Twitter Hacking for Profit and the LoLs
Krebs on Security
JULY 22, 2020
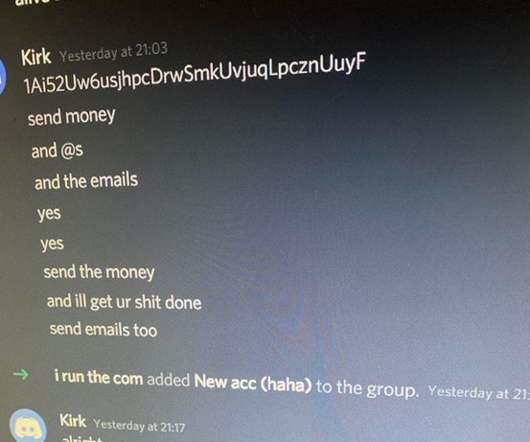
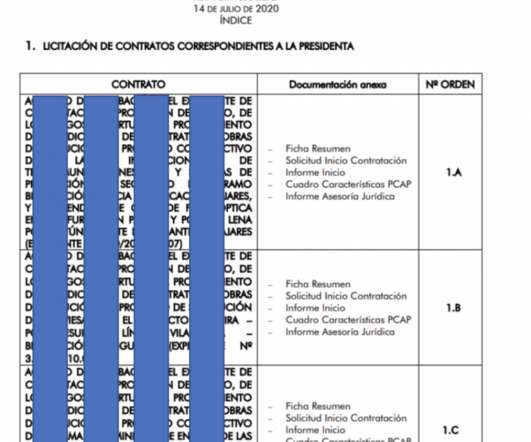
The New York Times last week ran an interview with several young men who claimed to have had direct contact with those involved in last week’s epic hack against Twitter. These individuals said they were only customers of the person who had access to Twitter’s internal employee tools, and were not responsible for the actual intrusion or bitcoin scams that took place that day.
































Let's personalize your content