US Banning TikTok, WeChat Downloads
Data Breach Today
SEPTEMBER 18, 2020
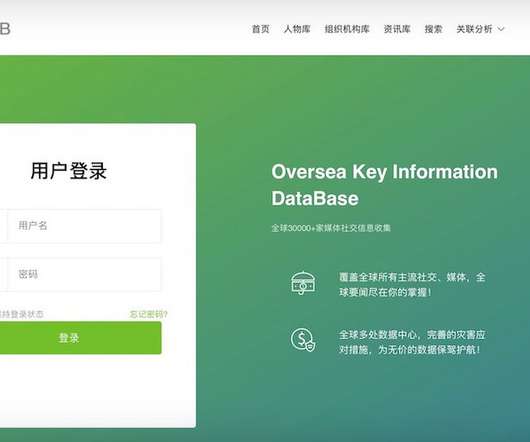
Commerce Department Says Social Media Apps Pose National Security Threat The U.S. Commerce Department is banning the downloading and hosting of China-based social media apps TikTok and WeChat effective on Sunday, citing national security concerns. The announcement comes as Oracle continues to negotiate a deal for partnering on TikTok's U.S. operations.






































Let's personalize your content