Attackers continued to favor software exploits, phishing, and stolen credentials as initial-access methods last year, as Log4j and the Russia-Ukraine cyber conflict changed the threat landscape.
April 19, 2023

Popular attacks for a trio of critical vulnerabilities kept exploitation at the top of the list of initial-access methods in 2022, while the war between Russia and Ukraine resulted in an unprecedented volume of attacks from a specific group of threat actors.
That's according to the annual M-Trends report from Google Cloud's Mandiant, published on April 18, which highlights that a few global incidents can dramatically affect the overall threat landscape.
The volume of attacks used in the Russia-Ukraine conflict, for example, resulted in the government sector's rise to the top of the list of targeted industries, accounting for 25% of all attacks investigated by Mandiant, up from 9% in 2021, when government agencies ranked sixth on the list. Meanwhile, about 36% of incidents investigated by Mandiant included the use of software exploits, with four out of every nine of those attacks targeting a vulnerable version of Log4j, the open source logging library.
Significant events — such as the Log4j patch effort — can have massive, albeit temporary, effects on the threat landscape, says Luke McNamara, a principal analyst with Mandiant.
"You have this ... massive spike in these methods as the initial infection vector, but a lot of it was ... the impact of one singular incident," he says, comparing the impact to the surge in supply chain attacks in 2021 due to the compromise of SolarWinds. "It's not necessarily indicative that this is going to be a large-scale trend that we're gonna see more and more of, but just something that impacts the threat activity for that given year."
Similarly, Russia's war against Ukraine had a dramatic impact on the threat landscape for more than year, Google Cloud stated in the report. A cyber-espionage group, UNC2589, and another group linked to Russian military intelligence, APT28, conducted extensive information collection and disinformation operations prior to Russia's February 2022 invasion of Ukraine. Now the threat groups appear to alternate information gathering and espionage campaigns with destructive attacks.
In the first four months of the war, the Mandiant group recorded more destructive attacks against Ukrainian organizations than in the previous eight years, according to the report.
"The invasion of Ukraine represents one of the first instances in which a major cyber power has conducted disruptive attacks, espionage, and information operations concurrently with widespread, kinetic military operations," the Mandiant report stated. "Mandiant has never observed threat actor activity that matches the volume of attacks, variety of threat actors, and coordination of effort as was seen during the first months following the invasion by Russia."
A Few Good Flaws
Those attacks — and the threat landscape more generally — relied on a handful of initial access methods. Overall, 80% of the incidents investigated by Mandiant typically used a software exploit, phishing attacks, stolen credentials, or leveraged a prior compromise, the report stated. The exploitation of known vulnerabilities was the most popular initial access vector, accounting for 32% of incidents where the initial compromise could be determined, while phishing accounted for 22% and stolen credentials for 14%.
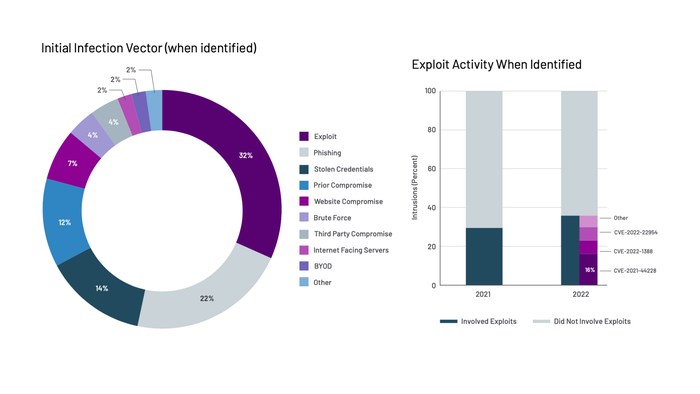
Exploits accounted for about a third of initial attacks, with more than 80% enabled by three vulnerabilities. Source: M-Trends 2023
Among exploits, three vulnerabilities made up the lion's share of the attacks. The primary vulnerability in Log4j (CVE-2021-44228) accounted for the largest portion (44%) of known exploits, but along with two other vulnerabilities — one affecting F5's Big-IP (CVE-2022-1388) and another affecting VMware's Workspace One Access and Identity Manager (CVE-2022-22954) — the trio accounted for nearly 90% of exploits.
Because all three vulnerabilities are often accessible remotely, attackers scan for them regularly, McNamara says.
"Targeting and exploiting perimeter devices that are accessible via the internet — things like firewalls, virtualization solutions, VPN — those are highly sought after targets for attackers," he says. "We saw this with Ukraine because [threat groups] leverage a lot kind of 'living on the edge,' as we put it, where they've used edge and perimeter network devices to come back in when they've been kicked out multiple times from a given organization."
More External Detections, Less Dwell Time
In another trend, the share of incidents discovered internally shrank in 2022, with 37% incidents detected by the targeted company and 63% of incidents disclosed to the target by a third party. The share of incidents not detected by a company's internal security teams has grown in every geography, slowly in the Americas, but much more quickly in the Asia-Pacific region (APAC) and the Europe, Middle East, and Africa (EMEA) regions.
Yet despite the more significant role played by third parties in attack detection, dwell time has decreased to 16 days in 2022, down from 21 in 2021. The debate is whether the decrease is due to defenders detecting attacks more quickly or attackers ending an attack with a destructive — and obvious — payload, Google Cloud's McNamara says.
"Really, the last two, three, four years, we've seen more and more disruptive activity, as the extortion space has become more multifaceted," he says. "Trying to kind of tease out how much of that is due to organizational maturity — organizations are getting better at catching threat actors — and how much of it is due to ... the nature of the activity itself is difficult."
However, while the median dwell time is 16 days, ransomware investigations are only seeing a median dwell time of nine days, whereas it's 17 days for non-ransomware investigations.
The cyber conflict between Russia and Ukraine also impacted the dwell time, according to Mandiant's report, as external intelligence agencies and companies notified Ukrainian organizations of breaches.
"The increase in external notification observed in 2022 is likely impacted by Mandiant’s investigative support of cyber threat activity which targeted Ukraine and an increase in proactive notification efforts," the report stated. "Proactive notifications from security partners enable organizations to launch response efforts more effectively."
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




