Third-Party Cyber-Risk by the Numbers
Dark Reading
APRIL 19, 2019
Recent stats show that the state of third-party cyber-risk and vendor risk management remains largely immature at most organizations.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 cyber-risk third-party-cyber-risk-by-the-numbers
cyber-risk third-party-cyber-risk-by-the-numbers 
Dark Reading
APRIL 19, 2019
Recent stats show that the state of third-party cyber-risk and vendor risk management remains largely immature at most organizations.

The Last Watchdog
JUNE 2, 2022
Third-Party Risk Management ( TPRM ) has been around since the mid-1990s – and has become something of an auditing nightmare. Related: A call to share risk assessments. This is because third-party risk has become a huge problem for enterprises in the digital age. One leading provider is Denver, Colo.-based
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JULY 13, 2023
London, July 13, 2023 — Beazley, the leading specialist insurer, today published its latest Risk & Resilience report: Spotlight on: Cyber & Technology Risks 2023. Yet, boardroom focus on cyber risk appears to be diminishing. trillion by 2025, a 300% increase since 2015 1.

The Last Watchdog
JULY 27, 2023
The number of compromised assets is not the most accurate method of evaluating an Autonomous System (AS). Though big operators inevitably receive a greater number of reports related to malicious IPs, smaller operators with fewer affiliated IPs — therefore receiving fewer reports — may be hosting riskier services.

IT Governance
DECEMBER 22, 2023
were third-party attacks). For Europe , this number rises to 61%. Admittedly, it only takes a comparatively small number of supply chain attacks to skew the number of incidents. However, that doesn’t stop the numbers from being worrying. The key here is to manage risks.

Krebs on Security
OCTOBER 1, 2020
But in practice, a fair number of victims find paying up is the fastest way to resume business as usual. Companies victimized by ransomware and firms that facilitate negotiations with ransomware extortionists could face steep fines from the U.S. Image: Shutterstock. jurisdiction) and making it a crime to transact with them.

Security Affairs
SEPTEMBER 29, 2023
Since passports contain a significant amount of personal information, including full names, date of birth, and a unique passport number, cyber criminals could use them to impersonate victims and steal their identities.” What are the risks of exposing passport data? Direct financial loss is also a possible risk.

IT Governance
NOVEMBER 23, 2023
Although the total number of data breaches – or rather, in those reported – decreased by 24% between 2019 and 2022 in the finance sector, the number of incidents increased by 99%. That really shouldn’t surprise us – these are lucrative targets for cyber criminals. What do the statistics say? million (about £4.70
Security Affairs
MARCH 10, 2024
Judge ordered NSO Group to hand over the Pegasus spyware code to WhatsApp Cybercrime BlackCat Ransomware Affiliate TTPs American Express credit cards EXPOSED in third-party vendor data breach – account numbers and names among details accessed in hack LockBit 3.0’S

Data Protection Report
NOVEMBER 2, 2023
million individuals, including dates of birth, phone numbers, partially exposed credit card details and residential addresses. In 2017, Equifax Inc, suffered a cybersecurity breach, with hackers able to access the personal data of around 13.8 The breach included data held by Equifax Inc in connection with two of Equifax’s products.

IBM Big Data Hub
FEBRUARY 6, 2024
Cybersecurity and cyber recovery are types of disaster recovery (DR) practices that focus on attempts to steal, expose, alter, disable or destroy critical data. DR itself typically targets a wider range of threats than just those that are cyber in nature. What is cyber recovery?
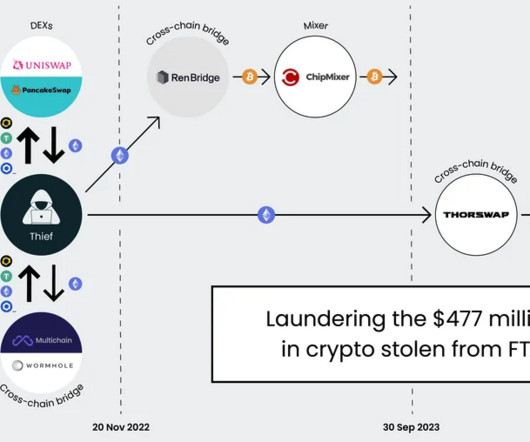
Krebs on Security
FEBRUARY 1, 2024
In a SIM-swapping attack, the crooks transfer the target’s phone number to a device they control, allowing them to intercept any text messages or phone calls sent to the victim, including one-time passcodes for authentication or password reset links sent via SMS. 11-12, 2022. ” “FTX had, it seemed, hit rock bottom.

