Norton 360 Now Comes With a Cryptominer
Krebs on Security
JANUARY 6, 2022
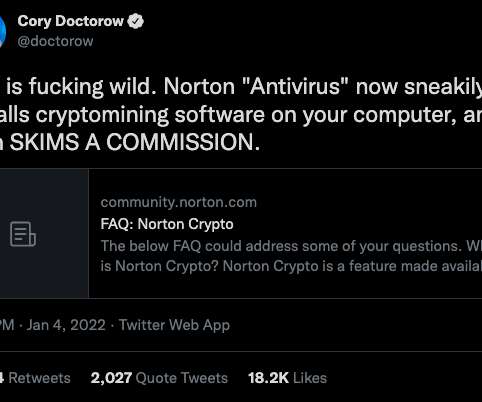
Norton 360 , one of the most popular antivirus products on the market today, has installed a cryptocurrency mining program on its customers’ computers. Norton’s parent firm says the cloud-based service that activates the program and allows customers to profit from the scheme — in which the company keeps 15 percent of any currencies mined — is “opt-in,” meaning users have to agree to enable it.


































Let's personalize your content