Dark Reading Launches New Section Dedicated to ICS/OT Security
Dark Reading
OCTOBER 26, 2022
ICS/OT Security joins the lineup of 14 cybersecurity topic sections on the media site.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 ics-ot-security
ics-ot-security 
Dark Reading
OCTOBER 26, 2022
ICS/OT Security joins the lineup of 14 cybersecurity topic sections on the media site.

Dark Reading
MARCH 9, 2023
These agile controls and processes can help critical infrastructure organizations build an ICS security program tailored to their own risk profile.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
SEPTEMBER 6, 2023
MITRE and CISA released a Caldera extension for OT that allows the emulation of attacks on operational technology systems. MITRE Caldera is an open-source adversary emulation platform that helps cybersecurity practitioners to automate security assessments. ” reads the announcement for the product.

Dark Reading
OCTOBER 11, 2022
The IT security executive led ICS/OT, IT/OT integration, and other security programs, as well as diversity and inclusion efforts in the industry.

Security Affairs
APRIL 14, 2022
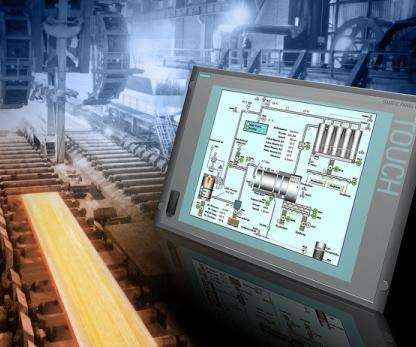
The US government agencies warned of threat actors that are targeting ICS and SCADA systems from various vendors. “APT actors have developed custom-made tools that, once they have established initial access in an OT network, enables them to scan for, compromise, and control certain ICS/SCADA devices” reads the advisory.
Security Affairs
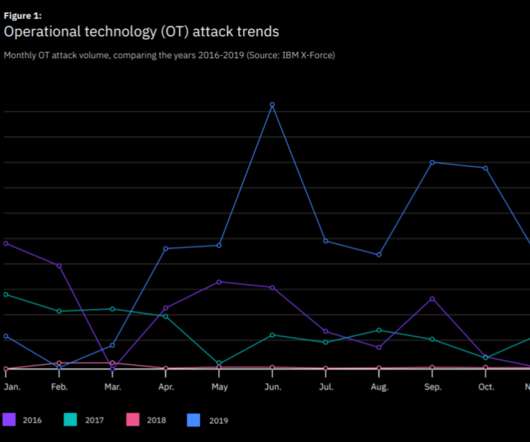
FEBRUARY 11, 2020
According to IBM, OT attacks increased by over 2000 percent in 2019, most of them involved the Echobot IoT malware. IBM’s 2020 X-Force Threat Intelligence Index report analyzes the threat landscape in 2019, the experts observed a spike in the number of OT attacks. “ OT attacks hit an all-time high. ” concludes IBM.

Security Affairs
JULY 14, 2023
Cybersecurity and Infrastructure Security Agency (CISA) is warning of two vulnerabilities affecting Rockwell Automation ControlLogix EtherNet/IP (ENIP) communication module models that could be exploited to achieve remote code execution and trigger a denial-of-service condition. . ” continues the ICS advisory. .”

Dark Reading
APRIL 15, 2022
Omdia Senior Analyst Hollie Hennessy says the new threat to multiple ICS and SCADA devices underscores the importance of a rapid response to IoT and OT security risks.

The Last Watchdog
AUGUST 26, 2019
Andrea Carcano’s journey to co-founding a security company in the vanguard of defending critical infrastructure began at a tender age. He went on to earn a masters degree in cybersecurity, during which time he won a scholarship from the European Commission to craft a proof of concept attack against an industrial control system (ICS.)

The Last Watchdog
AUGUST 26, 2019
Andrea Carcano’s journey to co-founding a security company in the vanguard of defending critical infrastructure began at a tender age. He went on to earn a masters degree in cybersecurity, during which time he won a scholarship from the European Commission to craft a proof of concept attack against an industrial control system (ICS.)

The Last Watchdog
JANUARY 7, 2019
The global cybersecurity community is keenly aware of these developments and earnest discussions are underway about how to deal with the attendant security exposures. Initially introduced in 2005, CVSS is a framework for rating the severity of security vulnerabilities in software. Barda: Yes. The risks are growing for two reasons.

