How to Handle Retail SaaS Security on Cyber Monday the Hacker News
IG Guru
NOVEMBER 29, 2023
The post How to Handle Retail SaaS Security on Cyber Monday the Hacker News first appeared on IG GURU. Check out the article here.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

IG Guru
NOVEMBER 29, 2023
The post How to Handle Retail SaaS Security on Cyber Monday the Hacker News first appeared on IG GURU. Check out the article here.

Security Affairs
APRIL 15, 2023
The Brazilian retail arm of car manufacturing giant Volvo leaked sensitive files, putting its clientele in the vast South American country in peril. Volvo’s retailer in Brazil, Dimas Volvo, leaked sensitive files through its website. website, belonging to an independent Volvo retailer in the Santa Catarina region of Brazil.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
NOVEMBER 20, 2022
How to Secure Access for your Seasonal Workers. As the holiday season approaches, many retail, hospitality, logistics, and food manufacturing organizations hire seasonal workers to meet increasing demand. The Bureau of Labor Statistics reports a 7% job rise in the retail industry. Mon, 11/21/2022 - 05:36.

AIIM
FEBRUARY 21, 2018
Organizations must focus strategically on how to manage digital content and understand that: 1) end-users are consuming technology differently; 2) consumer devices are being increasingly used as “on-ramps” to digital workflows; and 3) how you secure the scan and capture process becomes increasingly important.

IT Governance
APRIL 3, 2019
The UK’s biggest retailers are spending more than ever on cyber security but are continuing to see an alarming rise in cyber attacks and data breaches due to the ever-evolving threat landscape, a report has found. Are retailers investing wisely? But that doesn’t reflect how hard it is to stay safe in the modern threat landscape.

IBM Big Data Hub
FEBRUARY 21, 2022
That retail has experienced extreme disruption in recent years is beyond questioning. Even before Covid turned the world on its head, headlines about the so-called “retail apocalypse” were near-ubiquitous in the media. Retail isn’t just big, it’s huge — the National Retail Federation expects sales to grow by as much as 13.5%

Thales Cloud Protection & Licensing
JANUARY 20, 2022
How to activate multifactor authentication everywhere. Workstations are often shared between several workers (in call centers, shop floor, retail stores.). Make sure the solution you choose is built for security. Offering a convenient authentication experience doesn’t have to come at the expense of security.

IT Governance
DECEMBER 5, 2023
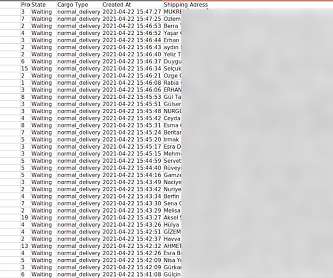
The security researcher Bob Diachenko of SecurityDiscovery first identified the exposed information in mid-September. We’ve also found 9 organisations providing a significant update on a previously disclosed incident. Organisation name Sector Location Data exfiltrated?
Thales Cloud Protection & Licensing
NOVEMBER 25, 2021
How to Protect Your Systems from Unauthorized Access This Holiday Season. Many retailers and shipping services are planning to hire temporary workers for the upcoming holiday season. That’s 50,000 more seasonal employees than the retailer brought in at the end of 2020, noted CNBC. Thu, 11/25/2021 - 05:41.

eSecurity Planet
JUNE 23, 2023
Scott Lyons, CEO of Red Lion notes, “The value of any test is less about if the pentester can get into the system and much more about if the system can prove its value to the business in resilience, ability to protect the system, or ability to provide alerts to security teams.” “The

AIIM
MARCH 29, 2022
Retailers and brands will open virtual stores, launch virtual collections, or host exclusive digital events for their targeted NFT holders. Right now, just two in five Americans say they are very or somewhat familiar with the metaverse, and less than one in five can correctly define it. will surely become insurmountable walls.

Dark Reading
APRIL 4, 2018
Retailers who haphazardly move to digital from a brick-and-mortar environment can leave their businesses open to significant cybersecurity vulnerabilities. Here's how to avoid the pitfalls.

Rocket Software
DECEMBER 22, 2021
With EDI, businesses were able to exchange documents and intellectual property (IP) across disparate systems quickly, securely and transparently. Automotive companies, general manufacturers, retailers and wholesalers, among others, are now looking to improve their EDI processes. Manage all EDI in a single place. Get expert support.

