6 Free Cybersecurity Training and Awareness Courses
Dark Reading
MAY 12, 2020
Most are designed to help organizations address teleworking risks related to COVID-19 scams.

Dark Reading
MAY 12, 2020
Most are designed to help organizations address teleworking risks related to COVID-19 scams.
Data Breach Today
MAY 11, 2020
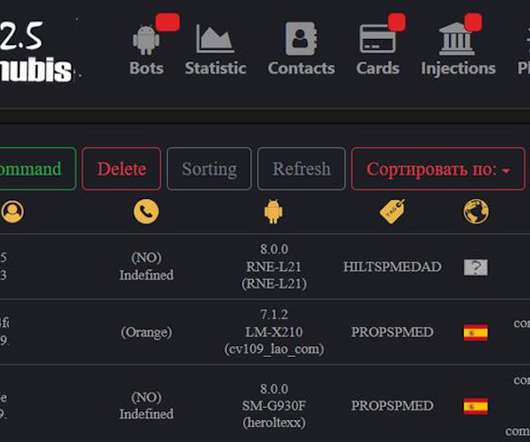
Powerful Platform Can Spot If Victim Is Looking at the Screen Anubis, one of the most potent Android botnets, apparently is getting a refresh a year after its source code was leaked, security researchers say. The changes could help fraudsters more closely monitor activity on hacked devices.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Data Breach Today
MAY 12, 2020
Researchers Say New Features and Functionality Added The operators behind the Zeus Sphinx malware have added new features and functionality to the Trojan, and more cybercriminals have deployed it within phishing campaigns that use the COVID-19 crisis as a lure, according to IBM X-Force. The Trojan has become more efficient at stealing banking data.
Jamf
MAY 12, 2020
If the upfront cost is more, how can Mac be less expensive than PC? We examine the numbers and put the Mac versus PC in the enterprise myths to bed.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.
WIRED Threat Level
MAY 10, 2020
Pick who sees your tweets, posts, and stories—and choose what you want to see, too.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Data Breach Today
MAY 13, 2020
FBI, CISA Issue Joint Warning to Organizations Conducting Research Hacking groups linked to China's government are targeting research and healthcare facilities that are working on developing vaccines, testing procedures and treatments for COVID-19, the FBI and the U.S. Cybersecurity and Infrastructure Security Agency warn in an alert.

Data Breach Today
MAY 13, 2020
Australian Shipping Giant, Hit With Nefilim Ransomware, Vows to Not Pay Ransom Australian shipping giant Toll Group has vowed to again not pay a ransom after suffering its second ransomware attack of the year. In the latest incident, however, the company warns that attackers also stole corporate data - and it may get leaked.

Threatpost
MAY 11, 2020
The infostealer has gone above and beyond in its new anti-analysis and obfuscation tactics.
Krebs on Security
MAY 11, 2020
Diebold Nixdorf , a major provider of automatic teller machines (ATMs) and payment technology to banks and retailers, recently suffered a ransomware attack that disrupted some operations. The company says the hackers never touched its ATMs or customer networks, and that the intrusion only affected its corporate network. Canton, Ohio-based Diebold [ NYSE: DBD ] is currently the largest ATM provider in the United States, with an estimated 35 percent of the cash machine market worldwide.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

The Last Watchdog
MAY 13, 2020
Chief Information Security Officers were already on the hot seat well before the COVID-19 global pandemic hit, and they are even more so today. Related: Why U.S. cybersecurity policy needs to match societal values CISOs must preserve and protect their companies in a fast-changing business environment at a time when their organizations are under heavy bombardment.
Data Breach Today
MAY 14, 2020
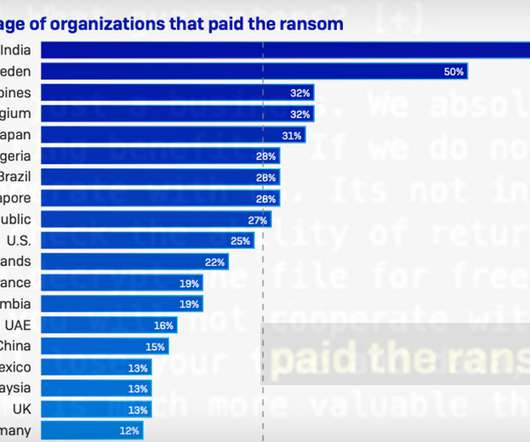
Funding Criminals Perpetuates Cybercrime Security experts and law enforcement officials have long argued that paying ransoms doesn't pay. For starters, it directly funds the cybercrime ecosystem and makes it attractive for criminals to keep launching ransomware attacks.

AIIM
MAY 12, 2020
Each year brings a rapid increase in technological advancements that can benefit both your personal and professional life. Constant tech advancements can make it feel hard to keep up with competing businesses if your company isn't adapting fast enough. In this day and age, digital transformations are integral for a growing business's future, as technology changes the advancements and operations of every company.

Krebs on Security
MAY 12, 2020
Microsoft today issued software updates to plug at least 111 security holes in Windows and Windows-based programs. None of the vulnerabilities were labeled as being publicly exploited or detailed prior to today, but as always if you’re running Windows on any of your machines it’s time once again to prepare to get your patches on. May marks the third month in a row that Microsoft has pushed out fixes for more than 110 security flaws in its operating system and related software.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
Hunton Privacy
MAY 12, 2020
The Dutch Data Protection Authority ( Autoriteit Persoonsgegevens , the “Dutch DPA”) recently imposed a €750,000 fine on a company for unlawful processing of employees’ fingerprints for attendance taking and time registration purposes. Biometric data, such as fingerprints, qualify as sensitive personal data under the EU General Data Protection Regulation (the “GDPR”) and their processing is subject to more stringent requirements.

