Cloud-Native Businesses Struggle with Security
Dark Reading
MAY 6, 2021
More companies moved to cloud-native infrastructure in the past year, and security incidents and malware moved right along with them.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 cloud-security cloud-native-businesses-struggle-with-security
cloud-security cloud-native-businesses-struggle-with-security 
Dark Reading
MAY 6, 2021
More companies moved to cloud-native infrastructure in the past year, and security incidents and malware moved right along with them.

The Last Watchdog
OCTOBER 23, 2023
Cisco’s $28 billion acquisition of Splunk comes at an inflection point of security teams beginning to adopt to working with modern, cloud-native data lakes. Related: Dasera launches new Snowflake platform For years, Splunk has been the workhorse SIEM for many enterprise Security Operation Centers (SOCs).
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IBM Big Data Hub
NOVEMBER 14, 2023
This integration is crucial for modernizing core enterprise applications on hybrid cloud platforms. Moreover, 36% of developers struggle with the collaboration between development and IT Operations, leading to inefficiencies in the development pipeline. What are the benefits of Wazi as a service on IBM Cloud?

Adapture
APRIL 4, 2024
For industries in which regulatory compliance is a condition of doing business—like finance and healthcare—maintaining it is absolutely crucial. Challenges of Maintaining Compliance Growing Environments Growing environments can cause IT departments to struggle to maintain compliance.
IBM Big Data Hub
MAY 19, 2023
Web-based ERP providers are experiencing significant growth and demand as more companies seek to streamline their business processes, cut costs and improve operational efficiency. The rapid growth of global web-based ERP solution providers The global cloud ERP market is expected to grow at a CAGR of 15%, from USD 64.7 billion by 2027.

IBM Big Data Hub
DECEMBER 19, 2023
For many enterprises, the journey to cloud reduces technical debt costs and meets CapEx-to-OpEx objectives. Many enterprises struggle to derive real value from their cloud journeys and may continue to overspend. Patterns that address security and compliance dimensions, ensuring traceability to these requirements.
Thales Cloud Protection & Licensing
OCTOBER 17, 2023
Three Easy Ways to Improve DevSecOps with Thales and Red Hat divya Tue, 10/17/2023 - 14:47 For many DevOps enthusiasts, the need to insert security considerations directly into the development cycle was often overlooked. Securing this data at rest is vitally important since it is otherwise vulnerable to breaches or unauthorized access.

The Last Watchdog
JUNE 23, 2021
The challenge of embracing digital transformation while also quelling the accompanying cyber risks has never been greater for small- and mid-sized businesses. To boost productivity, they must leverage cloud infrastructure and participate in agile software development. Related: How ‘PAM’ improves authentication.

IBM Big Data Hub
SEPTEMBER 21, 2023
But as organizations race to adopt these new technologies for business, it requires a global ecosystem of partners with industry expertise to identify the right enterprise use-cases for AI and the technical skills to implement the technology. Generative AI and large language models are poised to impact how we all access and use information.

IBM Big Data Hub
AUGUST 16, 2023
Cloud computing can add a collective $3 trillion to organizations that harness it correctly, according to McKinsey. It is poised to transform businesses and industries, revolutionize how employees and other stakeholders collaborate, and drive digital transformation initiatives.

eSecurity Planet
DECEMBER 7, 2022
Just today, security and compliance automation firm Drata announced a $200 million Series C funding round that brings the company’s valuation to $2 billion, doubling its $1 billion valuation from its Series B round last year. According to a recent Gartner survey, security is the top priority for CIOs. Where will the dollars go?

IBM Big Data Hub
JUNE 23, 2023
Insurers are also struggling with high, mostly fixed costs and the complexities of maintaining legacy systems, which makes current variable cost-based alternatives more attractive. Business scalability: The ability to allocate and release resources based on demand and gain savings from economies of scale.

IBM Big Data Hub
JULY 17, 2023
How generative AI is disrupting customer service Generative AI represents a powerful opportunity for businesses to increase productivity, improve personalized support and encourage growth. They also expect service to be delivered 24/7 across multiple channels. Watsonx.ai

Rocket Software
SEPTEMBER 27, 2021
For years, businesses that use mainframe technology have been seeing their seasoned professionals retire. Now, companies are struggling to find new talent to fill this skills vacuum, and when they do, it is difficult to properly train them without those established experts to offer guidance. Don’t Limit the Candidate Pool .

