ISC2 Cyber Workforce Study Says AI, Cloud Skills Are Needed
Data Breach Today
NOVEMBER 6, 2023
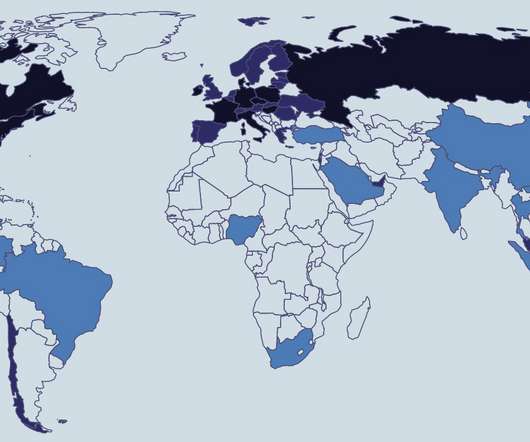
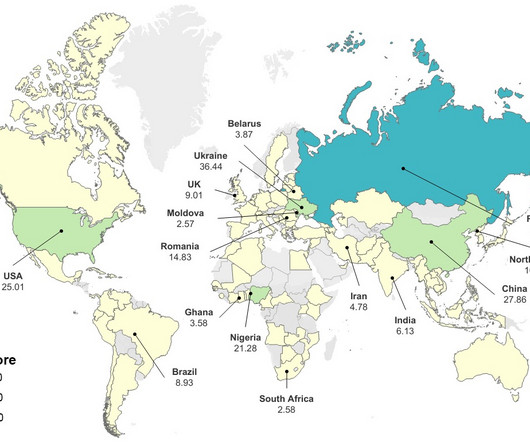
ISC2 CEO Clar Rosso on the Latest Cybersecurity Training and Development Trends Tech firms are making huge investments in generative AI tools, but nearly half of cybersecurity professionals say they have little or no or knowledge of AI, according to ISC2's Cyber Workforce Study 2023, which surveyed 14,865 international security practitioners and decision-makers. (..)













































Let's personalize your content