Australia Unveils AU$587M Strategy to Defeat Cybercrime
Data Breach Today
NOVEMBER 22, 2023
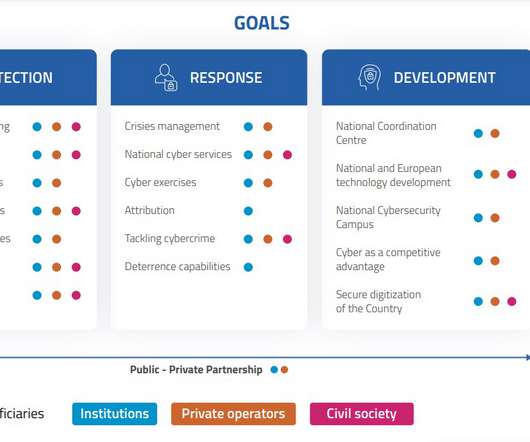
Australia Envisions Cybersecurity Leadership in the Pacific With New Strategy The Australian government says it will mandate ransomware reporting by businesses, boost law enforcement capacity and fund startups with innovative cybersecurity solutions under a strategy unveiled Monday. "We














































Let's personalize your content