KnowBe4
DECEMBER 19, 2023
Midstride in this year’s holiday shopping, it’s important to realize just how many websites exist that impersonate legitimate online retailers. More importantly, your users need to know how to spot these types of attacks before falling victim.

IBM Big Data Hub
FEBRUARY 23, 2024
A data controller is any organization, group, or person that collects personal data and determines how it is used. Think: an online retailer that stores customers’ email addresses to send order updates. Storage limitation: Organizations should securely dispose of data as soon as its purpose is fulfilled.

Security Affairs
JANUARY 22, 2023
Every week the best security articles from Security Affairs free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! If you want to also receive for free the newsletter with the international press subscribe here. The Irish DPC fined WhatsApp €5.5M The Irish DPC fined WhatsApp €5.5M

Adam Levin
NOVEMBER 25, 2020
This presents a set of challenges for IT professionals, with 36.6% of those surveyed listing poorly secured personal and network devices as being their primary concern with a remote workforce. Follow these tips to keep your online holiday shopping secure: Avoid clicking on links in marketing emails and social media posts.

Thales Cloud Protection & Licensing
JANUARY 20, 2022
How to activate multifactor authentication everywhere. Workstations are often shared between several workers (in call centers, shop floor, retail stores.). Make sure the solution you choose is built for security. Offering a convenient authentication experience doesn’t have to come at the expense of security.

Dark Reading
NOVEMBER 19, 2018
Here's how to prevent them from wreaking holiday havoc. It's the most wonderful time of the year - and hackers are ready to pounce.

CGI
SEPTEMBER 17, 2019
The race for corporate banks to catch up with their retail peers. Corporate and transaction banks (CTBs) face the challenge of delivering services equivalent to those offered by their retail bank peers. Corporates, particularly large corporates, have not experienced the benefits of this evolution in retail banking.
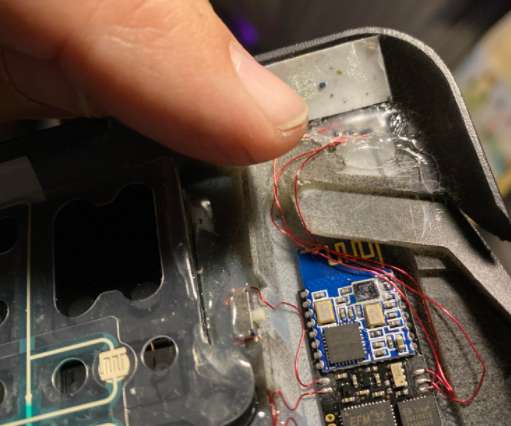
Krebs on Security
FEBRUARY 15, 2021
As a total sucker for anything skimming-related, I was interested to hear from a reader working security for a retail chain in the United States who recently found Bluetooth-enabled skimming devices placed over top of payment card terminals at several stores. Check out these other posts: How to Spot Ingenico Self-Checkout Skimmers.

CGI
DECEMBER 20, 2018
From channel to customer: How an omni-channel experience is the key to the retail industry’s success. Is the hype around the retail store being dead simply that, hype? Retailers are making a decided shift in focus from channel to customer , led by the growing demand for seamless and personalised customer experiences.
Security Affairs
APRIL 16, 2023
Every week the best security articles from Security Affairs are free for you in your email box. Every week the best security articles from Security Affairs are free for you in your email box. The post Security Affairs newsletter Round 415 by Pierluigi Paganini – International edition appeared first on Security Affairs.

WIRED Threat Level
MAY 16, 2020
The next time you sign up for a coupon code or retail promotion, use these apps to avoid spam text and email messages.

Krebs on Security
JULY 23, 2018
Google has not had any of its 85,000+ employees successfully phished on their work-related accounts since early 2017, when it began requiring all employees to use physical Security Keys in place of passwords and one-time codes, the company told KrebsOnSecurity. A YubiKey Security Key made by Yubico. a mobile device). a mobile device).

The Last Watchdog
MARCH 22, 2019
“The bad guys are insinuating their malicious code as part of the code that renders on the victim’s device during fulfillment,” says Chris Olson, CEO of the Media Trust, a McLean, VA-based website security vendor. “If For the most part, no one is really thinking about the security of all of these third-party apps. Talk more soon.

IT Governance
FEBRUARY 6, 2024
European Commission adopts cyber security certification scheme The European Commission has adopted the first European cyber security certification scheme, in line with the EU Cybersecurity Act. The voluntary scheme provides a set of rules and procedures on how to certify ICT products.

