ISACA Security Survey 2023: Technical Skills Gaps, Budgeting
Data Breach Today
OCTOBER 6, 2023
ISACA's Jon Brandt Discusses Threat Trends, Hiring Challenges, New Opportunities What kinds of training do security professionals need?
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
OCTOBER 6, 2023
ISACA's Jon Brandt Discusses Threat Trends, Hiring Challenges, New Opportunities What kinds of training do security professionals need?

Thales Cloud Protection & Licensing
MARCH 24, 2024
Data Security Trends: 2024 Report Analysis madhav Mon, 03/25/2024 - 05:08 Amid ongoing economic uncertainty and a progressively complex threat landscape, businesses are trying to navigate increasingly stringent regulatory requirements while bolstering their security posture. Next came Post Quantum Cryptography with 45%.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Micro Focus
DECEMBER 7, 2022
The post New Market Survey Reveals 5 Key Digital Transformation Trends appeared first on Micro Focus Blog. IT organizations are on a continuous path for digital transformation. Much as they’ve made huge recent leaps in their digital growth, there is. View Article.

Data Breach Today
NOVEMBER 6, 2023
ISC2 CEO Clar Rosso on the Latest Cybersecurity Training and Development Trends Tech firms are making huge investments in generative AI tools, but nearly half of cybersecurity professionals say they have little or no or knowledge of AI, according to ISC2's Cyber Workforce Study 2023, which surveyed 14,865 international security practitioners and decision-makers. (..)

Advertisement
Think your customers will pay more for data visualizations in your application? Five years ago they may have. But today, dashboards and visualizations have become table stakes. Discover which features will differentiate your application and maximize the ROI of your embedded analytics. Brought to you by Logi Analytics.

OpenText Information Management
JUNE 21, 2023
Simple and effective security … The post OpenText Cybersecurity 2023 Global Managed Security Survey: Tool Consolidation is More Than a Trend, it’s a Demand appeared first on OpenText Blogs. With more than 700,000 unfilled cybersecurity positions in the U.S.

IT Governance
MARCH 20, 2024
In the UK, cyber security has been dropping down the board’s list of priorities. The UK government’s Cyber Security Breaches Survey 2023 confirms this trend. Fewer directors, trustees and other senior managers of both UK businesses and charities see cyber security as a high priority in 2023 compared to 2022.
The Security Ledger
MAY 10, 2023
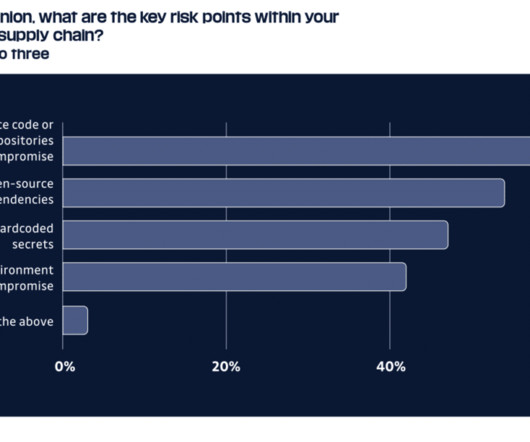
A bunch of recent surveys of IT and security pros send a clear message: threats and risks from vulnerable software supply chains are real, and they’re starting to freak people out. The post The surveys speak: supply chain threats are freaking people out appeared first on The Security Ledger with Paul F.

IBM Big Data Hub
JANUARY 15, 2024
While digital transformation has been a trend for some years, emerging technologies have made this movement even more important. They face an ever-increasing cadre of startups and established organizations, all of whom are also trying to keep up to date on digital transformation trends to achieve a competitive edge.

DLA Piper Privacy Matters
MAY 5, 2021
The Department for Culture Media and Sport recently published its annual Cyber Security Breaches Survey (the “Survey” ), which aims to capture trends in cyber security incidents and provides a snapshot of the approach of UK businesses to the risks of an incident and the types of incidents seen in the previous 12 months.

