UK won the Military Cyberwarfare exercise Defence Cyber Marvel 2 (DCM2)
Security Affairs
FEBRUARY 24, 2023
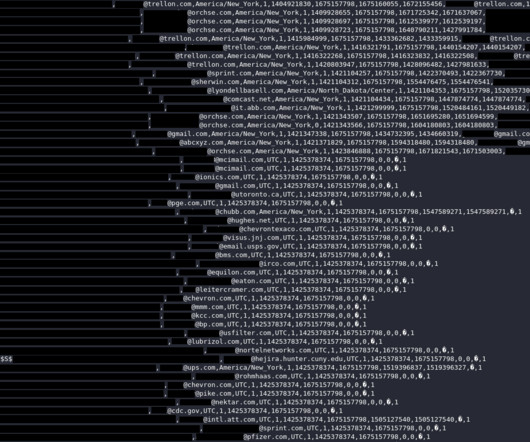
Defence Cyber Marvel 2 (DCM2) is the largest Western Europe-led cyber exercise that took place in Tallinn with 34 teams from 11 countries. This year, 750 cyber specialists have participated in the military cyberwarfare exercise. ” reads the press release published by the UK Ministry of Defence. .










































Let's personalize your content