Security Affairs
JULY 26, 2020
National Security Agency (NSA) and the Cybersecurity and Infrastructure Security Agency (CISA) issued an alert warning of cyber attacks targeting critical infrastructure across the U.S. critical infrastructure facilities take immediate actions to secure their OT assets. interests or retaliate for perceived U.S.
Security Affairs
FEBRUARY 7, 2021
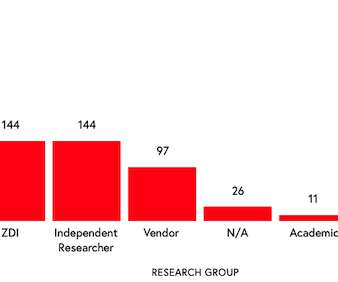
The number of vulnerabilities discovered in industrial control system (ICS) products surged in 2020, security firm Claroty reports. Experts reported that 449 vulnerabilities were disclosed affecting ICS products from 59 vendors during 2H 2020. ” reads the report published by Claroty. continues the report.

Security Affairs
JULY 1, 2021
The US CISA has released the Ransomware Readiness Assessment (RRA), a new ransomware self-assessment security audit tool. RRA could be used by organizations to determine their level of exposure to ransomware attacks against their information technology (IT), operational technology (OT), or industrial control system (ICS) assets.
Security Affairs
APRIL 19, 2021
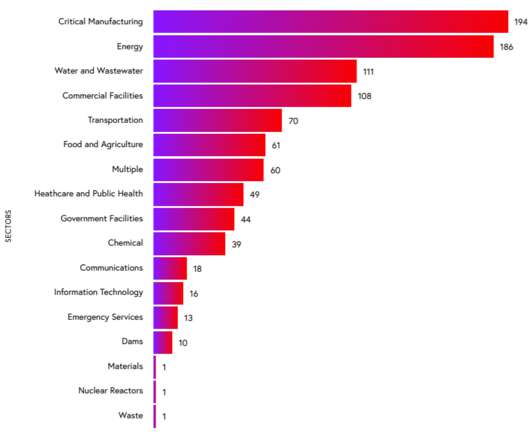
Over the years, the number of attacks against ICS/SCADA systems used by industrial organizations worldwide has rapidly increased. Many security firms highlighted the risks related to attacks targeting OT networks used in utilities. ” states the FireEye’s report. ” states the FireEye’s report.

Security Affairs
SEPTEMBER 18, 2020
Cybersecurity and Infrastructure Security Agency (CISA) has been named a Top-Level Root CVE Numbering Authority (CNA). CISA will be in charge of ICS and medical device vendors that are CNAs, it will supervise the process to assign CVE identifiers. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->.

Security Affairs
AUGUST 21, 2021
The US Cybersecurity and Infrastructure Security Agency (CISA) released guidance on how to prevent data breaches resulting from ransomware attacks. The post US CISA releases guidance on how to prevent ransomware data breaches appeared first on Security Affairs. Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini.
Security Affairs
MAY 17, 2023
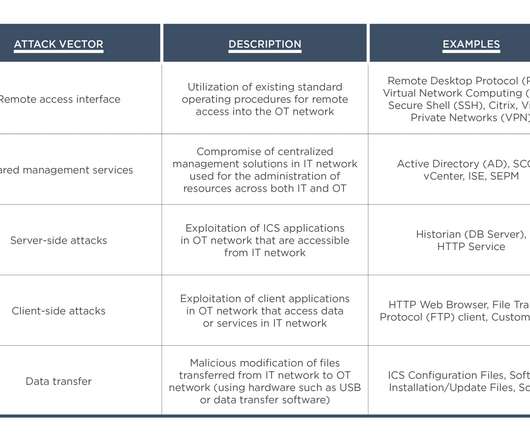
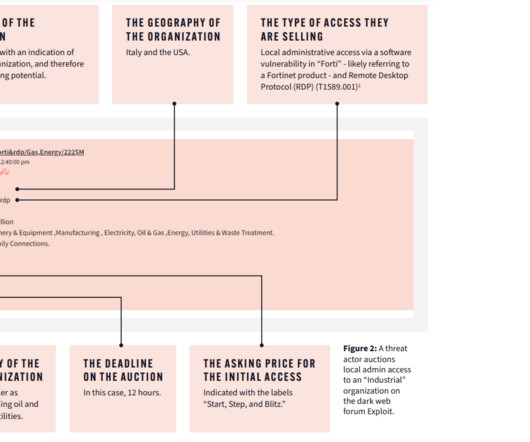
Threat actors auction initial access to remote software, RDP access, VPNs, and stolen credentials, allowing attacks to use these accesses to establish a foothold in the target organization and launch the attack on both IT and OT infrastructure. We are in the final!

The Security Ledger
FEBRUARY 14, 2023
Cyberattacks on industrial control systems (ICS) jumped in 2022, with an 87% jump in ransomware attacks and a 35% increase in the number of ransomware groups targeting industrial control and operational technology (OT) systems, according to a report by Dragos Security. Read the whole entry. »
Security Affairs
AUGUST 20, 2021
During the first half of 2021, 637 vulnerabilities affecting industrial control system (ICS) products were published, affecting products from 76 vendors. The company reported that during the first half of 2021, 637 vulnerabilities affecting industrial control system (ICS) products were published, affecting products from 76 vendors.

