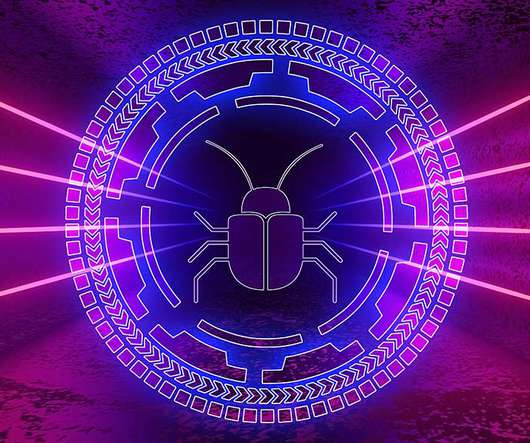
Buer Dropper Malware Updated Using Rust
Data Breach Today
MAY 3, 2021
Proofpoint: New Code Makes 'RustyBuer' Version Harder to Detect Attackers are using a freshly updated variant of the Buer first-stage malware loader rewritten in the Rust programming language to help evade detection, Proofpoint reports.


































Let's personalize your content