Data Breach Today
MAY 14, 2020
Another Example of How Cybercriminals' Tactics Are Changing Magellan Health, a U.S. managed care company that focuses on specialty areas of healthcare, says it was hit by a ransomware attack that involved the exfiltration of data. Ransomware gangs are increasingly going beyond encrypting data, stealing information to put more pressure on victims to pay ransoms.

AIIM
MAY 14, 2020
We're now operating twenty years into a new millennium. But despite the futuristic potential, many organizations continue to operate with systems and software that are a decade or more behind the times. Organizations that continue to operate in the past will be challenged to keep pace today – and in the future. Think about the technology you use in your personal life.

IT Governance
MAY 14, 2020
With the UK slowly beginning to ease its lockdown measures, organisations have a lot to consider. Some employees who can’t work from home will be itching to get back into the office, in which case you’ll need to take the appropriate steps to make sure they are able to work safely and follow social distancing rules. Other employees will have come to appreciate the benefits of working from home and want to continue to do so.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

IBM Big Data Hub
MAY 12, 2020
AI is transforming how businesses operate and deliver value, while simultaneously improving efficiencies across the organization. Governments have taken an increasingly important role in the advent of COVID-19 as citizens look to government agencies for trusted information for their individual safety, well-being and beyond – to both support and benefit themselves socially, economically and emotionally.

Data Breach Today
MAY 15, 2020
Cybersecurity Expert Reviews Key Questions to Ask Organizations must carefully re-examine their security procedures to make sure they're adequate for the new work-from-home environment during the COVID-19 crisis, says Shelton Newsham, a British law enforcement official who specializes in cybersecurity. He reviews key questions to ask.

DLA Piper Privacy Matters
MAY 13, 2020
The Information Commissioner’s Office (“ ICO ”) has published guidance for employers on complying with data protection law when taking steps to manage Covid-19 health and safety risk in the workplace (“ Guidance ”). The Guidance focuses on ‘testing’ of employees (which includes collecting data about symptoms and the conducting of temperature checks, and well as collecting data about Covid-19 test results), but also touches on other measures which businesses might be considering in order to moni

Security Affairs
MAY 11, 2020
During COVID-19 outbreak data processors have to be extra vigilant to maintain their compliance with data protection authorities like GDPR. COVID-19 has abruptly changed the world. It has imposed online learning and earning, which in turn has open new doors of cybersecurity threats and data breaches. Now the data processors have to be extra vigilant to maintain their compliance with data protection authorities like GDPR.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Micro Focus
MAY 14, 2020
Micro Focus Virtual Universe launches on May 19! There’s still time to register for this free event—join fellow technology leaders, innovators and Micro Focus solution experts and partners to see how we can help you drive value and innovate faster, with less risk, in the race to digital transformation. Here’s my Top 10 reasons: Top. View Article.

Data Breach Today
MAY 14, 2020
Connected Devices Could Allow Attackers to Target Industrial Systems, Trend Micro Reports The increasing use of internet-connected devices in manufacturing facilities is opening up new ways for hackers to target so-called "smart" factories with unconventional attack methods, according to an analysis by security firm Trend Micro and the Polytechnic University of Milan.

DXC Technology
MAY 13, 2020
Enterprise clients have looked to automate IT support for several years. With millions of employees across the globe now working from home, support needs have increased dramatically, with many unprepared enterprises suffering from long service desk wait times and unhappy employees. Many companies may have already been on a gradual pace to exploit digital solutions […].

Threatpost
MAY 15, 2020
A new threat group uses NSIS as an installer to target industrial companies with revolving payloads, including LokiBot, FormBook, BetaBot, Agent Tesla and Netwire.

Speaker: Nicholas Zeisler, CX Strategist & Fractional CXO
The first step in a successful Customer Experience endeavor (or for that matter, any business proposition) is to find out what’s wrong. If you can’t identify it, you can’t fix it! 💡 That’s where the Voice of the Customer (VoC) comes in. Today, far too many brands do VoC simply because that’s what they think they’re supposed to do; that’s what all their competitors do.

Security Affairs
MAY 15, 2020
Britain’s Ministry of Defence contractor Interserve has been hacked, intruders have stolen up to 100,000 past and present employees’ details. Interserve, a contractor for the Britain’s Ministry of Defence suffered a security breach, hackers have stolen up to 100,000 of past and current employees details. The company currently has around 53,000 employees.

Data Breach Today
MAY 14, 2020
Microsoft Spots Malicious Messages Spreading LokiBot Infostealer Fraudsters are honing their phishing emails tied to the COVID-19 crisis, using fake messages about business continuity plans and new payment procedures to spread the LokiBot information stealer, Microsoft researchers report.

IBM Big Data Hub
MAY 15, 2020
In Ohio, the tectonic shift occurred at 11:59 p.m. March 23, 2020 when the Department of Health Director implemented stay at home orders. In subsequent days and weeks, unknowns prevailed – despite an inundation of COVID-19 information, and often conflicting perspectives from government, healthcare and media sources. Points of view from colleagues, family and friends were abundant.
Let's personalize your content