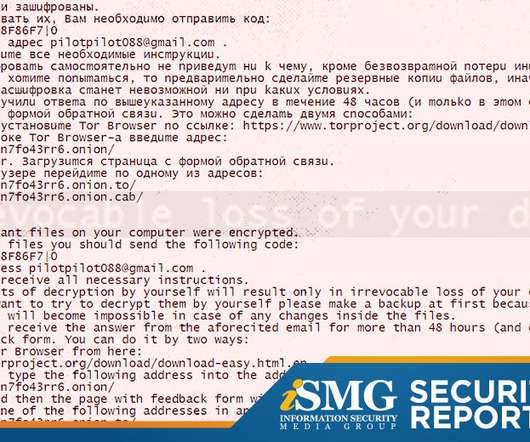
Latest Ransomware Attacks Show Diversity of Victims
Data Breach Today
NOVEMBER 20, 2019
What Do They Have in Common? Difficult Recovery A ransomware attack against a chain of veterinary medicine clinics plus an attack against a New York hospital show this threat remains pervasive, victims are diverse and recovery is difficult.








































Let's personalize your content