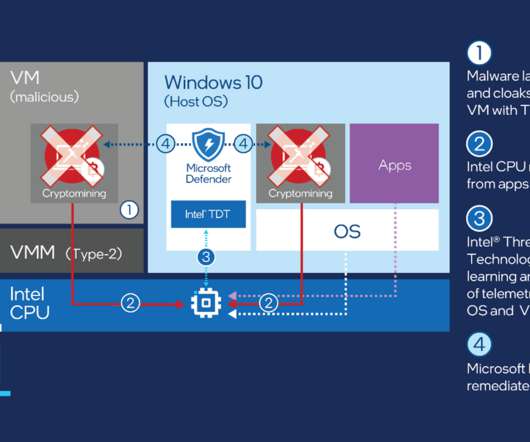
Microsoft Defender uses Intel TDT technology against crypto-mining malware
Security Affairs
APRIL 27, 2021
Cryptojacking malware allows threat actors to secretly mine for cryptocurrency abusing computational resources of the infected devices. “TDT leverages a rich set of performance profiling events available in Intel SoCs (system-on-a-chip) to monitor and detect malware at their final execution point (the CPU). Pierluigi Paganini.


























Let's personalize your content