Hidden Costs of a Data Breach
Dark Reading
FEBRUARY 22, 2022
Don't consider just the initial costs. Hidden factors include remediation, revenue loss, reputational harm, national security — even human life.

Dark Reading
FEBRUARY 22, 2022
Don't consider just the initial costs. Hidden factors include remediation, revenue loss, reputational harm, national security — even human life.

Krebs on Security
FEBRUARY 22, 2022
Missouri Governor Mike Parson made headlines last year when he vowed to criminally prosecute a journalist for reporting a security flaw in a state website that exposed personal information of more than 100,000 teachers. But Missouri prosecutors now say they will not pursue charges following revelations that the data had been exposed since 2011 — two years after responsibility for securing the state’s IT systems was centralized within Parson’s own Office of Administration.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
FEBRUARY 24, 2022
A reported loss of $171 Million. Huge sum, right? Related: Supply-chain hacks prove worrisome. Yes, and that is what Sony exactly lost when they were hacked and the personal info of every one of its customers leaked in 2011. This came to the news because Sony is one of the biggest names on the planet. Every second, even while you are reading this article, a hacker is trying to hack a site.
IT Governance
FEBRUARY 22, 2022
Information security management is a way of protecting an organisation’s sensitive data from threats and vulnerabilities. The process is typically embedded via an ISMS (information security management system) , which provides the framework for managing information security. At the centre of the framework is information risk management in, which organisations assess risks and the ways that they can compromise the confidentiality, integrity and availability of information.

Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

Security Affairs
FEBRUARY 19, 2022
The U.S. CISA has created a list of free cybersecurity tools and services that can help organizations increase their resilience. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) announced this week that it has compiled a list of free cybersecurity tools and services that can help organizations to reduce cybersecurity risk and increase resilience.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

eSecurity Planet
FEBRUARY 23, 2022
How can a hospital protect an MRI machine with an unchangeable password and still connect it to the network? How can an industrial recycler safely secure its $400,000 hard drive recertification rack with control software that only runs on Windows XP? These are not uncommon risks. The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks.

OpenText Information Management
FEBRUARY 22, 2022
The last two years have forced companies and organizations of all sizes to reassess their processes and operational methods and to change their mindset about how best to operate as a business. For OpenText, that has meant doubling down on the product innovations that allow people to reimage how and where they work, how goods … The post Announcing OpenText Cloud Editions 22.1 appeared first on OpenText Blogs.
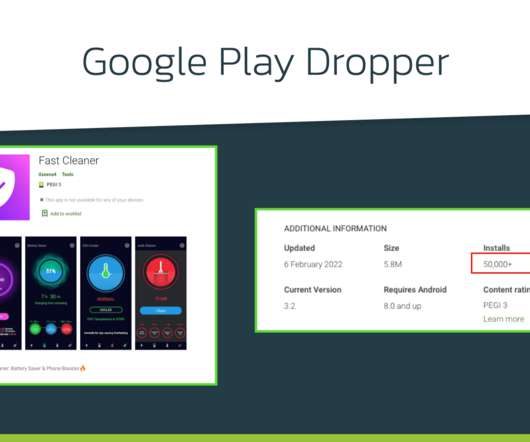
Security Affairs
FEBRUARY 21, 2022
Xenomorph Android trojan has been observed distributed via the official Google Play Store targeting 56 European banks. Researchers from ThreatFabric have spotted a new Android banking trojan, dubbed Xenomorph , distributed via the official Google Play Store that has over 50,000 installations. The banking Trojan was used to target 56 European banks and steal sensitive information from the devices of their customers.
Hunton Privacy
FEBRUARY 22, 2022
On February 14, 2022, Noom Inc., a popular weight loss and fitness app, agreed to pay $56 million, and provide an additional $6 million in subscription credits to settle a putative class action in New York federal court. The class is seeking conditional certification and has urged the court to preliminarily approve the settlement. The suit was filed in May 2020 when a group of Noom users alleged that Noom “actively misrepresents and/or fails to accurately disclose the true characteristics of its

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Data Matters
FEBRUARY 25, 2022
WEBINAR. 4:00 p.m. – 5:30 p.m. GMT | 11:00 a.m. – 12:30 p.m. EST. Sidley and OneTrust DataGuidance are pleased to announce that registration is now open for their annual Data Protection in Financial Services (DPFS) Week. Join us from February 28 – March 3 for DPFS Week 2022 , a series of webinars looking at the impacts of data privacy across the financial sector.
Troy Hunt
FEBRUARY 24, 2022
I feel the need, the need for speed. Faster, Faster, until the thrill of speed overcomes the fear of death. If you're in control, you're not going fast enough. And so on and so forth. There's a time and a place for going fast, and there's no better place to do that than when querying Have I Been Pwned's Pwned Passwords service.

Schneier on Security
FEBRUARY 23, 2022
A Berlin-based company has developed an AirTag clone that bypasses Apple’s anti-stalker security systems. Source code for these AirTag clones is available online. So now we have several problems with the system. Apple’s anti-stalker security only works with iPhones. (Apple wrote an Android app that can detect AirTags, but how many people are going to download it?

Security Affairs
FEBRUARY 24, 2022
Cybersecurity experts discovered a new data wiper malware that was used in attacks against hundreds of machines in Ukraine. The threat of hybrid warfare is reality, Russia-linked APT group have supported the operations of the Russian army while preparing for the invasion. Researchers from cybersecurity firms ESET and Broadcom’s Symantec discovered a new data wiper malware that was employed in a recent wave of attacks that hit hundreds of machines in Ukraine.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Jamf
FEBRUARY 25, 2022
Supercharge your school’s Apple device and data management with Apple School Manager, Managed Apple IDs, automation enabled by Jamf and integration with Claris Connect.

eSecurity Planet
FEBRUARY 23, 2022
The Great Resignation has left many companies reeling, experiencing a higher turnover rate than ever before. And while this is causing major problems for HR, it could also lead to underlying security issues. Employees carry with them a lot of knowledge about how to access company systems, and that knowledge doesn’t just go away when they leave. Around 58 percent of IT and security professionals are concerned about the knowledge former employees have about accessing company infrastructure.

