Securing Your Remote Workforce: A Coronavirus Guide for Businesses
Dark Reading
MARCH 30, 2020
Often the hardest part in creating an effective awareness program is deciding what NOT to teach.

Dark Reading
MARCH 30, 2020
Often the hardest part in creating an effective awareness program is deciding what NOT to teach.

Security Affairs
APRIL 3, 2020
Experts revealed that an unauthorized party compromised more than 200 million user records hosted somewhere within the U.S. in a Google Cloud database. . Many people are now so accustomed to cloud computing that they use it multiple times per day, whether to collaborate with co-workers, log into email accounts or do other everyday tasks. The convenience is undoubtedly one of its perks.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Schneier on Security
APRIL 1, 2020
Daniel's Hosting, which hosts about 7,600 dark web portals for free, has been hacked and is down. It's unclear when, or if, it will be back up.

WIRED Threat Level
MARCH 31, 2020
The hotel chain has suffered its second major breach in 16 months. Here's how to find out if you're affected.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Data Breach Today
APRIL 2, 2020
Andy Bates of Global Cyber Alliance on 'Work From Home, Secure Your Business' The Global Cyber Alliance is one of 13 nonprofit organizations that have banded together to offer businesses security tips for their newly remote workforces. Andy Bates, executive director of the alliance, discusses the coalition's core guidelines for reducing cyber risk.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.
Security Affairs
MARCH 30, 2020
The Zeus Sphinx malware is back, operators are now spreading it exploiting the interest in the Coronavirus outbreak. The Zeus Sphinx malware is back, it was observed in a new wave of attacks attempting to exploit the interest in the Coronavirus outbreak. Experts from IBM X-Force uncovered a hacking campaign employing the Zeus Sphinx malware, as known as Zloader or Terdot , that focus on government relief payments. .

Security Affairs
MARCH 29, 2020
In this post, I decided to share the details of the Coronavirus-themed attacks launched from March 22 to March 28, 2020. Threat actors exploit the interest in the COVID19 outbreak while infections increase worldwide, experts are observing new campaigns on a daily bases. Below a list of attacks detected this week. March 23 – COVID19-themed campaign delivers a new variant of Netwalker Ransomware.
Krebs on Security
MARCH 31, 2020
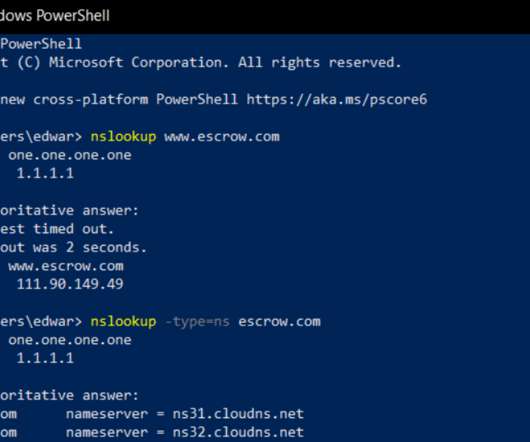
A spear-phishing attack this week hooked a customer service employee at GoDaddy.com , the world’s largest domain name registrar, KrebsOnSecurity has learned. The incident gave the phisher the ability to view and modify key customer records, access that was used to change domain settings for a half-dozen GoDaddy customers, including transaction brokering site escrow.com.

Data Breach Today
MARCH 30, 2020
Privacy Gaffe Blamed on Facebook's iOS Software Development Kit Zoom has apologized for sharing large sets of user data by default with Facebook, blaming the social network's software development kit, which it has removed from its iOS app. With COVID-19 driving unprecedented levels of remote working, video conferencing software is under the privacy and security microscope.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

The Last Watchdog
MARCH 31, 2020
DevOps is now table stakes for any company hoping to stay competitive. Speed and agility is the name of the game. And everyone’s all-in. Related: A firewall for microservices DevSecOps arose to insert security checks and balances into DevOps, aiming to do so without unduly degrading speed and agility. If you’re thinking that speed and security are like oil and water, you’re right.

AIIM
MARCH 31, 2020
Many of us find ourselves working from home – often rather suddenly and unexpectedly. Organizations of all sizes and in all industries are now in the position of figuring out how to ensure that the business of the business continues while staff stay home and practice effective social distancing. The good news is that the technology needed for effective working from home exists and is generally mature – though some providers have found that the sudden surge in volume can cause issues with particu
Krebs on Security
MARCH 30, 2020
In 2018, KrebsOnSecurity unmasked the creators of Coinhive — a now-defunct cryptocurrency mining service that was being massively abused by cybercriminals — as the administrators of a popular German language image-hosting forum. In protest of that story, forum members donated hundreds of thousands of euros to nonprofits that combat cancer (Krebs means “cancer” in German).

Data Breach Today
APRIL 1, 2020
Strangers Could Start a Chat with Someone Using Same Email Domain Popular teleconferencing software Zoom is continuing to fall under scrutiny as questions are raised over its privacy and security practices. The latest issue: a feature that inadvertently reveals strangers' email addresses and profile photos.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

IT Governance
APRIL 2, 2020
With organisations across the globe turned upside down by the COVID-19 pandemic, there has never been a worse time to suffer a data breach or cyber attack. And the bad news is that unsettled employees, many of whom are being asked to work from home, and depleted workforces mean there is an increased chance of an incident occurring. Thankfully, we’ve only found 67 incidents this month, with a total of 832,486,418 affected records – which is only slightly higher than last month’s figures.

