Honda Confirms Hack Attack Disrupted Global Production
Data Breach Today
JUNE 10, 2020
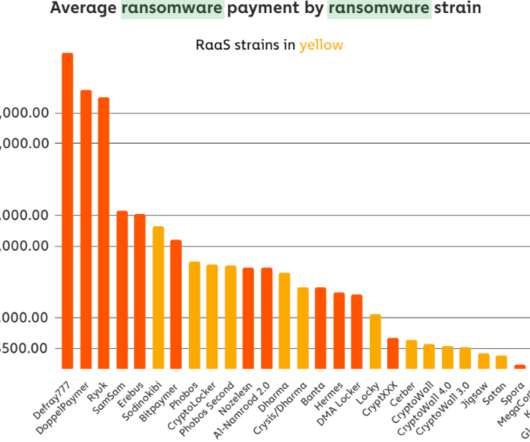
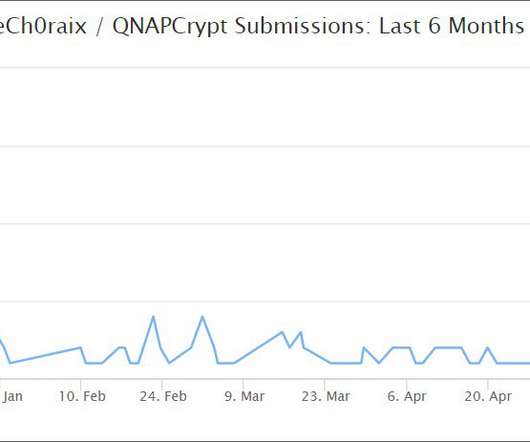
Ransomware Is the Likely Culprit, Security Experts Say Japanese auto giant Honda has confirmed that it sustained a hack attack earlier this week that has affected production operations at several of its global facilities, including plants in the U.S., Japan, Turkey and Italy. Security researchers suspect ransomware is the likely culprit.



































Let's personalize your content