Introducing Jamf How-to Video Shorts
Jamf
NOVEMBER 22, 2022
Check out Jamf how-to video shorts for no-nonsense training and support tutorials from your Jamf Customer Success team.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Jamf
NOVEMBER 22, 2022
Check out Jamf how-to video shorts for no-nonsense training and support tutorials from your Jamf Customer Success team.
Preservica
NOVEMBER 9, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! Sharing meeting minutes and videos are one of the ways that public sector employees meet compliance and open records regulations.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
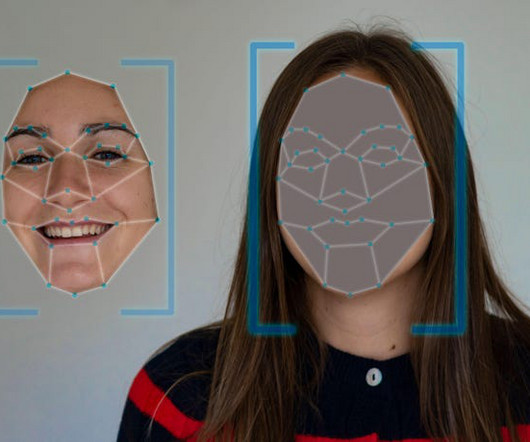
Dark Reading
MARCH 13, 2023
AI-generated videos pose as tutorials on how to get cracked versions of Photoshop, Premiere Pro, and more.

Schneier on Security
DECEMBER 19, 2022
The Ukrainian army has released an instructional video explaining how Russian soldiers should surrender to a drone: “Seeing the drone in the field of view, make eye contact with it,” the video instructs. Soldiers should then raise their arms and signal they’re ready to follow.
Krebs on Security
MAY 21, 2021
” HOW TO SPOT A JOB SCAM. ” Here are some other telltale signs of a job scam, as per the FBI: -Interviews are not conducted in-person or through a secure video call. . “So my dad said, ‘Troll him back, and tell him you want a signing bonus via money order.’ I never heard from him again.”
IT Governance
APRIL 5, 2023
IT Governance Podcast 2023-7: Capita, ChatGPT and TikTok (yet again) 5th April 2023 How to Prevent Malware Attacks: 8 Tips for 2023 5th April 2023 List of Data Breaches and Cyber Attacks in March 2023 – 41.9 For example, a video link might ask you to install a bogus video player plugin, which contains malware.

WIRED Threat Level
FEBRUARY 29, 2024
Every time someone in the UK searched for child abuse material on Pornhub, a chatbot appeared and told them how to get help.
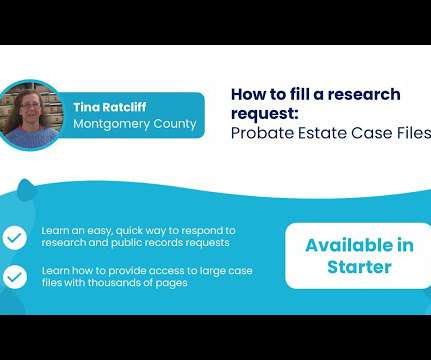
Preservica
NOVEMBER 30, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to fill a research request: Probate Estate Case Files. Watch her video below to learn how to do this yourself.

WIRED Threat Level
AUGUST 15, 2021
Here's how to set up vanishing texts, photos, or videos in most popular chat apps. Need to be discreet?

Adapture
JULY 1, 2021
7 Tips for Video Interviews. 2020 certainly taught us how to live life behind the lens of a video conferencing camera. How should you prepare for a conversation with your potential next employer when an in-person meeting isn’t possible? Long before the interview, make sure you know how to use the technology.
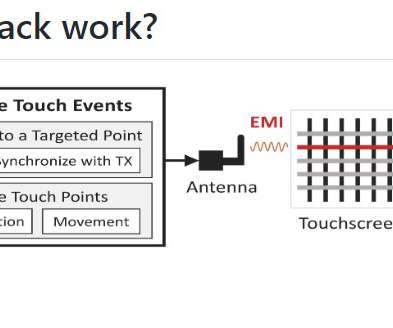
Security Affairs
MAY 27, 2022
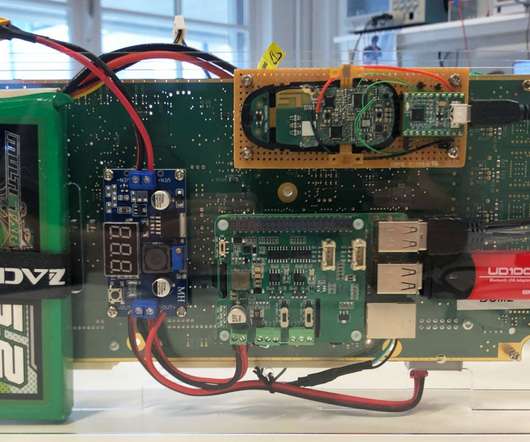
The researchers demonstrated how to inject two types of basic touch events, taps and swipes, into targeted locations of the touchscreen. Below are a couple of video PoCs of attacks devised by the experts that show GhostTouch attack to answer the phone call and connect the malicious Bluetooth. and a distance of up to 40mm.
IT Governance
APRIL 15, 2020
Maybe you feel less guilty about having a mid-morning video chat with a colleague in lieu of your normal coffee break. That’s why each week we’re sharing our experiences, advice and guidance on how to manage through the pandemic. Let’s take a look at what this week has to offer. Cyber attacks. Expert advice.