IT Governance
DECEMBER 19, 2023
An investigation determined that personal data, including names, addresses, phone numbers, Social Security numbers, dates of birth and bank account numbers, belonging to nearly 15 million people was obtained by an unauthorised party between 30 October and 1 November. Data breached: personal data belonging to 14,690,284 individuals.

Reltio
JANUARY 9, 2020
And complying with privacy and security regulations such as GDPR to protect customer data and respect customer communication preferences . It’s a business imperative that demands top-priority attention from your CEO, CMO, retail leaders, operations, customer support, and anyone else who works directly with your customers.

IT Governance
OCTOBER 26, 2021
Welcome to our third quarterly review of security incidents for 2021, in which we take a closer look at the information gathered in our monthly list of cyber attacks and data breaches. In this article, you’ll find an overview of the cyber security landscape from the past three months, including the latest statistics and our observations.

Reltio
OCTOBER 9, 2022
By processing big data, retailers can get insights into their entire supply chain. Privacy and Security. According to Capgemini , data security concerns are a major hurdle, second after budget constraints, to effectively turn big data into a profitable asset. How to Improve Big Data Management. Data governance.

eSecurity Planet
JANUARY 5, 2023
Also read: SANS Outlines Critical Infrastructure Security Steps as Russia, U.S. Given its broader availability combined with the right exploit, wiper malware could cause massive destruction in a short period of time, said Derek Manky, chief security strategist and VP of global threat intelligence at FortiGuard Labs. Trade Cyberthreats.

The Last Watchdog
MAY 3, 2021
Now comes something called attribute-based encryption, or ABE, a new approach to encrypting data that holds the potential to infuse agility into how encryption gets done online. I had the chance to learn more about ABE from Brent Waters, a distinguished scientist in the Cryptography & Information Security (CIS) Lab at NTT Research.

erwin
JUNE 11, 2020
The retail industry has also employed data intelligence in developing tools to better forecast and plan according to supply and demand trends and consumer Key Performance Indicators (KPI). Blockchain enables more secure and complex transaction record-keeping for businesses. Incorporating blockchain technology into more industries.

The Last Watchdog
APRIL 7, 2021
That’s the upshot of a new report, The State of Passwordless Security 2021 , put out by HYPR , a New York City-based supplier of advanced authentication systems. HYPR polled 427 IT professionals and found a high level of awareness about passwordless authenticators — and not just for enhanced security. Benefits beyond security.

Krebs on Security
AUGUST 16, 2018
At the time, AT&T suggested Terpin take advantage of the company’s “extra security” feature — a customer-specified six-digit PIN which is required before any account changes can be made. At the same time, so little is needed to undo weak security controls put in place to prevent abuse.

CGI
DECEMBER 20, 2018
From channel to customer: How an omni-channel experience is the key to the retail industry’s success. Is the hype around the retail store being dead simply that, hype? Retailers are making a decided shift in focus from channel to customer , led by the growing demand for seamless and personalized customer experiences.

The Last Watchdog
AUGUST 2, 2018
Claire McCaskill by Russian intelligency agency hackers, as she runs for re-election, underscores the need for each individual and organization to take online privacy and security as a core part of our everyday lives. Related: Using ‘gamification’ for security training. A large retailer may spend millions on cyber security.

Krebs on Security
OCTOBER 1, 2021
30 , the FCC said it plans to move quickly on requiring the mobile companies to adopt more secure methods of authenticating customers before redirecting their phone number to a new device or carrier. In a long-overdue notice issued Sept. ” The FCC said the proposal was in response to a flood of complaints to the agency and the U.S.
Security Affairs
JUNE 17, 2021
The securWizCase experts found a major breach that affected the popular online retailer Cosmolog Kozmetik. WizCase’s security team, led by Ata Hakç?l, l, has found a major breach in popular online retailer Cosmolog Kozmetik’s database. Hundreds of thousands of users were compromised in the breach. What’s Happening?

eSecurity Planet
SEPTEMBER 10, 2021
From the very beginning of the cloud computing era, security has been the biggest concern among enterprises considering the public cloud. In addition, 95 percent of survey respondents confirmed that they are extremely to moderately concerned about public cloud security. What is cloud security?

The Last Watchdog
MARCH 26, 2019
One way to grasp how digital transformation directly impacts the daily operations of any organization – right at this moment — is to examine the company’s application environment. Related: How new exposures being created by API sprawl. Legacy systems simply cannot address the security risks presented by APIs.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content