Another Event-Related Spyware App
Schneier on Security
NOVEMBER 15, 2022
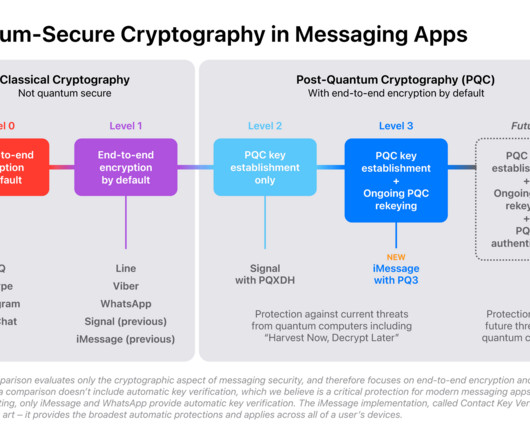
This month, it’s Egypt’s COP27 Summit app : The app is being promoted as a tool to help attendees navigate the event. Even messages shared via encrypted services like WhatsApp are vulnerable, according to POLITICO’s technical review of the application, and two of the outside experts.





































Let's personalize your content