Data Protection Report
NOVEMBER 22, 2022
The emergence of autonomous vehicles (AVs) in Canada will present a number of cybersecurity challenges and risks. AV manufacturers will need to consider these risks and address them early in the design and development process of their products. Cybersecurity Risks. Risk Mitigation. a cloud service provider).

IT Governance
MAY 17, 2022
Cyber security audits are a vital component of an organisation’s defences against data breaches and privacy violations. In this blog, we explain how cyber security audits work and show you how to conduct one. In this blog, we explain how cyber security audits work and show you how to conduct one.
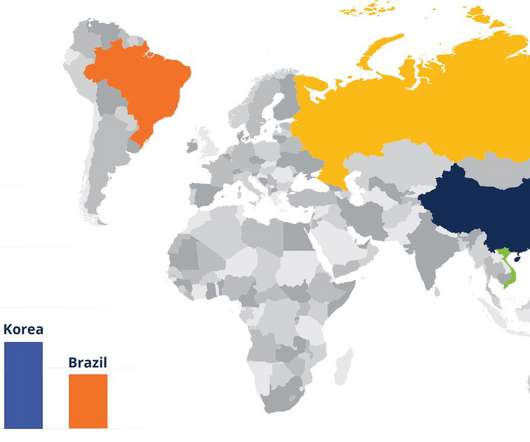
eSecurity Planet
MARCH 7, 2022
A SaaS security company says a spike in cyber attacks from Russia and China in recent weeks suggests the two countries may be coordinating their cyber efforts. “The vast volumes of data analyzed suggests these countries may even be coordinating attack efforts. Security Agencies Release Network Security, Vulnerability Guidance ).
IT Governance
DECEMBER 5, 2023
The number of incidents is particularly high this month, partly because we’ve improved our incident-finding processes, but also partly because we’ve seen several big supply chain attacks this month. In these cases, a service provider suffered a cyber attack, which had a knock-on effect on numerous other organisations.

eSecurity Planet
APRIL 22, 2022
That’s where cyber insurance may be able to help. As the number and severity of data breaches continues to rise, organizations are recognizing that those costs are not theoretical. However, a good cyber insurance provider can also leverage their partnerships to help your company afford better security controls. That’s a 29.1%

eSecurity Planet
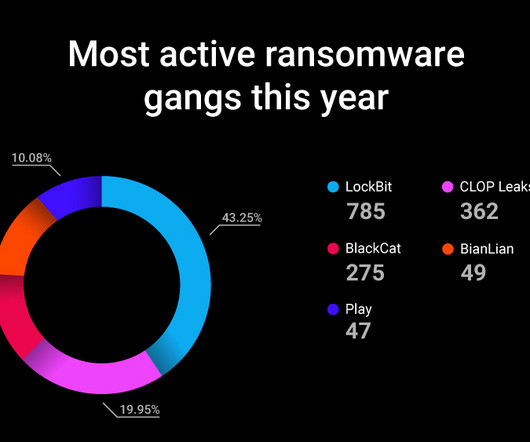
MAY 27, 2021
The explosion of ransomware and similar cyber incidents along with rising associated costs is convincing a growing number of insurance companies to raise the premiums on their cyber insurance policies or reduce coverage, moves that could further squeeze organizations under siege from hackers. Insurers Assessing Risks.

