Video Game Streamer 'Twitch' Confirms Massive Data Breach
Data Breach Today
OCTOBER 6, 2021
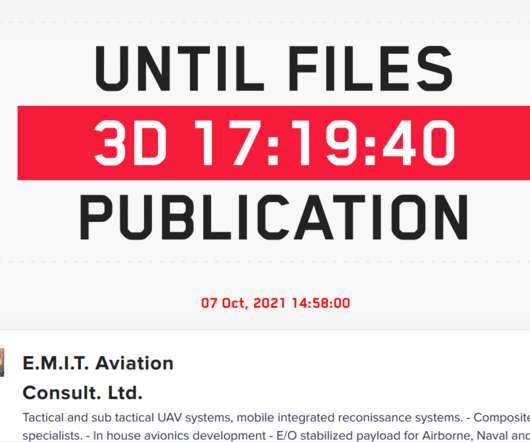
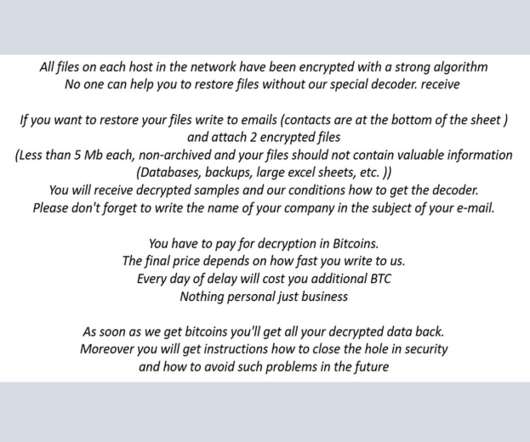
Reports: Platform's Entire Source Code Compromised in 125GB Leak Amazon-owned video streaming service Twitch, which focuses on video games and e-sports broadcasts, reportedly suffered a massive data breach, which the company vaguely confirmed via Twitter. A post on the anonymous online forum 4chan reportedly indicates that the entire platform was compromised.

































Let's personalize your content