The Week in Cyber Security and Data Privacy: 4 – 10 March 2024
IT Governance
MARCH 11, 2024
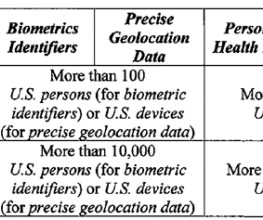
According to a listing on a popular hacking forum, the database includes customers’ names, email addresses, hashed passwords, and more. Source (New) Transport USA Yes 3,815 Okta Source 1 ; source 2 (Update) Cyber security USA Yes 3,800 Shah Dixit & Associates, P.C. The claim is yet to be verified. Data breached: 36 million records.











































Let's personalize your content