Security Affairs
JUNE 26, 2022
ICS malware like TRITON , which experts associated with Russia-linked APT group XENOTIME , has offensive capabilities to shut down industrial safety controls and cause extensive damages to industrial facilities. At this time it is not clear why the safety mechanisms in place did not prevent the explosion. “On March 24 the U.S.

The Security Ledger
OCTOBER 28, 2021
In this Spotlight edition of the podcast, we’re joined by Curtis Simpson, the Chief Information Security Officer at Armis. IoT and OT (operation technology) deployments are growing and pose challenges to organizations that are still. As always, you can check our full conversation in our latest Security Ledger podcast at Blubrry.

Security Affairs
FEBRUARY 20, 2020
More than 400 flaws affecting industrial control systems (ICS) were disclosed in 2019, more than 100 were zero-day vulnerabilities. According to a report published by Dragos, the experts analyzed 438 ICS vulnerabilities that were reported in 212 security advisories, 26% of advisories is related to zero-day flaws.

Dark Reading
DECEMBER 8, 2020
National Grid Partners, Saudi Aramco Energy Ventures, and Hewlett Packard Enterprise led the latest funding round for the ICS/OT security company.
Security Affairs
APRIL 2, 2023
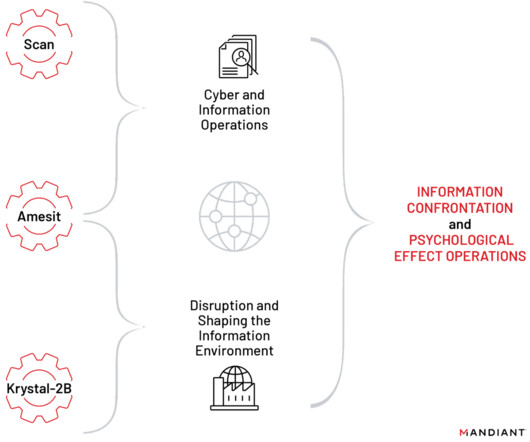
These projects include tools, training programs, and a red team platform for exercising various types of offensive cyber operations, including cyber espionage, IO, and operational technology (OT) attacks.” The former could be used to manipulate public opinion and the latter was designed to simulate IT/OT attacks.

Security Affairs
MARCH 25, 2022
.” The two indictments, one from June 2021 and one from August 2021 , are charging one employee of the Russian Federation Central Scientific Research Institute of Chemistry and Mechanics (TsNIIKhM) and three officers of Russia’s Federal Security Service (FSB). ” continues the DoJ. ” states the DoJ.
Security Affairs
APRIL 27, 2020
” Organizations are recommended to implement supplementary security measures to protect SCADA systems used in the water and energy sectors. Government worldwide are worning of hackers targeting water utilities and urge the operators to secure industrial control systems (ICS). Pierluigi Paganini.
Security Affairs
OCTOBER 8, 2023
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

Security Affairs
AUGUST 27, 2019
The activity of the Lyceum APT group was first documents earlier of August by researchers at ICS security firm Dragos that tracked it as Hexane. Security experts at Dragos Inc. “However, the true content of this document is a training schedule spanning multiple departments, with ICS being first on the list.

Security Affairs
NOVEMBER 13, 2020
Schneider Electric released security advisories for multiple vulnerabilities impacting various products, including four issues that can be exploited by attackers to take control of Modicon M221 programmable logic controllers (PLCs). The advisory also includes General Security Recommendations for the above vulnerabilities.

Security Affairs
JULY 15, 2022
The attackers are attempting to infect industrial control systems (ICS) and create a botnet. “Dragos assesses with moderate confidence the adversary, while having the capability to disrupt industrial processes, has financial motivation and may not directly impact Operational Technology (OT) processes.” Pierluigi Paganini.
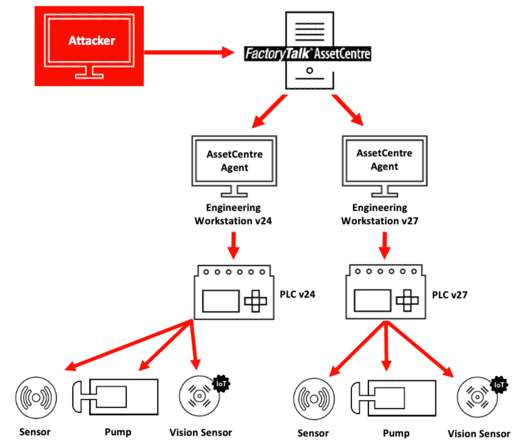
Security Affairs
APRIL 6, 2021
FactoryTalk AssetCentre provides customers with a centralized tool for securing, managing, versioning, tracking and reporting automation-related asset information across their entire facility. If you want to receive the weekly Security Affairs Newsletter for free subscribe here. ” reads the advisory published by Claroty.