Collibra
JANUARY 31, 2020
To celebrate Data Privacy Day, we asked Collibrians across the globe to shed some light on what it’s like to support and defend privacy, regulation and security, as part of the Data Intelligence Company. What advice do you have for organizations that are struggling with balancing compliance and innovation? . “In

eSecurity Planet
AUGUST 10, 2023
Cloud security posture management (CSPM) discovers and manages infrastructure and configuration risks across cloud environments. As most cloud security failures are due to customer error, CSPM’s ability to find and fix those errors has made it a critical cloud security tool.

eSecurity Planet
DECEMBER 19, 2023
Attack surfaces will explode: Cyberdefense complexity will compound as API, cloud, edge, and OT resources add to the list of assets to defend. For more on governance and policies, check out our article on IT security policies , including their importance and benefits, plus tips to create or improve your own policy.

CGI
FEBRUARY 26, 2015
What happens when yesterday's digital natives are tomorrow's leaders? A lot has been written about the expectations of digital natives coming into the workplace and how difficult it can be for digital natives and digital immigrants to communicate. Understanding this change is critical for businesses to plan.

The Last Watchdog
AUGUST 2, 2023
2, 2023 – Normalyze , a pioneer in cloud data security, today introduced new capabilities to protect data across hybrid cloud deployments and on-premises environments. Organizations with sophisticated hybrid cloud frameworks struggle to get an end-to-end picture of the risks across all data stores.

IBM Big Data Hub
OCTOBER 17, 2023
Introducing the SAP Business Technology Platform The SAP Business Technology Platform (BTP) is a technological innovation platform designed for SAP applications to combine data and analytics, AI, application development, automation and integration into a single, cohesive ecosystem.

eSecurity Planet
FEBRUARY 23, 2024
An application gateway, also known as an application level gateway (ALG), functions as a critical firewall proxy for network security. Its filtering capability ensures that only certain network application data is transmitted, which has an impact on the security of protocols including FTP, Telnet, RTSP, and BitTorrent.

Thales Cloud Protection & Licensing
FEBRUARY 17, 2020
In the past decade, businesses started evaluating the pros and cons of moving to the cloud in order to meet the increased demand for the cost and IT efficiency benefits of cloud computing and Software as a Service (SaaS). This presents a security risk to businesses. Just Good Enough Security is Not Good Enough.
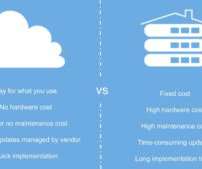
Reltio
JUNE 22, 2020
Cloud-native is a phrase tossed around a lot these days. Why is the cloud-native model gaining popularity? While architecture and technology provide operational flexibility, the business benefits of cloud-native models are more wide-ranging. Advantages of Cloud vs On-Prem. Cloud-hosted.

eSecurity Planet
OCTOBER 26, 2023
Multi-cloud is a cloud computing strategy that enables businesses to run their applications and services across multiple private and public cloud platforms, so securing multi-cloud environments is a complicated task. Here is a step-by-step approach for making multi-cloud security work.

Thales Cloud Protection & Licensing
FEBRUARY 1, 2024
They struggled to create and remember complex, ever-changing passwords for the maze of systems they accessed daily. They're error-prone, an unstable link in the security chain, a high-friction element in user journeys, and an outdated authentication method unsuitable for today's landscape. Fortunately, it didn’t have to.
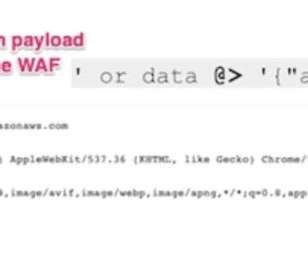
eSecurity Planet
DECEMBER 12, 2022
“An attacker able to bypass the traffic scanning and blocking capabilities of WAFs often has a direct line to sensitive business and customer information,” vulnerability researcher Noam Moshe wrote in a blog post detailing the threat. Read next: Top Database Security Solutions. “This turned out to be JSON.”

eSecurity Planet
OCTOBER 20, 2021
Businesses have far more cloud security options than they once did, making clouds often as safe as, if not safer than, on-premises solutions. Still, cloud security has grown increasingly complicated as application development and deployment have grown. A recent survey found that 79% of U.S.