Preservica
NOVEMBER 29, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to preserve social media content: Twitter records. Watch the video below to learn how to do this yourself.

The Last Watchdog
MAY 19, 2022
Wikipedia uses a CMS for textual entries, blog posts, images, photographs, videos, charts, graphics, and “ talk pages ” that help its many contributors collaborate. For instance, the The Last Watchdog article you are reading uses a CMS to store posts, display them in an attractive manner, and provide search capabilities.

Adam Shostack
JANUARY 10, 2019
They even “let” you edit your own videos. Like doing a video course so we could show me drawing on a whiteboard, rather than showing fancy pictures and implying that that’s what you need to create to threat model like the instructor. My producer Rae worked with me, and taught me how to write for video.

Preservica
FEBRUARY 22, 2022
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to preserve and share the legacy of your county. This educational series will regularly feature new video assets.

Preservica
NOVEMBER 29, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to preserve and share the legacy of your county. This educational series will regularly feature new video assets.

Preservica
FEBRUARY 22, 2022
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to bring community history to life using Preservica Starter. This educational series will regularly feature new video assets.
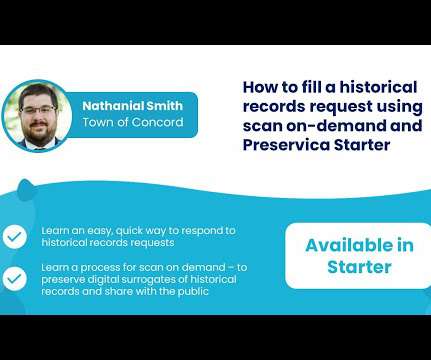
Preservica
NOVEMBER 30, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to fill a historical records request using scan on-demand and Preservica Starter. Want more like this? Check back to see what’s new!

Security Affairs
JULY 10, 2022
The researchers also published a set of PoC videos, below is an attack against a Honda CRV: The researchers pointed out that there is no possibility to discover if someone has exploited the flaw against a model because the exploitation does not leave any traces in traditional log files. How to fix the issue? Pierluigi Paganini.
Preservica
FEBRUARY 22, 2022
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to provide easy online access to grantee and grantor indexes. Watch this video to find out. Want more like this?

Preservica
NOVEMBER 29, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to bring community history to life using Preservica Starter. This educational series will regularly feature new video assets.
Preservica
NOVEMBER 29, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to provide easy online access to grantee and grantor indexes. Watch this video to find out. Want more like this?
Preservica
NOVEMBER 29, 2021
Welcome to the "How we do it" Video Series. If you are a Clerk, Records Manager or Archivist for City or County Government, our practical “How we do it” videos are for you! How to create and share a collection of historical exhibition materials. This educational series will regularly feature new video assets.

eSecurity Planet
OCTOBER 31, 2023
We explore the art of writing effective penetration testing reports in the sections below: How to Write a Great Pentest Report in 6 Steps The process of writing a great penetration test report is straightforward and can be covered in six key steps. Usable reports enable these goals efficiently and effectively. You can unsubscribe at any time.

CILIP
JANUARY 8, 2024
Children’s author Julia Donaldson joins the Great School Libraries Campaign and shares how everyone can help to ensure a school library in every school in a new video. Will ‘Project Hope’ protect public libraries? which identified some positives, as well as inequalities in the school system across England, Scotland and Wales.