Dark Reading
FEBRUARY 15, 2023
Factoring user experience and convenience into how employees and tenants access buildings is top concern for security professionals says benchmark industry survey.

eDiscovery Daily
JULY 2, 2019
As part of its focus on offerings and opportunities that impact certifications, careers, contacts, and competence, the Association of Certified E-Discovery Specialists (ACEDS) recently conducted one of the more comprehensive online surveys of individuals currently working in the field of the eDiscovery that I’ve seen in a long time.

DLA Piper Privacy Matters
JANUARY 19, 2021
The third annual DLA Piper GDPR fines and data breach survey which we launched today reflects how the current circumstances have affected the privacy landscape across the 31 European countries surveyed. ” This year’s report also considers emerging trends and enforcement priorities.

The Last Watchdog
MARCH 18, 2020
Related: Why some CEOs have quit tweeting That’s the upshot of FireMon’s second annual State of Hybrid Cloud Security Report of 522 IT and security professionals, some 14 percent of whom occupy C-suite positions. This is the fact that the cloud services provider is only liable for securing the underlying cloud infrastructure.

The Last Watchdog
OCTOBER 4, 2023
In a keynote address, Omdia’s Eric Parizo, managing prinicipal analyst, and Andrew Braunberg, principal analyst, unveiled an approach they coined as “proactive security.” Last Watchdog followed up with Braunberg to ask him, among other things, what RBVM solutions signal about the ramping up of proactive security.

The Last Watchdog
MARCH 4, 2024
These worrying statistics underscore the need to be more proactive in preventing security breaches. Keeping these systems up to date and installing the latest security patches can help minimize the frequency and severity of data breaches among organizations. A robust security plan is only as good as its weakest link.

KnowBe4
SEPTEMBER 22, 2022
A survey by GetApp has found that the number of organizations using phishing simulations has risen from 30% in 2019 to 70% in 2022. Despite this positive trend, however, attackers continue to increase both the sophistication and volume of their phishing emails, which has led to a significant rise in employees clicking on phishing links.
Security Affairs
JANUARY 25, 2020
Chinese hackers have exploited a zero-day vulnerability the Trend Micro OfficeScan antivirus in the recently disclosed hack of Mitsubishi Electric. According to ZDNet, the hackers involved in the attack against the Mitsubishi Electric have exploited a zero-day vulnerability in Trend Micro OfficeScan to infect company servers.

Schneier on Security
JULY 28, 2020
Key trends from their summary : Deep Impact from State Actors: There were at least 27 different state attacks against the software supply chain including from Russia, China, North Korea, and Iran as well as India, Egypt, the United States, and Vietnam.States have targeted software supply chains with great effect as the majority of cases surveyed here (..)

Threatpost
JUNE 28, 2021
A survey from GSMA and Trend Micro shows a concerning lack of security capabilities for private 5G networks (think factories, smart cities, industrial IoT, utilities and more).

Thales Cloud Protection & Licensing
MARCH 23, 2022
Shifting Risk and Business Environment Demand creates a Shift in Security Strategies. The 2022 Thales Data Threat Report, based on data from a survey of almost 2,800 respondents from 17 countries across the globe, illustrates these trends and changes. Malware and accidental human error are the biggest security threats.

