3 Everyday Things in Your Office That Could Lead to a Data Breach
Adam Levin
NOVEMBER 29, 2019
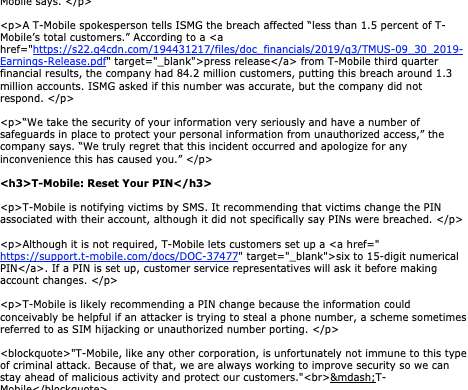
When you think about cyberthreats , what comes to mind? An extortionist announcing your doom with a dark monitor and a laughing skull? State-sponsored cyber-warriors working from a secure command post? President Trump’s certain, “somebody sitting on their bed that weighs 400 pounds ?” Chances are good, your version of cyber risk involves one of the above “types” hunched over a keyboard deploying massively sophisticated malware on the networks of unsuspecting bus
































Let's personalize your content