Schneier on Security
FEBRUARY 22, 2022
The US National Cyber Director Chris Inglis wrote an essay outlining a new social contract for the cyber age: The United States needs a new social contract for the digital age — one that meaningfully alters the relationship between public and private sectors and proposes a new set of obligations for each. Such a shift is momentous but not without precedent.
Security Affairs
FEBRUARY 23, 2022
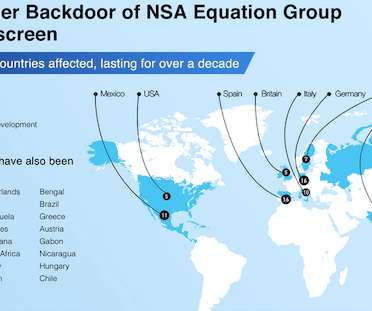
Pangu Lab researchers disclosed details of the Bvp47 backdoor that was used by the US NSA Equation Group. Researchers from The China’s Pangu Lab have disclosed details of a Linux top-tier APT backdoor, tracked as Bvp47, which is associated with the U.S. National Security Agency (NSA) Equation Group. The name “ Bvp47 ” comes form numerous references to the string “Bvp” and the numerical value “0x47” used in the encryption algorithm.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
Hanzo Learning Center
FEBRUARY 24, 2022
Prognostications and predictions are inherently flawed. Does anyone really believe Punxsutawney Phil is a reliable weather forecaster? And how many of us, in our predictions of what would happen in legal technology in 2020, anticipated that a global pandemic would temporarily bring society to a halt? We sure didn’t.
eSecurity Planet
FEBRUARY 21, 2022
Quick response (QR) codes are a convenient format for storing all kinds of information in a readable and secure way, at least when correctly implemented. With the ongoing COVID-19 pandemic, for example, governments have recently implemented QR codes to create Digital COVID Certificates for vaccination, tests status and other reasons. QR technology isn’t new, and security features like two-factor authentication (2FA) or multi-factor authentication (MFA) often invite users to generate such c

Dark Reading
FEBRUARY 25, 2022
Ukraine's Computer Emergency Response Team calls out UNIC1151 nation-state hacking group out of Belarus as behind the attacks.

Security Affairs
FEBRUARY 25, 2022
The popular collective Anonymous declared war on Russia for the illegitimate invasion of Ukraine and announced a series of cyber attacks calling to action its members. The Anonymous collective is calling to action against Russia following the illegitimate invasion of Ukraine. The famous groups of hackivists is also calling for action Russian citizens inviting them to express their dissent to Putin. “The Anonymous collective is officially in” cyber war “against the Russian gover

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

DLA Piper Privacy Matters
FEBRUARY 22, 2022
Authors: Denise Lebeau-Marianna & Divya Shanmugathas. The French Supervisory Authority (the “ CNIL ”) regularly conducts investigations based on various triggering events such as a complaint, an article or its annual program that the CNIL regularly publishes on its website. On 15 February 2022, published a post regarding its upcoming dawn raids for 2022.

eSecurity Planet
FEBRUARY 25, 2022
Many cybersecurity audits now ask whether penetration testing is conducted and how vulnerabilities are detected and tracked. These questions ask IT teams to consider how frequently security is tested from the outside via penetration testing and from the inside via vulnerability testing. That right there – inside vs. outside – should give you a good idea of a key difference between the tests, but for those who don’t spend their days performing compliance audits, the difference between these two t

Dark Reading
FEBRUARY 25, 2022
A lot of the recommended preparation involves measures organizations should have in place already.

Security Affairs
FEBRUARY 25, 2022
The CERT of Ukraine (CERT-UA) warned of a spear-phishing campaign targeting Ukrainian armed forces personnel. The Computer Emergency Response Team of Ukraine (CERT-UA) is warning of an ongoing spear-phishing campaign targeting private email accounts belonging to Ukrainian armed forces personnel. The Ukrainian agency attributes the campaign to the Belarus-linked cyberespionage group tracked as UNC1151.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Schneier on Security
FEBRUARY 24, 2022
The story is an old one, but the tech gives it a bunch of new twists : Gemma Brett, a 27-year-old designer from west London, had only been working at Madbird for two weeks when she spotted something strange. Curious about what her commute would be like when the pandemic was over, she searched for the company’s office address. The result looked nothing like the videos on Madbird’s website of a sleek workspace buzzing with creative-types.
eSecurity Planet
FEBRUARY 22, 2022
Most attacks make would-be victims click to install malware or redirect them to a phishing page to steal their credentials. Zero-click attacks remove this hurdle. They can compromise the targeted device despite a victim’s good security hygiene and practices. There is no need for social engineering , as the program can implant backdoors directly without forced consent.
Hunton Privacy
FEBRUARY 23, 2022
On February 18, 2022, the Texas Attorney General’s Office (the “Texas AG”) announced that it had issued two Civil Investigative Demands (“CIDs”) to TikTok Inc. The Texas AG’s investigation focuses on TikTok’s alleged violations of children’s privacy and facilitation of human trafficking, along with other potential unlawful conduct. In relevant part, the CIDs seek information and documents related to TikTok’s policies and practices with respect to how the company identifies, addresses and prevent
Let's personalize your content