The Last Watchdog
DECEMBER 5, 2018
million patients had significant amounts of PII exposed by the healthcare provider’s third-party billing vendor, AccuDoc Solutions, shows the healthcare sector remains acutely vulnerable to attacks exploiting third-party contractors even as their first-party security posture hardens. Weak links. Sticky problem.
eSecurity Planet
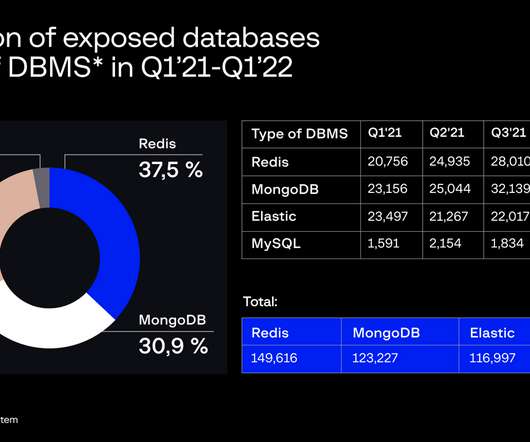
MAY 3, 2022
The Attack Surface Management team at Group-IB said it constantly scans the IPv4 landscape for exposed databases, potentially unwanted programs, and other risks. The Attack Surface Management team at Group-IB said it constantly scans the IPv4 landscape for exposed databases, potentially unwanted programs, and other risks.

IT Governance
JANUARY 19, 2023
Customers’ full names, phone numbers and mailing addresses are thought to have been exposed in the incident. However, it’s unclear what damage the cyber criminals were able to inflict before the vulnerability was closed. Are customers at risk? How did this happen? Our own systems were not compromised.

The Last Watchdog
FEBRUARY 3, 2020
Department of Homeland Security issued a bulletin calling out Iran’s “robust cyber program,” and cautioning everyone to be prepared for Iran to “conduct operations in the United States.” ” Related: Cyber warfare enters Golden Age In fact, strategic cyber operations essentially pitting Russia and Iran against the U.S.
IT Governance
APRIL 3, 2023
Welcome to our March 2023 list of data breaches and cyber attacks. You can find the full list of data breaches and cyber attacks below, including our new feature in which we delve into the month’s biggest incidents in a little more detail. This suggests that it had a poor understanding of the attack and rushed to disclose the breach.

Hunton Privacy
NOVEMBER 15, 2023
In February 2022, Medlab became aware of unauthorized third-party access to its IT system, and undertook a forensic investigation led by independent external cyber experts. However, the maximum penalty available in this case will be A$2.2 million because the company’s conduct occurred prior to December 2022.

IT Governance
NOVEMBER 6, 2023
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. Welcome to this week’s round-up of the biggest and most interesting news stories. Library branches remain open, Wi-Fi is still available and materials can still be borrowed.

The Last Watchdog
APRIL 30, 2019
If your company is participating in the global supply chain, either as a first-party purchaser of goods and services from other organizations, or as a third-party supplier, sooner or later you’ll encounter the NIST Cybersecurity Framework. and the upcoming NIST Privacy Framework. and the upcoming NIST Privacy Framework.

IBM Big Data Hub
JANUARY 19, 2024
A disaster recovery strategy lays out how your businesses will respond to a number of unplanned incidents. Typically, companies either build DRPs themselves or outsource their disaster recovery process to a third-party DRP vendor. Worldwide, the popularity of disaster recovery strategies is understandably increasing.

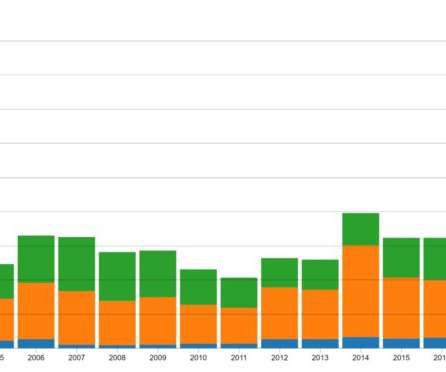
IT Governance
JANUARY 20, 2022
Welcome to our review of security incidents for 2021, in which we take a closer look at the information gathered in our monthly list of data breaches and cyber attacks. By contrast, there was a significant decrease in the number of breached records over the same period (20.1 Our findings support this theory.

Security Affairs
DECEMBER 1, 2022
Eliminating the risk of a data breach is nearly impossible, but some things can be done to reduce it significantly. Yahoo initially reported that 1 billion users had been affected, but the number turned out to be much higher. Data breaches can be devastating for organizations and even entire countries. SolarWinds attack on U.S.
Krebs on Security
DECEMBER 14, 2022
The services are generally priced according to the volume of traffic to be hurled at the target, the duration of each attack, and the number of concurrent attacks allowed. The DOJ also charged six U.S. men with computer crimes related to their alleged ownership of the popular DDoS-for-hire services. The DOJ also charged six U.S.

