Cloned Voice Tech Is Coming for Bank Accounts
Data Breach Today
APRIL 12, 2024
Experts Warn AI Tools Can Now Compromise Voice Password Systems Used by Many Banks At many financial institutions, your voice is your password.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
APRIL 12, 2024
Experts Warn AI Tools Can Now Compromise Voice Password Systems Used by Many Banks At many financial institutions, your voice is your password.

Security Affairs
MARCH 20, 2024
The Pokemon Company resets some users’ passwords in response to hacking attempts against some of its users. The Pokemon Company announced it had reset the passwords for some accounts after it had detected hacking attempts, Techcrunch first reported. The company was likely the target of credential stuffing attacks.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
OCTOBER 24, 2022
It involves regularly changing passwords and inventorying sensitive data. With proper training, employees can prevent these attacks before they happen. While the protection of the company’s assets can never be completely guaranteed, security awareness training should be a top priority for business owners.

KnowBe4
DECEMBER 4, 2023
When you think of KnowBe4, you probably think of phishing training, good password hygiene modules, security awareness, or maybe even data protection compliance such as GDPR.

Dark Reading
AUGUST 10, 2020
When picking passwords, users often fall back on certain insecure patterns, but good habits can be learned using simple games, a group of researchers find.

Schneier on Security
OCTOBER 12, 2022
Researchers have used thermal cameras and ML guessing techniques to recover passwords from measuring the residual heat left by fingers on keyboards. But, honestly, if someone can train a camera at your keyboard, you have bigger problems. “ABS” is Acrylonitrile Butadiene Styrene, which some keys are made of. News article.

The Last Watchdog
OCTOBER 5, 2023
5, 2023 – Today, the Healey-Driscoll Administration kicked off Cybersecurity Month in Massachusetts with the announcement of $1,136,911 in funding to develop a new cybersecurity training center at MassBay Community College and support the existing center at Bridgewater State University. Worcester, Mass.,

Dark Reading
AUGUST 15, 2023
The AI model trained on typing recorded over a smartphone was able to steal passwords with 95% accuracy.
Krebs on Security
JANUARY 7, 2020
Late last year saw the re-emergence of a nasty phishing tactic that allows the attacker to gain full access to a user’s data stored in the cloud without actually stealing the account password. “Even employees who are trained on security are trained to make sure it’s a legitimate site before entering their credentials.

The Last Watchdog
MARCH 24, 2022
It can be a real hassle to keep track of the passwords you use. So many people use the same combination of username and password for every account. You see, these days, many data breaches could be traced back to people using the same password across multiple accounts. And finding that password is even easier.

KnowBe4
NOVEMBER 6, 2023
In an analysis of web pages identified as admin portals, some incredibly weak passwords were identified – and some of them are going to really surprise you.
IT Governance
MAY 5, 2022
“My password was hacked”: it’s one of the oldest excuses in the book for people who post something regrettable online. All of us have dozens of accounts that are only one password breach away from compromising sensitive information. It’s why the tech giant Intel created World Password Day, which is celebrated on 5 May 2022.

The Last Watchdog
NOVEMBER 19, 2023
Fluent in American English, a gang member convinced a help desk worker to provide a one-time password to log into the systems. But persuading a poorly trained help desk operator to provide a temporary password isn’t, unfortunately, out of the ordinary. Reduce the amount of time a temporary password can be used.

IT Governance
JUNE 8, 2020
What does cyber security training teach you? A cyber security training course will increase your IT team’s awareness of your organisation’s wider defence mechanisms. These are issues that your IT team can help mitigate once they have the necessary training. Book this training course today to get 25% off.

Security Affairs
APRIL 15, 2022
Now is the moment to train your personnel on security best practices, if you haven’t already. Experian predicts 2022 will be a hangover from the “cyberdemic” of 2021, making it crucial to stay ahead by designing a cybersecurity training program for employees and strengthening defenses.

IT Governance
APRIL 20, 2020
With the coronavirus pandemic keeping us stuck inside and struggling to find ways to remain productive, now might be the perfect time to take an online cyber security training course. Certified Cyber Security Foundation Training Course. 3 reasons cyber security training is essential. Certified GDPR Foundation Training Course.