eDiscovery Daily
JULY 22, 2019
I’m here to cover the results of the Summer 2019 eDiscovery Business Confidence Survey, published (as always) on Rob Robinson’s terrific Complex Discovery site. As always, Rob provides a complete breakdown of the latest survey results, which you can check out here. of all respondents. point rebound to 50.9% of respondents.
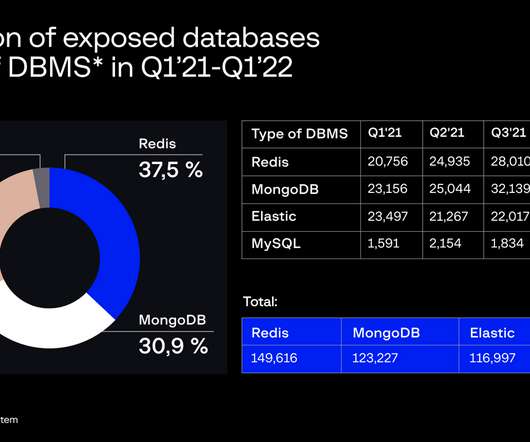
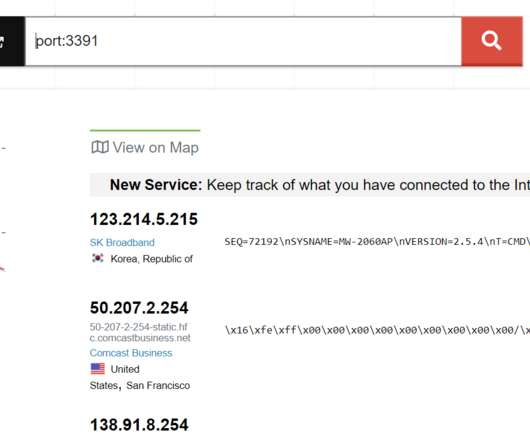
eSecurity Planet
MAY 3, 2022
Also read: Database Security: 7 Best Practices & Tips. According to Group-IB, the likelihood of the database systems being used in cybercrime and security breaches is high. days was required for an exposed database owner to resolve a security issue in the first quarter of 2021. Expectations for Security Breaches Run High .

eSecurity Planet
OCTOBER 18, 2022
The vast majority of cybersecurity decision makers – 91 percent, in fact – find it difficult to select security products due to unclear marketing, according to the results of a survey of 800 cybersecurity and IT decision makers released today by email security company Egress. Assessing AI and Security Training.

eSecurity Planet
JANUARY 18, 2024
When assessing the overall security of cloud storage and choosing a solution tailored to your business, it helps to determine its features, potential risks, security measures, and other considerations. It excels in remote access, scalability, and security, with distributed storage options and privacy adherence capabilities.

The Last Watchdog
AUGUST 1, 2023
1, 2023– AppViewX , a leader in automated machine identity management (MIM) and application infrastructure security, today announced the results of a research study conducted by Enterprise Management Associates (EMA) on SSL/TLS Certificate Security. New York, NY, Aug.

The Last Watchdog
SEPTEMBER 21, 2022
Over the past two years, this trend has greatly accelerated, and working practices have been transformed for many workers and organizations. Yet, with all these changes, the specter of security breaches remains high. Meanwhile, there has also been a shift to a Zero Trust security approach. Strategy reassessment needed.

The Last Watchdog
MAY 18, 2021
To make matters more difficult, implementing new security software and processes to address these issues is another big hurdle, often causing disruption—and not the good kind. So, how can businesses strike the balance between proper security measures and a modernized IT infrastructure with the headaches of migrating systems?
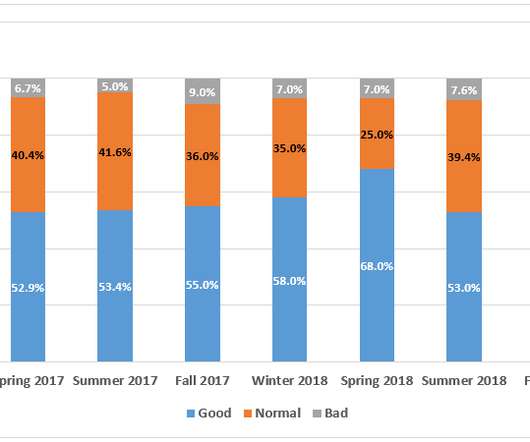
eDiscovery Daily
JANUARY 14, 2020
I’m here to cover the results of the Winter 2020 eDiscovery Business Confidence Survey, published (as always) on Rob Robinson’s terrific Complex Discovery site. As always, Rob provides a complete breakdown of the latest survey results, which you can check out here. of total respondents, the least diverse survey since Fall 2018.

IBM Big Data Hub
JUNE 9, 2023
.” API management and API gateways can play an important role in how you consistently create, secure and control access to your APIs. Introducing Noname Advanced API Security for IBM Against this backdrop, IBM has collaborated with Noname Security to help companies shore up their API lifecycle against malicious activity.

