Insights about the first five years of Right to be Forgotten requests at Google
Elie
DECEMBER 12, 2019
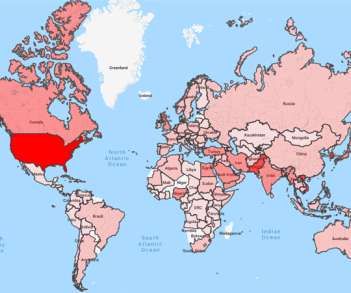
The. “Right to be Forgotten” (RTBF). is a landmark European ruling that governs the delisting of personal information from search results. This ruling establishes a right to privacy, whereby individuals can request that search engines delist URLs across the Internet that contain “inaccurate, inadequate, irrelevant or excessive” information uncovered by queries containing the name of the requester.

































Let's personalize your content