AIIM
APRIL 2, 2020
The show Star Trek always had the coolest futuristic technology. For example, I can’t tell you how many times I’ve wished I could tell Scotty to “Beam me up!” and be teleported back home. Another thing that really caught my eye on that show was their “universal translator.” It was basically this handheld device that allowed you to easily communicate across any language – be it human or alien!

erwin
APRIL 3, 2020
Many organizations start an enterprise architecture practice without a specialized enterprise architecture tool. Instead, they rely on a blend of spreadsheets, Visio diagrams, PowerPoint files and the like. Under normal circumstances, this approach is difficult. In times of rapid change or crisis, it isn’t viable. Four Compelling Reasons for An Enterprise Architecture Tool.

Data Breach Today
MARCH 30, 2020
Will Hacking Incidents, Other Breaches Continue to Rise During COVID-19 Pandemic? The total number of health data breaches - and individuals affected - on the 2020 tally has more than doubled in recent weeks. Here are the details.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Security Affairs
MARCH 30, 2020
Security experts uncovered a new Coronavirus-themed phishing campaign, the messages inform recipients that they have been exposed to the virus. Experts continue to spot Coronavirus-themed attack, a new phishing campaign uses messages that pretend to be from a local hospital informing the victims they have been exposed to the virus and that they need urgently to be tested.

Jamf
APRIL 2, 2020
With 48 hours notice, the faculty of the Sewanhaka Central High School District completely re-imagined education. They are teaching students from their living rooms. They are providing counseling sessions, and the essential services for special education and ELL students, entirely online. Read how Sewanhaka realized a goal they previously thought "unimaginable".

OpenText Information Management
MARCH 31, 2020
All the major examples of supply chain disruptions over the previous 20 years – from the SARS epidemic to the Fukushima earthquake and tsunami – have led to the development of new levels of supply chain risk management. However, the lessons learned about the vulnerabilities in global supply chains from these events can’t easily be … The post How to adapt to supply chain disruptions caused by the Coronavirus appeared first on OpenText Blogs.

Data Breach Today
MARCH 31, 2020
Wide Variety of Personal Information Exposed Marriott acknowledged Tuesday that a recent data breach exposed the personal records of millions of hotel guests. It's the second major breach reported by the hotel giant in two years.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

erwin
MARCH 30, 2020
Data intelligence has a critical role to play in the supercomputing battle against Covid-19. Last week, The White House announced the launch of the COVID-19 High Performance Computing Consortium , a public-private partnership to provide COVID-19 researchers worldwide with access to the world’s most powerful high performance computing resources that can significantly advance the pace of scientific discovery in the fight to stop the virus.
Security Affairs
APRIL 3, 2020
Bad news for Apple iPhone or MacBook users, attackers could hack their device’s camera by tricking them into visiting a website. The ethical hacker Ryan Pickren demonstrated that it is possible to hack Apple iPhone or MacBook users by simply tricking them into visiting a website with the Safari browser. Pickren reported seven vulnerabilities to Apple that rewarded him with a $75,000 bounty.

Threatpost
APRIL 1, 2020
The zero-day Zoom flaws could give local, unprivileged attackers root privileges, and allow them to access victims’ microphone and camera.
Data Breach Today
MARCH 31, 2020
Remote Desktop Protocol: Experts See No Apocalypse, But Urge Better Defenses As the coronavirus drives a massive upsurge in remote working, a review of remote desktop protocol usage suggests RDP adoption hasn't spiked. But as IT teams rely more heavily on remote access, experts warn that too many RDP systems remain internet-exposed.

Speaker: Nicholas Zeisler, CX Strategist & Fractional CXO
The first step in a successful Customer Experience endeavor (or for that matter, any business proposition) is to find out what’s wrong. If you can’t identify it, you can’t fix it! 💡 That’s where the Voice of the Customer (VoC) comes in. Today, far too many brands do VoC simply because that’s what they think they’re supposed to do; that’s what all their competitors do.

Dark Reading
APRIL 1, 2020
To keep users and networks healthy and secure, security teams need to mimic countries that have taken on COVID-19 with a rapid, disciplined approach.
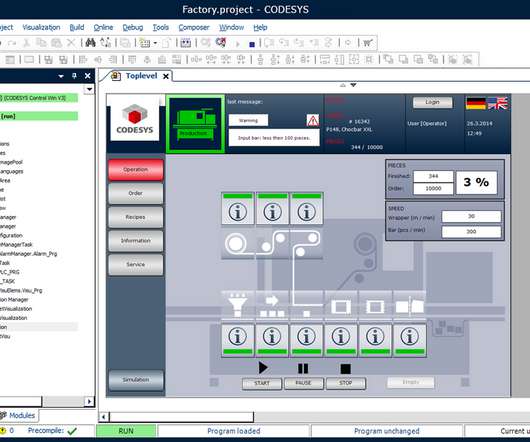
Security Affairs
MARCH 28, 2020
Experts discovered an easily exploitable heap-based buffer overflow flaw, tracked as CVE-2020-10245, that exists in the CODESYS web server. A critical heap-based buffer overflow flaw in a web server for the CODESYS automation software for engineering control systems could be exploited by a remote, unauthenticated attacker to crash a server or execute arbitrary code.
Micro Focus
APRIL 1, 2020
COBOL’s 60th anniversary has seen an unprecedented level of conversation about the world’s most long-standing business language. This exclusive blog sees Dutch COBOL legend, Wim Ebbinkhuijsen, share his story about the language, in an interview with our own Derek Britton. At a recent COBOL community event in the Netherlands, the assembled group of nearly 100.
Let's personalize your content