Thales Cloud Protection & Licensing
JANUARY 24, 2022
Data Privacy and Security: It Takes Two to Tango. The goal of Data Privacy Week, celebrated between January 24 – 28, is to spread awareness about online privacy and educate citizens on how to manage their personal information and keep it secure. However, with technology innovation comes new risks, security challenges and threats.

eDiscovery Daily
OCTOBER 23, 2019
I’m here to cover the results of the Fall 2019 eDiscovery Business Confidence Survey, published (as always) on Rob Robinson’s terrific Complex Discovery site. As always, Rob provides a complete breakdown of the latest survey results, which you can check out here. of respondents, which is the lowest ever for a Fall survey.

Thales Cloud Protection & Licensing
FEBRUARY 4, 2020
The traditional focus on security has been on breach prevention and threat detection but these can only go so far. For organisations going through digital transformation there needs to be a layered approach to security – complimenting these traditional strategies with data protection.In contracts). We’d love to hear from you.

AIIM
MARCH 30, 2023
The information management industry is also undergoing pivotal change due to AI, increasing information chaos, emerging workplace trends , and changing demographics. Emerging Workplace Trends. Remote work and hybrid work have fundamentally changed information security and governance. Changing Demographics.

eSecurity Planet
AUGUST 8, 2022
Security executives have been adding features focusing on zero-trust technology , automation, responsive SOAR platforms , secure access service edge (SASE) models, and deception technology , among others. The Key to Cyber Defense is Security Culture. We break security culture into seven distinct, measurable dimensions.

Schneier on Security
OCTOBER 3, 2019
In August, CyberITL completed a large-scale survey of software security practices in the IoT environment, by looking at the compiled software. This dataset contains products such as home routers, enterprise equipment, smart cameras, security devices, and more. CyberITL's methodology is not source code analysis.

eDiscovery Daily
OCTOBER 31, 2018
The Complex Discovery eDiscovery Business Confidence Survey is in the last quarter of its third year and the results are in for the Fall 2018 eDiscovery Business Confidence Survey! As always, Rob provides a complete breakdown of the latest survey results, which you can check out here. of all respondents. Last Fall, it was 5.5%

eDiscovery Daily
FEBRUARY 19, 2018
A recently issued report provides an interesting look at how Chief Information Security Officers (CISOs) and others responsible for security are addressing the challenges in today’s cybersecurity climate. 77 percent of respondents advised that the scope of their managed security services includes incident response.

The Security Ledger
OCTOBER 21, 2021
Brian Trzupek of DigiCert joins Paul to talk about the findings of a recent State of PKI Automation survey and the challenges of managing fast-growing population of tens of thousands of PKI certificates. The post Spotlight: Automation Beckons as DevOps, IoT Drive PKI Explosion appeared first on The Security Ledger with Paul F.

eDiscovery Daily
JANUARY 13, 2019
Hard to believe that we’ve started the fourth year of the Complex Discovery eDiscovery Business Confidence Survey! As always, Rob provides a complete breakdown of the latest survey results, which you can check out here. So, this time, I will look at the results for all thirteen surveys to date. individual responses.
Thales Cloud Protection & Licensing
APRIL 12, 2022
Identity Management Day 2022: Identity Security Is Our Responsibility. As the lines between our personal and professional lives continue to blur, protecting our digital identities as consumers, employees, or partners is essential to security. This is a great step towards adopting a Zero Trust approach to security.

eDiscovery Daily
APRIL 25, 2019
As promised yesterday , I’m here to cover the results of the Spring 2019 eDiscovery Business Confidence Survey, published (as always) on Rob Robinson’s terrific Complex Discovery site. As always, Rob provides a complete breakdown of the latest survey results, which you can check out here. and continued until registration of 180(!)

The Last Watchdog
NOVEMBER 28, 2023
The study, conducted by independent research firm Propeller Insights, dives into how IT business leaders feel about their security posture in a world where the technologies they embrace to grow and thrive are also vulnerable to constant and increasing threats. Human error is among the top causes of security breaches.

The Last Watchdog
MAY 8, 2023
Moreover, of the current worldwide workforce, surveys conducted by PwC have shown that there is only a 38 percent ‘availability of key skills ’, considering the new and more sophisticated emerging threats developed by malicious actors. According to Cybersecurity Ventures, by 2025 there will exist a gap of over 3.5
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content