Hunton Privacy
JULY 26, 2019
The European Data Protection Board (the “EDPB”) recently adopted its Guidelines 3/2019 on processing of personal data through video devices (the “Guidelines”). Although the Guidelines provide examples of data processing for video surveillance, these examples are not exhaustive.

Security Affairs
MAY 4, 2022
Below is a video PoC published by the researcher that shows a DLL hijacking attack against a sample of the Conti ransomware. The post An expert shows how to stop popular ransomware samples via DLL hijacking appeared first on Security Affairs. All basic tests were conducted successfully in a virtual machine environment.”
Security Affairs
NOVEMBER 23, 2020
Boffins have demonstrated how to steal a Tesla Model X in a few minutes by exploiting vulnerabilities in the car’s keyless entry system. The researchers also published the following video PoC for the attack: Back in 2018 time, the COSIC research team demonstrated a similar attack against the key fob of a Tesla Model S.

The Texas Record
APRIL 11, 2018
We are pleased to announce a new online video course for state agency records management officers and records liaisons. Click here to access the video on the course page. This 30 minute video course covers the basic concepts of records management: legal obligations, definitions, and how to read a retention schedule.

IBM Big Data Hub
NOVEMBER 30, 2023
Use engaging content, images and videos to showcase the working environment. Video interviews: Save time and resources and get a more comprehensive understanding of candidates’ communication skills and demeanor using video interviewing platforms. Describe the application process.

Security Affairs
MAY 3, 2021
Which are the most common causes of a Data Breach and how to prevent It? How can organizations prevent it? It might include anything from names to private photos or video footage. Thus, it is extremely important for businesses to be vigilant about how their data is stored online. Pierluigi Paganini.

IT Governance
NOVEMBER 30, 2021
The shift towards remote working has been made possible due to technological advancements in the way we access information and systems, and how we interact with teammates. Organisations have learned that tools such as video conferencing, Cloud services and online content management systems are effective and affordable.

Thales Cloud Protection & Licensing
JANUARY 28, 2020
The latter measure is especially important, as data-in-motion encryption helps shield an organization’s data, video, voice and metadata from eavesdropping, surveillance and other interception attempts. The post How to Keep Your Information Safe for Data Privacy Day 2020 appeared first on Data Security Blog | Thales eSecurity.
WIRED Threat Level
AUGUST 14, 2022
Keep private photos, videos, and documents away from prying eyes.
WIRED Threat Level
APRIL 5, 2020
Zoom's a great video chat platform, but a few simple steps also make it a safe one. Prying bosses.

eSecurity Planet
JULY 7, 2023
So how can you tell if your organization is under a DDoS attack — rather than experiencing a viral surge in website traffic — and are there early warning signs that can help you respond to DDoS attacks faster? If you’re experiencing a DDoS attack, see How to Stop DDoS Attacks in Three Stages.

Security Affairs
JUNE 3, 2019
Supra Smart Cloud TV allows remote file inclusion in the openLiveURL function, which allows a local attacker to broadcast fake video without any authentication. Technical Observation: We are abusing `openLiveURL()` which allows a local attacker to broadcast video on supra smart cloud TV. m3u8) format based video.
Security Affairs
JANUARY 5, 2021
A German security researcher demonstrated how to break, once again, the Google Audio reCAPTCHA with Google’s own Speech to Text API. Tschacher published a video PoC of the attack that demonstrates how a bot can solve the Google audio reCAPTCHA using the speech-to-text API. Pierluigi Paganini.
IT Governance
APRIL 22, 2020
Similarly, imagine if you’re on a video call and leave the room for a moment. During the lockdown, we’ve noticed that many of our line managers have set up regular one-to-one video calls with their team in addition to scheduled work meetings. Guidance on how managers should address these problems.

WIRED Threat Level
NOVEMBER 11, 2020
It's time to do something about those photos and videos automatically saving to your camera roll.

Dark Reading
JUNE 18, 2020
The CISO of Amazon Prime Video discusses his approaches to a slimmed-down budget. CISOs are never going to have all the finances they want. Hard choices must be made.

Record Nations
JULY 6, 2020
Learn more in this video about what makes organized records […]. The post 4 Signs of Poor Records Management and How to Fix Them appeared first on Record Nations.
Security Affairs
OCTOBER 26, 2023
.” The researchers published a series of PoC videos for attacks to recover: Instagram Credentials when a target uses an autofilling credential manager to sign into Instagram with Safari on macOS. The video shows how to recover the subject lines of the Gmail account’s most recent messages on an iPad.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content