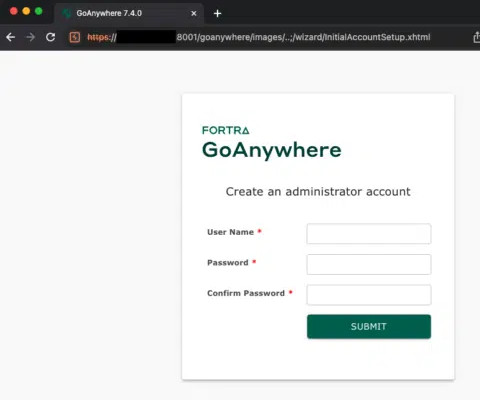
Experts released PoC exploit for Fortra GoAnywhere MFT flaw CVE-2024-0204
Security Affairs
JANUARY 24, 2024
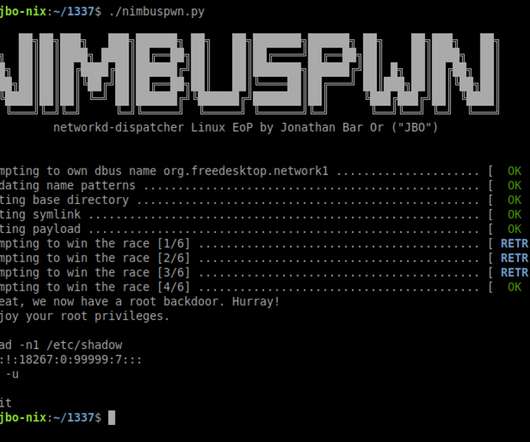
Researchers released PoC exploit code for a recently disclosed critical authentication bypass flaw in Fortra’s GoAnywhere MFT (Managed File Transfer). Researchers with cybersecurity firm Horizon3’s Attack Team published technical details of the recently disclosed vulnerability CVE-2024-0204 impacting Fortra GoAnywhere MFT.


































Let's personalize your content