Dark Reading
FEBRUARY 10, 2023
A tailored spear-phishing attack successfully convinced a Reddit employee to hand over their credentials and their one-time password, but soon after, the same worker notified security.
KnowBe4
JANUARY 16, 2023
We’re thrilled to announce that the power of KnowBe4’s most popular free password security tool has been brought to your KnowBe4 console as a new feature!

IT Governance
OCTOBER 25, 2019
Cyber security training is one of the most effective ways of improving your organisation’s defences against security incidents. Yet, according to a report by Centrify , 77% of UK workers say they’ve never received any form of cyber skills training. 23 million people use ‘123456’ as their password.

The Last Watchdog
MARCH 4, 2024
This means using longer passwords — at least 16 characters , as recommended by experts — in a random string of upper and lower letters, numbers, and symbols. Train staff regularly. A solid cyber security culture requires regular training on the latest best practices so people know what to look out for and what to do.

Dark Reading
NOVEMBER 7, 2018
Researchers say companies need to rethink their password training and take a more holistic approach to security.

The Last Watchdog
MAY 24, 2022
This is one giant leap towards getting rid of passwords entirely. Excising passwords as the security linchpin to digital services is long, long overdue. Password abuse at scale arose shortly after the decision got made in the 1990s to make shared secrets the basis for securing digital connections. Our brains just won’t do it.”.

IT Governance
NOVEMBER 13, 2019
Cyber security awareness training is one of the most important steps an organisation can take to protect its systems. Unfortunately, research by Privatise Business VPN suggests that staff aren’t getting the training they need to secure their organisation’s systems. The benefits of cyber security training. Your staff.

Adam Shostack
FEBRUARY 24, 2019
Chris Eng said “ Someone should set up a GoFundMe to send whoever wrote the hit piece on password managers to a threat modeling class. There was a set of flaws where master passwords were accessible in memory, and thus an attacker with a debugger could get your master password and decrypt all your passwords.

Security Affairs
APRIL 23, 2020
It’s become evident that many businesses lack the necessary anti-hacking training. Lack of Necessary Training in New Users. By automating password generation and access windows, companies can ensure they have exclusive, secure access to their RPA. Rising RPA Adoption. The global RPA market grew from $800 million to $2.9

Krebs on Security
OCTOBER 1, 2021
From there, the attackers can reset the password for almost any online account tied to that mobile number, because most online services still allow people to reset their passwords simply by clicking a link sent via SMS to the phone number on file.
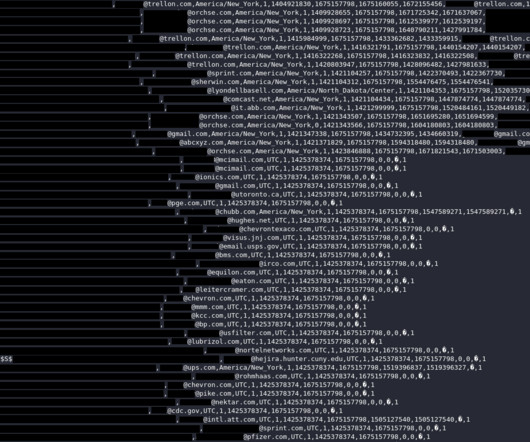
Security Affairs
AUGUST 31, 2023
The National Safety Council leaked thousands of emails and passwords of their members, including companies such as NASA and Tesla. The National Safety Council has leaked nearly 10,000 emails and passwords of their members, exposing 2000 companies, including governmental organizations and big corporations.

Adapture
JULY 30, 2021
Credential Stuffing vs Brute Force Over the past couple of decades, we’ve been constantly reminded to use strong passwords. Strong passwords were supposed to fend off brute force attacks, the most commonly used attack vector to break into an account. In fairness, strong passwords can still thwart brute force.

The Last Watchdog
DECEMBER 8, 2022
This overconfidence is cause for concern for many cybersecurity professionals as humans are the number one reason for breaches (how many of your passwords are qwerty or 1234five?). Only 28 percent don’t use repeated passwords•Only 20 percent use a password manager. Not using repeated passwords.