IT Governance
JULY 8, 2020
Doing so means they get a step ahead of their competitors, but it comes at the cost of reviewing and addressing cyber security risks. Effective cyber security begins with a solid internal understanding of risks and the processes designed to mitigate them. Likewise, senior management should adopt cyber resilience.

Data Matters
FEBRUARY 28, 2019
The review aimed to look more closely at how wholesale banking and asset management firms oversee and manage their cybersecurity, including the extent to which firms identify and mitigate relevant cyber risks and their current capability to respond to and recover from data security incidents.

IT Governance
JANUARY 21, 2021
The Wentworth Club, whose members include high-profile celebrities, emailed those affected offering its “profuse apologies” after its systems were crippled by cyber criminals. Cyber security experts urge organisations not to pay up, because there is no assurance that the attackers will keep their word. Paying the ransom.
Security Affairs
OCTOBER 17, 2023
Studies show that human error is the root cause of more than 80% of all cyber breaches, whether malicious or unintended. This is happening despite an exponential increase in organizational cyber training over the past decade. Not to mention the heightened cyber awareness and risk mitigation across businesses and industries.

The Last Watchdog
MARCH 29, 2022
based networking systems supplier, like any number of other established tech giants, as well as innumerable cybersecurity startups, is deeply vested in seeing this transition through to the end. Log4j is the latest, greatest vulnerability to demonstrate just how tenuous the security of modern networks has become. The Sunnyvale, Calif.-based

IT Governance
FEBRUARY 14, 2023
The goal is to prevent unauthorised personnel from accessing the data – whether that’s cyber criminals or employees who don’t have a legitimate reason to access the files. The third element of the CIA triad is availability. Confidentiality, integrity and availability. The second element of the CIA triad is integrity.

IT Governance
JUNE 15, 2023
The UK’s broadcasting regulator, Ofcom, has revealed that it’s among the organisations whose data has been stolen in the massive MOVEit cyber attack. This is the latest in a series of cyber attacks exploiting a critical flaw in Progress Software’s MOVEit file transfer tool, which is used by thousands of organisations and as many as 3.5
IT Governance
APRIL 5, 2023
Malware is one of the most common cyber security threats that organisations and individuals face. It can do this in a number of ways, such as: Stealing, encrypting or deleting sensitive information; Hijacking or altering core system functions; Monitoring user activity; and Spamming the device with adverts. What is malware?

Security Affairs
JUNE 16, 2023
We are aware of a cyber security incident that has impacted a third-party tool from Progress called MOVEit Transfer, which is used by a small number of Shell employees and customers,” said Shell US spokesperson Anna Arata in a statement. “Our At this time the number of installs located in the UK is 127.
eSecurity Planet
JANUARY 6, 2022
Third-party security, ransomware , artificial intelligence (AI) and decentralized finance (DeFi) are some of the threats you can expect to see more of this year – with the potential for far worse results than we’ve seen in the past. Third-party Risks Take Center Stage.

eSecurity Planet
OCTOBER 21, 2022
Effective patch management mitigates risk by eliminating domain-specific activities and applying standard processes across all enterprise systems,” said Gartner analyst Terrence Cosgrove. Risk Assessment: Include a risk assessment for your own organization that isolates the key systems and applications to patch first.

Data Protection Report
SEPTEMBER 21, 2021
OFAC’s revised guidance regarding the risks of ransomware payments does not substantially modify OFAC’s earlier October 1, 2020 guidance on the same topic (available here ) in which OFAC highlighted: (i) the U.S. OFAC’s measures consist of: (1) the designation of the entire SUEX OTC, S.R.O.

Thales Cloud Protection & Licensing
MARCH 1, 2023
Europe Leads the Cybersecurity Regulation Dance divya Thu, 03/02/2023 - 06:58 Europe has emerged as a hub for developing cyber policies, acting to improve software security, and quickly reporting severe breaches. It includes a 24-hour deadline for such organizations to disclose major cyber incidents as soon as they become aware.

Security Affairs
FEBRUARY 14, 2020
Nedbank bank announced on Thursday that a security breach at a third-party supplier has compromised the details of as many as 1.7 Nedbank bank disclosed on Thursday a security breach at a third-party supplier that has compromised the details of as many as 1.7 million of its clients. million of its clients.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content