Thales Cloud Protection & Licensing
AUGUST 2, 2023
Cloud Key Management Solution for Azure, Azure Stack and M365 madhav Thu, 08/03/2023 - 05:59 Uncover Your Cybersecurity Blind Spots Cybersecurity is a strategic risk that should be managed at the highest levels of an organization. CCKM reduces your operational burden and increases efficiency.

eSecurity Planet
NOVEMBER 4, 2022
The two are addressing major issues like sprawling cloud and software supply chain risks, showing that good companies addressing real needs are having little trouble finding investors. Versa Networks is a top operator in the fast-growing Secure Access Service Edge (SASE) market. See the Top Secure Access Service Edge (SASE) Providers.

IBM Big Data Hub
APRIL 19, 2023
In response to the COVID-19 crisis, many federal agencies kicked their digital transformations into high gear to help enhance public services, embrace a remote workforce and better secure data with trust and transparency. IBM has built a diverse ecosystem of partners to help government effectively use the cloud to address these challenges.

Reltio
JANUARY 28, 2021
MDM technology has advanced leaps and bounds in the last five to 10 years to keep up with business trends and digital transformation. The best practices many businesses centered their ERPs and customer data systems on now severely limit their agility and ability to use emerging data sources for competitive advantage. Examples: .

IBM Big Data Hub
APRIL 19, 2023
In response to the COVID-19 crisis, many federal agencies kicked their digital transformations into high gear to help enhance public services, embrace a remote workforce and better secure data with trust and transparency. IBM has built a diverse ecosystem of partners to help government effectively use the cloud to address these challenges.

ARMA International
SEPTEMBER 27, 2021
Part 1 discussed the key DT business drivers, concepts, and technology trends, how they are transforming organizations and society, and how they are affecting business users and customers. This means imagining the “art of the possible” for a new future using a cloud computer model to deliver transformative change.

eSecurity Planet
SEPTEMBER 17, 2021
Remote work poses unique risks not addressed by traditional corporate network security , so it’s only natural that enterprise security vendors have been targeting work-at-home employees with more advanced security solutions than you’d typically see in a home office. Fortinet and Linksys HomeWRK Solution.

Reltio
JANUARY 28, 2021
Data is your business’s most important asset in a digitized world. It drives decision-making at every level of business. Real-time data-driven decisions give your business the agility to adjust to market fluctuations, consumer preferences, and access to capital. MDM Best Practices for Business Success. #1

Reltio
JUNE 22, 2020
Retail & Luxury Brand Business Needs Mapped to Customer Data Challenges. It maps retail and luxury brand business needs to their related customer data challenges. They believe in using customer data strategically. They are working together to bridge their customer data silos to create a company-wide customer data strategy.

eSecurity Planet
MAY 2, 2024
Attackers can compromise credentials because of extensive user password problems throughout most organizations; however, a number of security solutions provide credentials protection for both basic and advanced needs. 20% increase accesses of specific organizations advertised. 583% increase in Kerberoasting [password hash cracking] attacks.

Reltio
NOVEMBER 9, 2020
Business and IT leaders are working collaboratively to design and deliver omnichannel connected customer experiences. Organizations use customer data in virtually every function of the business, including customer experience, product research, design, development, advertising, marketing, and sales. It's a company-wide transformation.

eSecurity Planet
FEBRUARY 9, 2024
Cloud-native application development combines organizational and technical changes in the design, build, and deployment of software in the cloud to deliver value faster and improve overall business efficiency. Gartner predicts that by 2025, more than 95% of new digital workloads will be deployed on cloud-native platforms.

IBM Big Data Hub
AUGUST 3, 2023
In a recent trend, many organizations are opting to store their sensitive data in the cloud. In essence, data democratization occurs when everyone within an organization has access to sensitive and business-valuable data. It’s both a data security and privacy issue. What is data democratization?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content