IT Governance
OCTOBER 24, 2019
One of cyber criminals’ favourite ways of hacking organisations is through brute-force or ‘password spraying’ attacks, which bombard targets with login attempts using lists of common passwords. million people in the UK use ‘123456’ as their password. million are securing their accounts with ‘password’ and 3.8

IT Governance
JANUARY 24, 2024
Data leaks from years ago are still being used today to compromise accounts, telling us that many people don’t change their password after a breach, or even at some regular frequency. This is from a direct perspective – to enable a supply chain attack, for example – but also because of poor password habits.

KnowBe4
MARCH 30, 2022
A new report suggests that everything from endpoints, to passwords, to training, to security policies, to a lack of awareness is all contributing to much higher risk of cyberattack.

IT Governance
JULY 4, 2018
After all, technology won’t help you if an employee leaves their password written down for anyone to see or misplaces a removable device. 2) Train your staff : what you teach your staff – and how those lessons are delivered – will depend on what they need to know. How to deliver training. What you should be doing.

IBM Big Data Hub
APRIL 15, 2024
They typically follow a one-size-fits-all approach, with employees completing annual generic computer-based training with some slick animation and a short quiz. This refers to their knowledge and skills to engage in safe online practices, such as creating strong passwords and recognizing phishing attempts.

IT Governance
FEBRUARY 11, 2019
An advert is currently running in which a man gets his password hacked because, the ad implies, he wasn’t using a VPN (virtual private network). The man’s password? Sooner rather than later, someone will guess your password and stumble into a wealth of sensitive information. Are we all so useless? Security vs convenience.

The Last Watchdog
FEBRUARY 5, 2024
Implement strong password policies and multi-factor authentication to prevent unauthorized access. User education: Regularly train employees on cybersecurity best practices, including recognizing phishing attempts and secure handling of sensitive information. Robust access control. Comprehensive monitoring.

IT Governance
AUGUST 3, 2023
Vishing attempts to con potential victims into surrendering personal information such as passwords, card details and PINs, which can be used for identity theft. However, that software itself contains malware – typically a keylogger that tracks everything that the user types on their machine, such as passwords and other sensitive information.

IT Governance
MAY 17, 2018
This week, we discuss the exposure of millions of Facebook users’ data, security failings in train passenger networks and Kaspersky Lab’s relocation to Switzerland. Have you ever used – or perhaps, given its reliability, I should say tried to use – Wi-Fi on a train? Here are this week’s stories.
eSecurity Planet
AUGUST 19, 2022
Browsers allow users to maintain authentication, remember passwords and autofill forms. Cybercriminals can use them to change passwords and emails associated with user accounts, or trick the victims into downloading additional malware, or even deploy other exploitation tools such as Cobalt Strike and Impacket kit.

eSecurity Planet
DECEMBER 10, 2023
Often, they start their journey by stealing an initial set of credentials or somehow spoofing the application or network so they don’t have to use a password at all. Credential Stuffing In a credential stuffing attack, a threat actor will attempt multiple commonly-used and known passwords, usernames, or both to see if they work.

The Last Watchdog
SEPTEMBER 25, 2023
Employee training is crucial. Training team members regularly with real-life scenarios will help them spot potential threats and protect them from exposing your business. Taking an active role Your cybersecurity policy should address your employees and technology systems. Set access privileges and internal controls.
IT Governance
JUNE 15, 2022
This is a security mechanism that requires people to enter a second piece of information in addition to a password in order to log on. Weak passwords. For all the advancements that organisations have made to secure their systems, password practices remain a huge problem. Passwords are usually compromised in one of two ways.

Rocket Software
OCTOBER 25, 2020
These experts, along with other Rocketeers, will be participating in this year’s IBM TechU virtual training event. Passwords are the most common method for user authentication. The post Join us for deep technical content and training at IBM TechU appeared first on The Rocket Software Blog. October 28, 11:30 AM ET.
Security Affairs
OCTOBER 17, 2023
This is happening despite an exponential increase in organizational cyber training over the past decade. If your friend or colleague is suddenly asking you for money or to change your password, call them on the phone and ask if they really sent the message. You should always stop and verify. Verify domain names – they could end in.co
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content