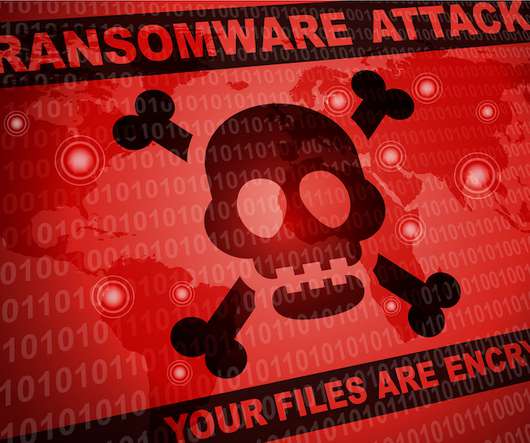
How Cybersecurity's Metrics of Misery Fail to Describe Cybercrime Pain
Dark Reading
JANUARY 2, 2020
Dollars lost and data records exposed are valuable measurements, but the true pain of a cybersecurity incident goes far beyond that. We asked infosec pros how they put words to the pain they feel when their defenses fall apart.



































Let's personalize your content