SilverTerrier gang uses COVID-19 lures in BEC attacks against healthcare, government organizations
Security Affairs
MAY 9, 2020
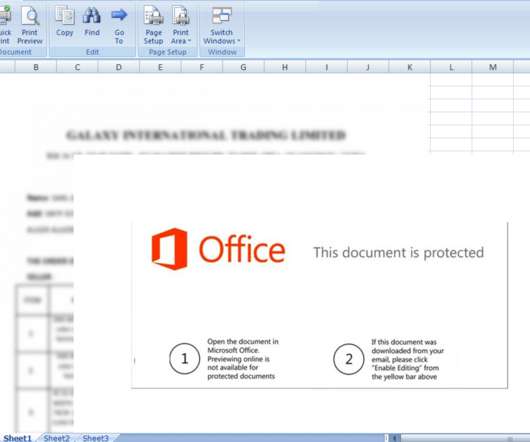
Nigerian cyber gang SilverTerrier, specialized in BEC attacks, used COVID-19 lures in recent attacks on healthcare and government organizations. SilverTerrier has been active since at least 2014, it is a collective of over hundreds of individual threat actors. . “On April 8, 2020, we witnessed the most recent campaign by this actor.




























Let's personalize your content