompassing more basic supplies.

Thales Cloud Protection & Licensing
NOVEMBER 6, 2019
In the absence of IoT security regulations, many smart product manufacturers simply release new devices that lack built-in security measures and have not undergone proper security review and testing. Take manufacturing, for instance. Such disruption could have serious consequences depending on the type of organization that’s affected.

Security Affairs
NOVEMBER 1, 2021
“According to Vladimir Kononovich, some manufacturers rely on security through obscurity, with proprietary protocols that are poorly studied and the goal of making it difficult for attackers to procure equipment to find vulnerabilities in such devices. Wincor is currently owned by ATM manufacturer giant Diebold Nixdorf.

IBM Big Data Hub
APRIL 25, 2024
An early case study of BPR was Ford Motor Company, which successfully implemented reengineering efforts in the 1990s to streamline its manufacturing processes and improve competitiveness. Organizations of all sizes and industries implement business process reengineering.
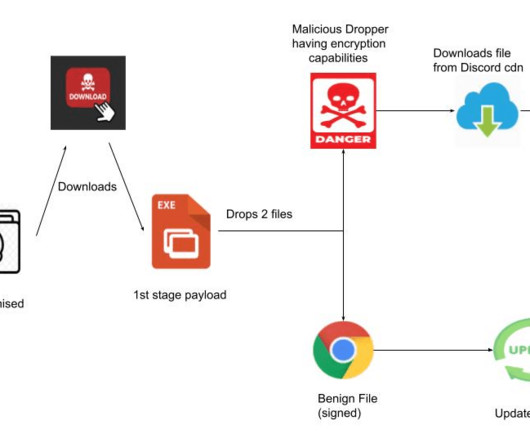
Security Affairs
JULY 5, 2023
“The sample Stealer-as-a-Ransomware variant analyzed in this case study employs a deceptive FAKEUPDATES campaign to lure in its targets, tricking them into promptly updating their browsers. The malware allows operators to steal information from various browsers, it also supports ransomware capabilities.

Security Affairs
FEBRUARY 13, 2019
” Let’s go to our case study: I received a scan request for a PDF file that was reported to support an antivirus vendor, and it replied that the file was not malicious. Then I thought, “Why not turn a PDF analysis into an article?” About the author : Zoziel Freire.

Krebs on Security
JUNE 25, 2019
” “At present, pre-installed partners cover the entire mobile phone industry chain, including mobile phone chip manufacturers, mobile phone design companies, mobile phone brand manufacturers, mobile phone agents, mobile terminal stores and major e-commerce platforms,” reads a descriptive blurb about the company.

Schneier on Security
MAY 1, 2018
They've already used the tool to study a bunch of different IoT devices. Dahua is also a security camera manufacturer, although Amcrest's website makes no references to Dahua. Amcrest customer service informed us that Dahua was the original equipment manufacturer. Halo Smoke Detector.

Adapture
JANUARY 25, 2022
Case Studies/Examples Travel Management Solution Managing travel expenses and workflows is a massive headache for any organization, let alone a multibillion-dollar company with tens of thousands of employees. ADAPTURE has implemented all Smartsheet technology and products in clients’ workflows and processes.

IBM Big Data Hub
DECEMBER 8, 2023
A close-up of the SDV architecture The infrastructure layer This layer includes not only the vehicle but also the telco equipment, roadside units, smart city systems and similar components, as well as various backend systems of the original equipment manufacturers (OEMs).

AIIM
MARCH 7, 2022
Consider an especially tense series of conversations witnessed by management at a manufacturing company. In a recent study by OnePoll of 1,500 workers in the UK and another 1,500 in the US, 61% of US respondents at 46% of UK respondents would consider leaving if a new employer provided better apps or software systems for employees.

Synergis Software
NOVEMBER 2, 2018
I had the pleasure of attending the Delaware Valley Industrial Resource Center (DVIRC) Manufacturing Summit on October 12 at The Fuge in Warminster where Valerie Gervais was a featured keynote. Anthropologists, by practice, start with a blank page when studying new cultures or peoples. VP HR, Saint-Gobain.

Thales Cloud Protection & Licensing
NOVEMBER 23, 2023
Accelerating manufacturers’ time-to-market through open innovation madhav Fri, 11/24/2023 - 05:09 The manufacturing industry is in the midst of a significant digital transformation, where organizations are leveraging all different types of technologies to stay competitive and meet customer demands.

Security Affairs
DECEMBER 19, 2023
BlackCat/ALPHV ransomware gang has been active since November 2021, the list of its victims is long and includes industrial explosives manufacturer SOLAR INDUSTRIES INDIA , the US defense contractor NJVC , gas pipeline Creos Luxembourg S.A. , the fashion giant Moncler , the Swissport , NCR , and Western Digital.

Info Source
AUGUST 1, 2023
The excellence in its methodology has made Infosource the preferred and chosen marketing intelligence company for most leading manufacturers active in the EMEA region. Media enquiries: Michelle Oelschig, Scarlet Letter Contact details: 083-636-1766, michelle@scarletletter.co.za

AIIM
JANUARY 19, 2018
Hundreds of thousands of manufacturing jobs have been lost due to automation. A recent Oxford study paints an even drearier picture, one where 47% of total US employment is at risk for automation in the coming decade. Automation is claiming jobs. Thousands more have been claimed in finance due to the automation of the stock market.

Adam Levin
JUNE 30, 2020
Manufacturing giant Honda had its networks brought to a standstill by just such an attack. A 2019 study showed that 80 percent of IT business leaders expected a critical breach or a successful cyberattack within a year, double what a similar study had indicated in 2015. 1-99-employee companies are a target.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content