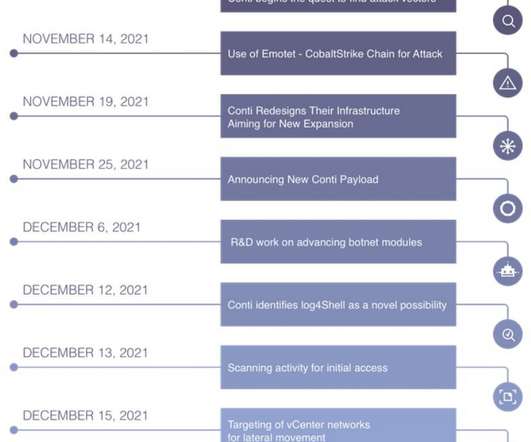
Conti ransomware gang exploits Log4Shell bug in its operations
Security Affairs
DECEMBER 17, 2021
Recently the Conti gang hit the attack on the Australian energy CS Energy and threaten to leak the stolen files. After the disclosure of the exploit, Microsoft researchers reported that Nation-state actors from China, Iran, North Korea, and Turkey are now abusing the Log4Shell (CVE-2021-44228) in the Log4J library in their campaigns.























Let's personalize your content