Security Affairs
SEPTEMBER 30, 2021
The US Cybersecurity and Infrastructure Security Agency (CISA) has released the Insider Risk Mitigation Self-Assessment Tool , a new tool that allows organizations to assess their level of exposure to insider threats. The post CISA releases Insider Risk Mitigation Self-Assessment Tool appeared first on Security Affairs.

The Last Watchdog
OCTOBER 8, 2018
And the risks are multiplying as more digital devices become connected in insufficiently secured environments. Monitoring and management of many existing industrial control systems’ (ICS) embedded devices, like pumps, valves and turbines, are ancient in technological terms. Dismantling the silos. Expensive collateral damage.

CGI
JUNE 1, 2017
OT-IT convergence brings opportunities and risk. Operational technology (OT) or industrial control systems (ICS) are responsible for keeping the power on and water and gas flowing to support essential services for consumers, industry and governments. Thu, 06/01/2017 - 07:40. But there are huge differences in how they operate?from

CGI
JUNE 17, 2019
Cybersecurity in utilities: Critical questions for securing distributed energy resources (DERs). This is primarily because while DERs connect to electricity grid operators, they may not always be owned by these operators or support the necessary security features. Security is no longer just an IT responsibility.

Security Affairs
OCTOBER 15, 2021
In all the attacks the ransomware encrypting files on the infected systems and in one of the security incidents threat actors compromised a system used to control the SCADA industrial equipment. The SCADA system provides visibility and monitoring but is not a full industrial control system (ICS). Pierluigi Paganini.

eSecurity Planet
APRIL 19, 2023
Portnox is a private company that specializes in network access security with nearly 1,000 customers and closed a Series A fundraising with Elsewhere Partners for $22 million in 2022. To compare Portnox Cloud against competitors, see our complete list of top network access control (NAC) solutions. Who Is Portnox?
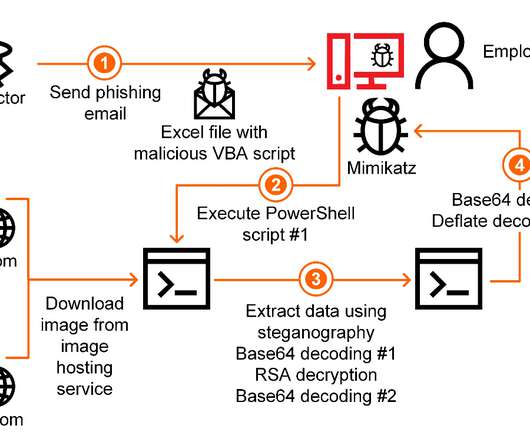
Security Affairs
MAY 29, 2020
Researchers from Kaspersky’s ICS CERT unit reported that threat actors targeted industrial suppliers in Japan and several European countries in sophisticated attacks. Kaspersky experts only observed malicious activity on IT systems, OT networks were not impacted in the attacks. ” continues the analysis. Pierluigi Paganini.

eSecurity Planet
FEBRUARY 23, 2022
How can an industrial recycler safely secure its $400,000 hard drive recertification rack with control software that only runs on Windows XP? The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. Also read: Top IoT Security Solutions for 2022.
eSecurity Planet
MAY 13, 2021
They have to supply physical security that denies access to the cyber-physical assets, and they sometimes must employ several cyber defenses depending on the device or system in question. Camera and sensor security. In short, zoning with inspection technology enabled helps to ensure IT and OT network systems’ safe operations.

CGI
JUNE 22, 2017
Securing the electricity network: Understanding the unique ICS environment of a utility. As utilities and energy delivery systems begin to seek the benefits that the convergence of information technology (IT) and operational technology (OT) offers, they also face the challenge of increased vulnerability to cyberattacks.

eSecurity Planet
APRIL 17, 2023
OPSWAT is a cybersecurity company that offers two main security product platforms: MetaDefender (threat protection) and MetaAccess (cloud access control and endpoint compliance). For all OS, the client ensures device compliance, vulnerability and patch management status, and secure access. Who Is OPSWAT?

eSecurity Planet
NOVEMBER 6, 2023
The past week has been a busy one for cybersecurity vulnerabilities, with 34 vulnerable Windows drivers and four Microsoft Exchange flaws heading a long list of security concerns. The Problem: Three flaws discovered by the Kubernetes security community carry CVSS severity scores of 7.6 CVE-2022-4886 (Path Sanitization Bypass): This 8.8-level
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content